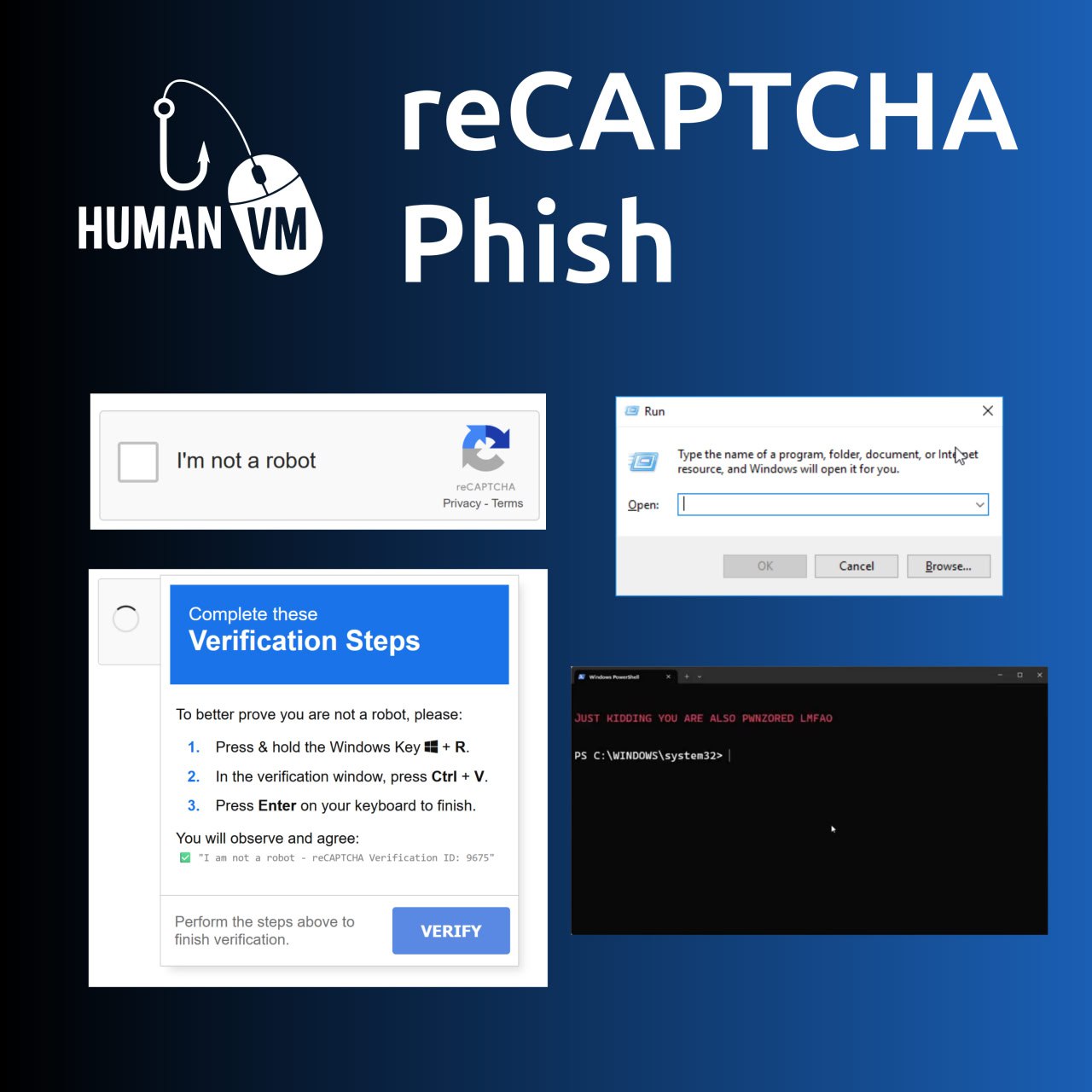
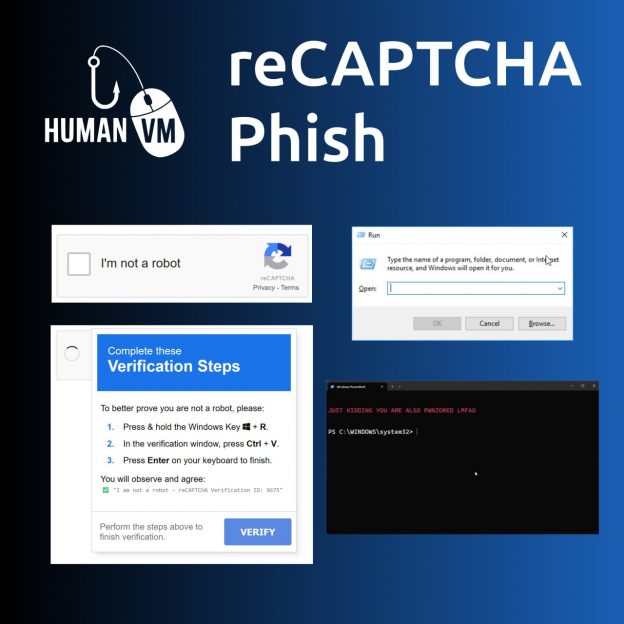
Fake reCAPTCHA. Probably the most interesting example of exploitation of human vulnerability in the last month. This trick works for two reasons:
🔹 Various captcha services have taught people to do the strangest things: click on pictures with certain content, retype words, solve some puzzles. Many people do not even think when they see another window “prove that you are not a robot” and just do what they are asked. 🤷♂️
🔹 Websites have the ability to write arbitrary text to the site visitor’s clipboard. 😏
Fake captcha asks the user to launch the Run window in Windows (Win + R), then paste a malicious command from the clipboard into this window (Ctrl + V) and run the command (Enter). Very primitive, but it works! 🤩 This is how attackers trick victims into running malicious PowerShell scripts and HTA applications. 👾
John Hammond recreated the code of such a “captcha”. You can use it in anti-phishing training.

Hi! My name is Alexander and I am a Vulnerability Management specialist. You can read more about me here. Currently, the best way to follow me is my Telegram channel @avleonovcom. I update it more often than this site. If you haven’t used Telegram yet, give it a try. It’s great. You can discuss my posts or ask questions at @avleonovchat.
А всех русскоязычных я приглашаю в ещё один телеграмм канал @avleonovrus, первым делом теперь пишу туда.

Pingback: September episode of “In The Trend of VM”: 7 CVEs, fake reCAPTCHA, lebanese pagers, VM and IT annual bonuses | Alexander V. Leonov