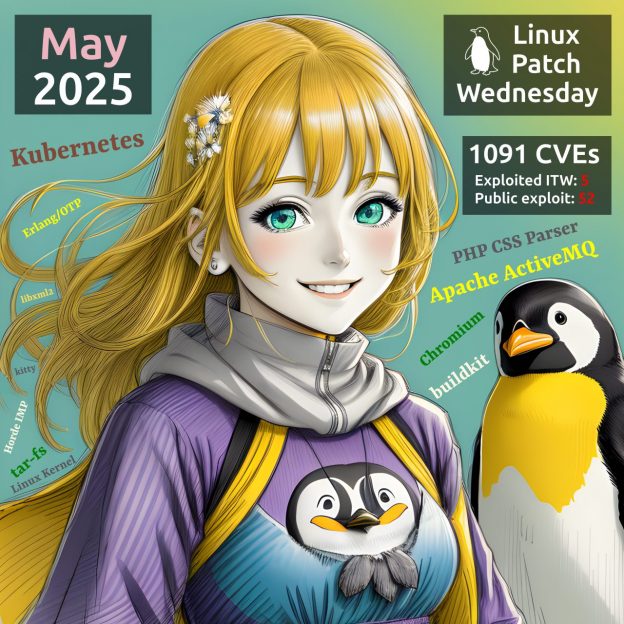
May Linux Patch Wednesday. This time: 1091 vulnerabilities. Of those, 716 are in the Linux Kernel. 🤯 5 vulnerabilities are exploited in the wild:
🔻 RCE – PHP CSS Parser (CVE-2020-13756). In AttackerKB, an exploit exists.
🔻 DoS – Apache ActiveMQ (CVE-2025-27533). In AttackerKB, an exploit exists.
🔻 SFB – Chromium (CVE-2025-4664). In CISA KEV.
🔻 PathTrav – buildkit (CVE-2024-23652) and MemCor – buildkit (CVE-2024-23651). In BDU FSTEC.
For 52 (❗️) more, there are signs of existing public exploits. Two trending vulnerabilities I’ve mentioned before::
🔸 RCE – Kubernetes “IngressNightmare” (CVE-2025-1974 and 4 others)
🔸 RCE – Erlang/OTP (CVE-2025-32433)
Exploits for these are also notable:
🔸 EoP – Linux Kernel (CVE-2023-53033)
🔸 XSS – Horde IMP (CVE-2025-30349)
🔸 PathTrav – tar-fs (CVE-2024-12905)
🔸 SFB – kitty (CVE-2025-43929)
🔸 DoS – libxml2 (CVE-2025-32414)