Last Week’s Security news: Cisco ASA, BIG-IQ, vSphere, Solaris, Dlink, iPhone %s, DarkRadiation, Google schema, John McAfee. Hello, today I want to experiment with a new format. I will be reading last week’s news from my @avleonovnews channel, which I found the most interesting. I do this mostly for myself, but if you like it too, then that would be great. Please subscribe to my YouTube channel and my Telegram @avleonovcom.
Let’s start with some new public exploits.
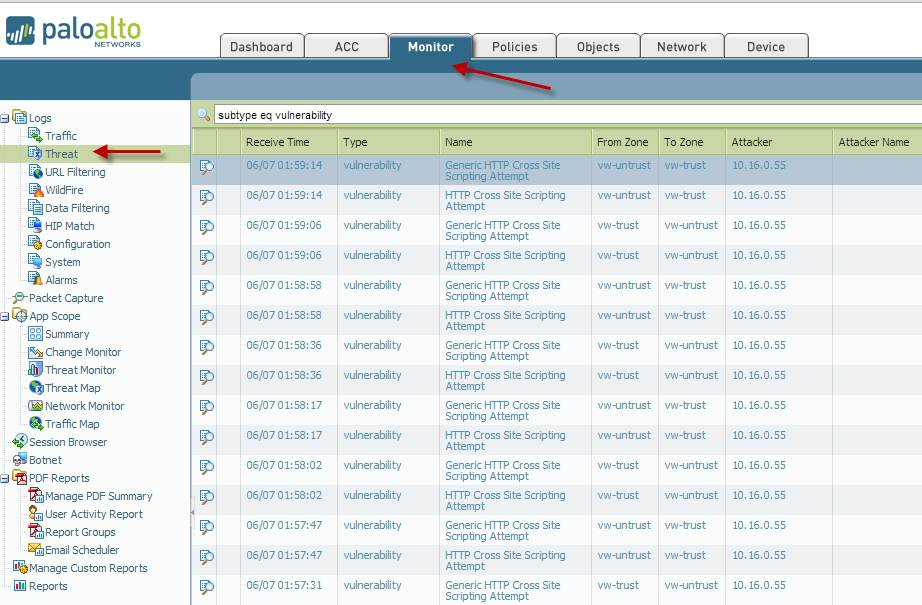
- Researchers at Positive Technologies have dropped a proof-of-concept (PoC) exploit on Twitter for a known cross-site scripting (XSS) vulnerability in the Cisco Adaptive Security Appliance (ASA) CVE-2020-3580. This flaw was patched in October. There are reports of researchers pursuing bug bounties using this exploit. Maybe you should do this too. Well, or at least ask your IT administrators if they have updated the ASA.
- F5 BIG-IQ VE Post-auth Remote Root RCE. BIG-IQ provides a single point of management for all your BIG-IP devices — whether they are on premises or in a public or private cloud. It was possible to execute commands with root privileges as an authenticated privileged user via command injection in easy-setup-test-connection. A good reason to check if you have this in the infrastructure. But of course the fact that this is Post-auth makes it less interesting.
- VMware vCenter 6.5 / 6.7 / 7.0 Remote Code Execution. From the description of the vulnerability that was published in February 2021. “The vSphere Client (HTML5) contains a remote code execution vulnerability in a vCenter Server plugin. A malicious actor with network access to port 443 may exploit this issue to execute commands with unrestricted privileges on the underlying operating system that hosts vCenter Server.” Therefore, if your IT colleagues have not patched vCenter since February, you can try to demonstrate how this vulnerability is exploited in practice.
- Solaris SunSSH 11.0 Remote Root. “CVE-2020-14871 is a critical pre-authentication (via SSH) stack-based buffer overflow vulnerability in the Pluggable Authentication Module (PAM) in Oracle Solaris. PAM is a dynamic authentication component that was integrated into Solaris back in 1997 as part of Solaris 2.6”. If you are still using Solaris in your infrastructure, this is a great opportunity to try this exploit.
- Dlink DSL2750U – ‘Reboot’ Command Injection. There, in the exploit code, there is a link to the full study that shows how the researcher, Mohammed Hadi, gains admin access to the router. This is interesting considering that this router model is quite popular and you can still buy such a router.
- It’s 2021 and a printf format string in a wireless network’s name can break iPhone Wi-Fi. On Friday, Carl Schou, a security researcher in Denmark, reported that his iPhone lost its Wi-Fi capability after attempting to connect to a Wi-Fi network named “%p%s%s%s%s%n”. Fortunately, the damage appears not to be permanent. Apple iOS devices that lose Wi-Fi capability after being bitten by this bug can be restored via the General -> Reset -> Reset Network Settings menu option, which reverts network settings to their factory default. Not a very interesting vulnerability in terms of practical exploitation, but fun. Don’t connect to unfamiliar Wi-Fi networks.