ISACA Moscow Vulnerability Management Meetup 2018. Last Thursday, September 20th, I spoke at ISACA Moscow “Vulnerability Management” Meetup held at Polytechnic University. The only event in Moscow devoted solely to Vulnerability Management. So I just had to take part in it. 🙂

The target audience of the event – people who implement the vulnerability management process in organizations and the employees of Vulnerability Management vendors. I noticed groups of people from Altex-Soft (Altx-Soft), Positive Technologies and Vulners.

It was very interesting to see such concentration of Vulnerability and Compliance Management specialists in one place. Questions from the audience were relevant and often concerned the weaknesses of competitors. 😉 Here I will make a brief overview of the reports. You can also read here about previous year event at “ISACA Moscow Vulnerability Management Meetup 2017“.
Talking about the audience, there were fewer people than last year, but still a lot:

The event was recorded. I will add video here as soon as it’s ready.
upd. Video in Russian. My presentation starts at 1:35:56
The event was conducted entirely in Russian, including all the slides. So, maybe I will make English subtitles and voiceover, at least for my part.
How to speak with Top management about Vulnerabilities
The first one was Alexander Bodrik, Vice President of ISACA Moscow, with report “Vulnerability Management for the Organizational Leaders”.
He was talking how to communicate with the TOP managers about the vulnerabilities and how to explain why this might concern them.
- For HRD: vulnerability in the Recruiting Portal may allow an attacker to place compromising images -> it will harm the HR brand and create problems with hiring staff.
- For FIN: vulnerability in ERP can cause spreading confidential information about salaries among the staff -> it will be necessary to unexpectedly increase spends on salaries.
- For Business Manager: a Denial of Service vulnerability can affect the ability to provide service according to SLA -> the company will loose customers.
Why do you need to do this? Sometimes it is much easier to have a “sponsor” from the TOPs in order to achieve Vulnerability Remediation. So, there will be a chain:
SOC (vulnerability detection) -> CISO -> TOP -> IT (vulnerability remediation)
During the Q&A session there was a small discussion if it is the most effective way to explain TOP managers the importance of vulnerabilities by showing them potential losses in money. The problem is that each TOP manager can have his own KPIs and interests. Moreover, it would be very difficult to convince them that the risks are real if there have never been (yet) any serious security incidents in the organization.
Zabbix Threat Control
Then Nikolai Samosvat from Qiwi talked about Zabbix Threat Control. This is a plugin for the Zabbix monitoring system developed by Nicholai. His report was called “Non-standard way of monitoring infrastructure for vulnerabilities”.

The idea is that Zabbix can collect the lists of installed software packages from Linux systems. So you can create a plugin that will get vulnerabilities for each package from Vulners Vulnerability Search Engine through the API. And this will work for free. In addition, it is even possible to update the packages directly from Zabbix interface.
In Q&A section there was a question: what if the automated update will break the server? In fact, you can create a special server group in Zabbix and test the updates on it. An interesting practice of Qiwi is that they update one of the nodes in each cluster and if the update was successful (by health checks and autotests), then this update is considered safe enough to be used on all the servers. And if update breaks something, then a special team will deal with it.
In addition, there was a short discussion whether it is too dangerous to send the versions of packages to the remote Vulners server. For such cautious people, Vulners can offer on-premises installations.
SCAP-based Compliance Management solution
After him spoke Zakhar Mikhailov, the Director of Partnerships at Altx-Soft, and his colleague Mikhail Shchelokov from the sales team.
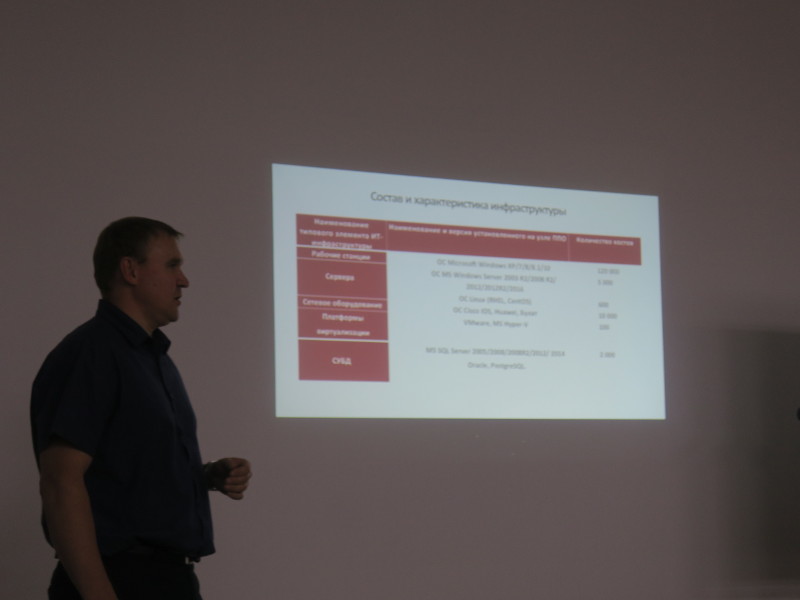
They was talking about their Vulnerability Management product RedCheck, and specifically about it’s compliance mode. The report was called “Beyond compliance – the practical benefit of a certified Russian Vulnerability Management solution.”

They told how they implemented this product in national postal operator Russian Post:
- 120 000 Workstations (Microsoft Windows XP/7/8/8.1/10)
- 5000 Windows Servers (ОС MS Windows Server 2003 R2/2008 R2/)
- 600 Linux Server (RHEL, CentOS)
- 10 000 Network Devices (Cisco IOS, Huawei, Bulat)
- 100 Virtualization Platforms (VMware, MS Hyper-V)
- 2 000 Database Servers (MS SQL Server, Oracle, PostgreSQL)
They developed benchmarks for various operating systems and network devices. Some of them were based on CIS benchmarks, and some were based on vendor’s hardening guides.
I think it is an impressive Compliance Management implementation case. I have not heard anything like this before. And it’s great that we have such local security vendor that can solve Compliance Management tasks using international standards for Security Content, like SCAP. In addition, they also are the leading contributors to CIS Oval Content repository.
The colleagues from Positive Technologies had a question about the mapping of high-level standards (like PCI DSS) to low-level checks of benchmarks and how it was done in RedCheck. I also was doing this for some time, I can say that this is not such a trivial process as it seems.
There were also questions about agent-based scanning (this technology was used in their Russian Post project). There is an opinion that not many users will want to install yet another agent on their systems (you can read about it in my old post “Vulnerability scanners: a view from the vendor and end user side“). But in fact agent-based scanning in RedCheck is just one of the possible options. It is also possible to scan with temporary agents and in agentless mode. And agent-based scanning makes the minimal impact on the systems, so that’s why it was chosen.
Criticizing Vulnerability Management vendors
My report was the final one. I was talking about the stages of Vulnerability Management process, where VM-vendor can’t help customers. At least at the current time. The report was called “Vulnerability management: what you can’t get from VM vendors”.

To put it briefly, I criticized Vulnerability Management vendors for giving very little attention to the topics:
- Asset (host) inventory
- Effective Prioritization of detected Vulnerabilities
- Flexible creation and tracking of Vulnerability Remediation Tasks
- Difficulties with justifying the need for patching
As you can see, I’ve already wrote about some of these topics. And I will write the posts for the rest of them in near future.
Without all this, Vulnerability Management process in the organization will not work, even if you buy the most expensive Vulnerability Management product. In fact, I advocated for the development of custom solutions within the company, the things that I do at work. 🙂
After the main program, I talked with my former colleagues for a long time about the the implementation of VM process from the vendor and from the client side (this visions are very different)!
I really liked the meetup. 🙂 Many thanks to ISACA Moscow and the Moscow Polytechnic University for the organization! And I hope we will meet again next year.

Hi! My name is Alexander and I am a Vulnerability Management specialist. You can read more about me here. Currently, the best way to follow me is my Telegram channel @avleonovcom. I update it more often than this site. If you haven’t used Telegram yet, give it a try. It’s great. You can discuss my posts or ask questions at @avleonovchat.
А всех русскоязычных я приглашаю в ещё один телеграмм канал @avleonovrus, первым делом теперь пишу туда.

Pingback: PRYTEK meetup: Breach and Attack Simulation or Automated Pentest? | Alexander V. Leonov
Pingback: Настоящий Automated Pentest | Александр В. Леонов