
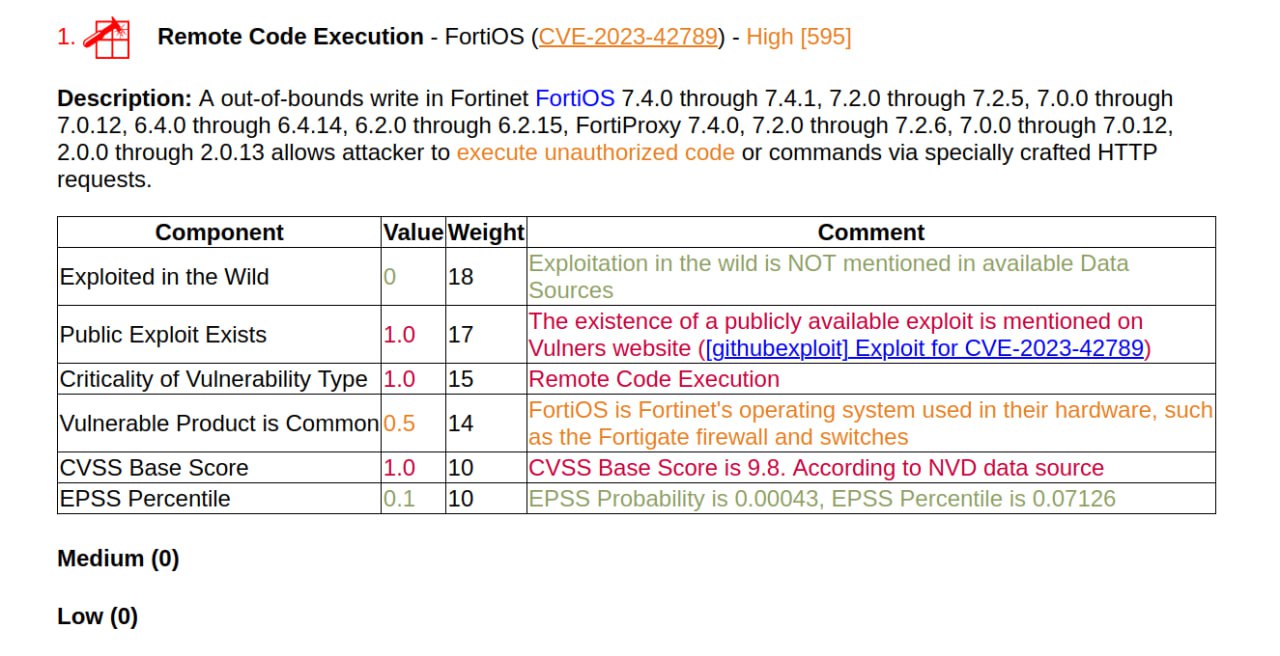
Recently there was news about an RCE vulnerability in FortiOS and FortiProxy (CVE-2023-42789). It “allows attacker to execute unauthorized code or commands via specially crafted HTTP requests”. The vulnerability is exploited in the captive portal, which, in theory, should not be accessible from the Internet. This is why the Fortinet bulletin warns about an “inside attacker”.
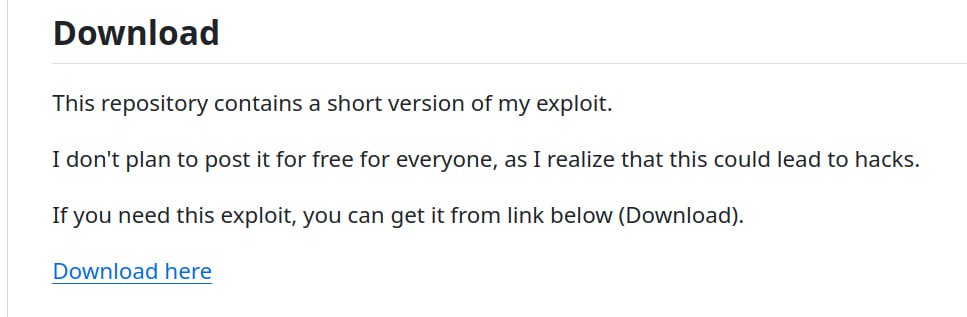
There is a repository on GitHub that allegedly contains a PoC, but its reliability is questionable. The code only implements checking the availability of the captive portal; there is no payload there. The repository was created by a user without any reputation or previous activity. He sells the full exploit code for ~$262. It looks like a scam, but if suddenly this is a truly functional exploit, then it is likely that it will quickly leak to the public.
In any case, it is worth updating or getting rid of this solution.

Hi! My name is Alexander and I am a Vulnerability Management specialist. You can read more about me here. Currently, the best way to follow me is my Telegram channel @avleonovcom. I update it more often than this site. If you haven’t used Telegram yet, give it a try. It’s great. You can discuss my posts or ask questions at @avleonovchat.
А всех русскоязычных я приглашаю в ещё один телеграмм канал @avleonovrus, первым делом теперь пишу туда.

