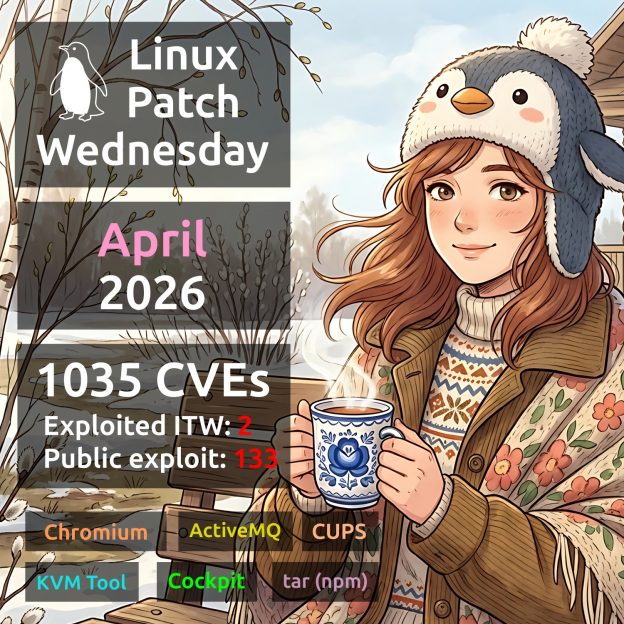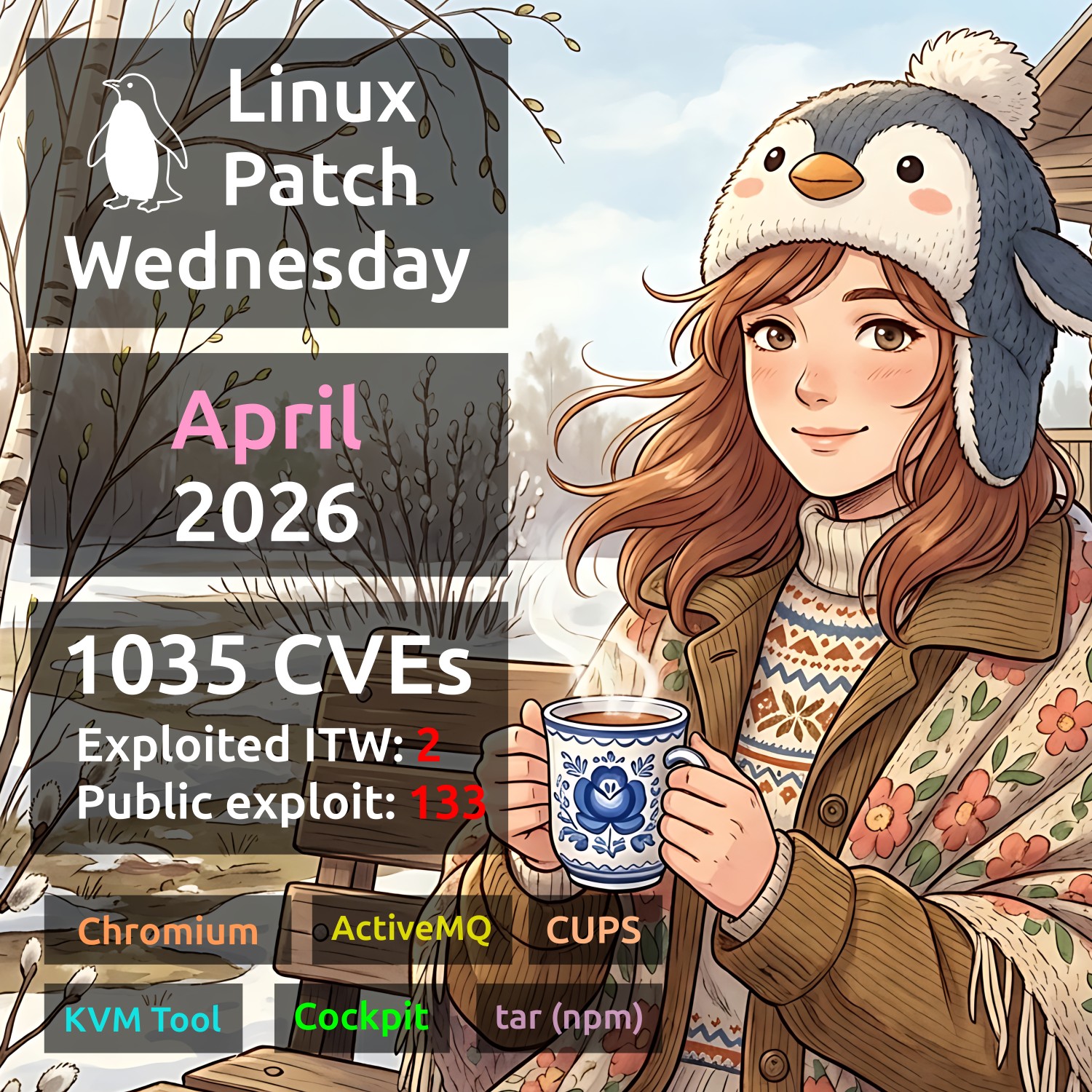
April Linux Patch Wednesday. In April, Linux vendors addressed 1,035 vulnerabilities – nearly twice as many as in March. One might assume that most of these would again be Linux Kernel vulnerabilities, but that’s not the case! Linux Kernel vulnerabilities were relatively few – just 209. The remaining vulnerabilities are distributed across more than 200 affected products. Notably, two vulnerabilities show evidence of active exploitation in the wild:
🔻 RCE – Apache ActiveMQ (CVE-2026-34197). Remote code execution is possible via the Jolokia API (/api/jolokia/) with no authentication required. The vulnerability remained hidden in the codebase for 13 years before being discovered using AI. Listed in the CISA KEV since April 16. Numerous exploits are available on GitHub.
🔻 RCE – Chromium (CVE-2026-5281). A use-after-free vulnerability in Dawn (Chromium’s graphics layer and WebGPU implementation) affects Google Chrome versions prior to 146.0.7680.178. A remote attacker who has gained control of the rendering process can execute arbitrary code via a specially crafted HTML page. Listed in the CISA KEV since April 1.
Public exploits are available, or signs of their existence have been observed, for another 133 (❗️) vulnerabilities. The most notable ones, in my opinion:
🔸 RCE – Cockpit (CVE-2026-4631). Cockpit is a web‑based tool for server administration in Linux systems, enabling users to manage servers, containers, storage, and network configurations through a browser interface. An attacker with network access to the Cockpit web service can send a single HTTP request to the login page, injecting malicious SSH options or commands and executing code on the Cockpit server – all without valid credentials.
🔸 RCE – CUPS (CVE-2026-34990 + CVE-2026-34980). CUPS (Common UNIX Printing System) is a printing system for Unix‑like operating systems, including Linux and macOS. A chain of these vulnerabilities allows a remote attacker without authentication to overwrite files with root permissions over the network, effectively gaining root access on a typical Linux system.
🔸 RCE – KVM Tool (CVE-2021-45464). KVM Tool is a lightweight tool for running virtual machines based on KVM (Kernel‑based Virtual Machine) in Linux. KVM Tool prior to commit 39181fc contains an out‑of‑bounds write vulnerability, allowing a guest OS user to execute arbitrary code on the host machine.
🔸 PathTrav – tar (npm) (CVE-2026-31802, CVE-2026-24842). Prior to version 7.5.11, the npm package allowed creating a symbolic link pointing outside the extraction directory, leading to file overwrites.
Other vulnerabilities worth paying attention to:
🔸 RCE – Handlebars (CVE-2026-33937), tiemu (CVE-2017-20225), Netwide Assembler (CVE-2026-6067), openexr (CVE-2026-34545), Axios (CVE-2026-40175), hdf5 (CVE-2026-29043)
🔸 CodeInj – GLPI (CVE-2025-66417), glances (CVE-2026-30930, CVE-2026-32611), Handlebars (CVE-2026-33938, CVE-2026-33940), dynaconf (CVE-2026-33154), icalendar (CVE-2026-33635)
🔸 SFB – ormar (CVE-2026-27953), cpp-httplib (CVE-2026-34441), Safari (CVE-2026-20643), rack (CVE-2026-34835), wolfssl (CVE-2026-5194), Traefik (CVE-2026-32695), glances (CVE-2026-32632, CVE-2026-32634), Vert.x-Web (CVE-2026-1002), ecdsa (CVE-2026-33936), glibc (CVE-2026-4438), incus (CVE-2026-33542), Mongoose (CVE-2026-2968)
🔸 AuthBypass – scitokens_cpp_library (CVE-2026-32725, CVE-2026-32726), Node.js pbkdf2 (CVE-2026-32633), rack-session (CVE-2026-39324), Traefik (CVE-2026-33433), grpc (CVE-2026-33186), nltk (CVE-2026-33231)
🔸 ArbFileWrite – Rust (CVE-2026-33056)
🔸 CmdInj – Netty (CVE-2026-33870), awstats (CVE-2025-63261)
🔸 EoP – Keycloak (CVE-2026-4636), QEMU (CVE-2026-33711), glances (CVE-2026-33641)