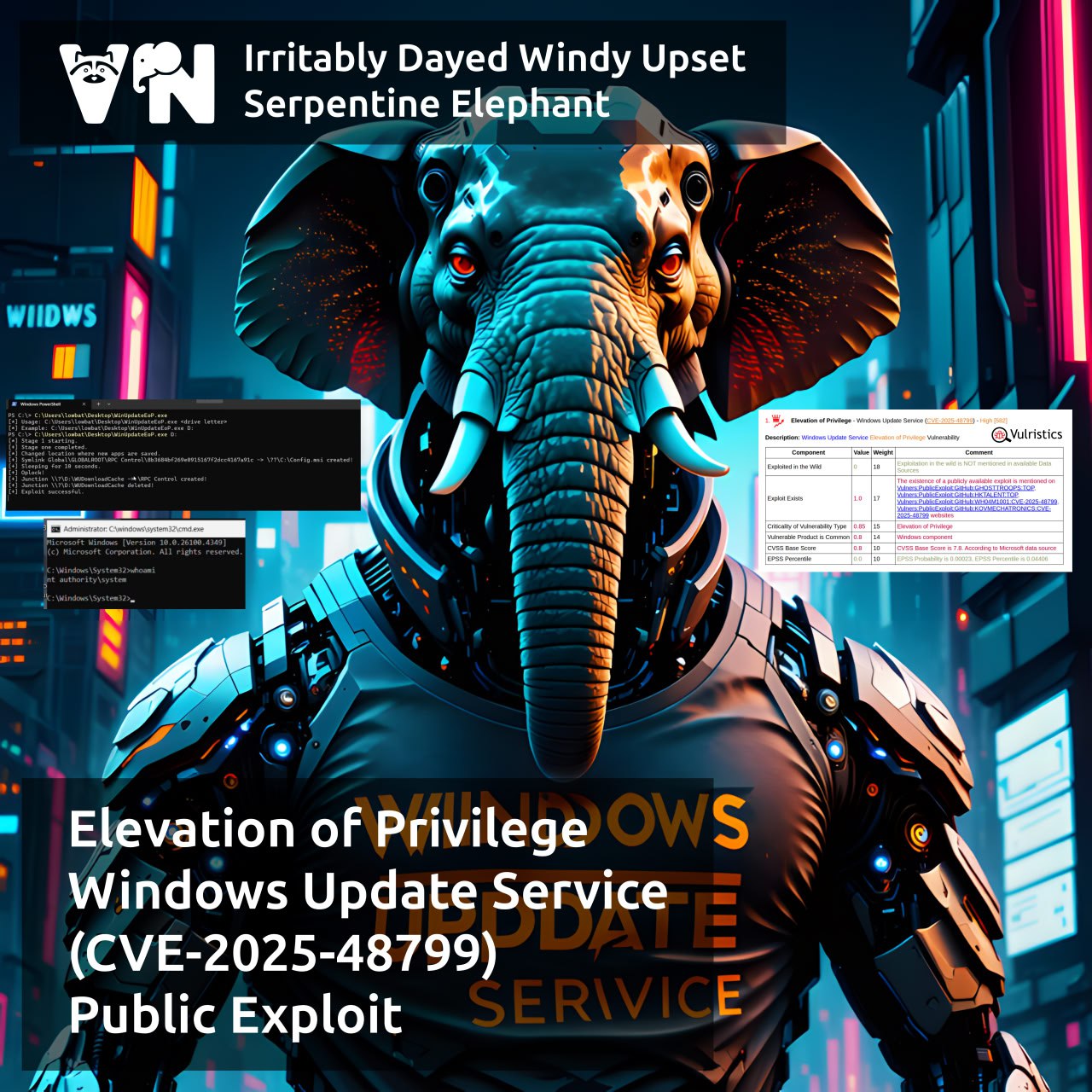
About Elevation of Privilege – Windows Update Service (CVE-2025-48799) vulnerability. This vulnerability is from the July Microsoft Patch Tuesday. Improper link resolution before file access (‘link following’) in the Windows Update Service allows an authorized attacker to elevate privileges to “NT AUTHORITY\SYSTEM”.
🛠 An exploit for this vulnerability was published by researcher Filip Dragović (Wh04m1001) on July 8, the day of MSPT. In the exploit description, he states that the vulnerability affects Windows 10/11 systems with at least two hard drives. If the installation location for new apps is changed to the secondary drive (using Storage Sense), then during the installation of a new app, the wuauserv service will arbitrarily delete folders without checking for symbolic links, leading to to LPE.
🎞 In the demonstration video, Filip Dragović runs the EXE file and gets an administrator console.
👾 No signs of exploitation in the wild yet.

Hi! My name is Alexander and I am a Vulnerability Management specialist. You can read more about me here. Currently, the best way to follow me is my Telegram channel @avleonovcom. I update it more often than this site. If you haven’t used Telegram yet, give it a try. It’s great. You can discuss my posts or ask questions at @avleonovchat.
А всех русскоязычных я приглашаю в ещё один телеграмм канал @avleonovrus, первым делом теперь пишу туда.


Pingback: August “In the Trend of VM” (#18): vulnerabilities in Microsoft Windows and SharePoint | Alexander V. Leonov