
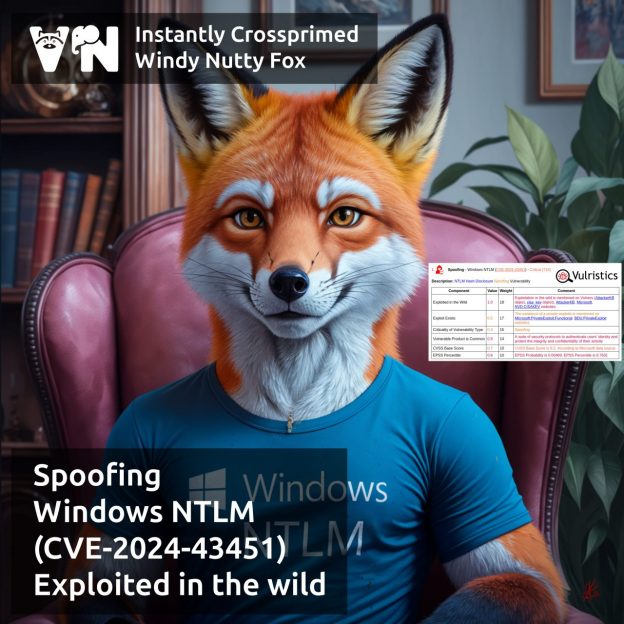
About Spoofing – Windows NTLM (CVE-2024-43451) vulnerability. The vulnerability is from the November Microsoft Patch Tuesday. It immediately showed signs of being exploited in the wild. The vulnerability is related to the outdated MSHTML platform, which is still used in Windows. To exploit the vulnerability, the user must minimally interact with the malicious URL file: right-click on it, delete it, or move it to another folder. There is no need to open the malicious file. As a result, the attacker receives the user’s NTLMv2 hash, which he can use for authentication.
👾 According to ClearSky, the vulnerability is used to distribute Spark RAT, an open-source remote access Trojan.

Hi! My name is Alexander and I am a Vulnerability Management specialist. You can read more about me here. Currently, the best way to follow me is my Telegram channel @avleonovcom. I update it more often than this site. If you haven’t used Telegram yet, give it a try. It’s great. You can discuss my posts or ask questions at @avleonovchat.
А всех русскоязычных я приглашаю в ещё один телеграмм канал @avleonovrus, первым делом теперь пишу туда.

Pingback: New episode “In The Trend of VM” (#10): 8 trending vulnerabilities of November, zero budget VM and who should look for patches | Alexander V. Leonov