The most serious problem of Vulnerability Scanners is that they are too complex and unpredictable. Usually they don’t affect the target hosts, but when they do, welcome to hell! And if you scan huge infrastructure, tens thousands hosts and more, it’s not “if” the scanner will break the server it’s “when” it will do it.
As a responsible person for Vulnerability Management you will be also responsible for all the troubles that VM product can make in the IT infrastructure. And what will you say to the angry mob of your colleagues from IT and Business when they will be quite curious to know why did the service/server go down after the scan? Actually, it’s not much to say.
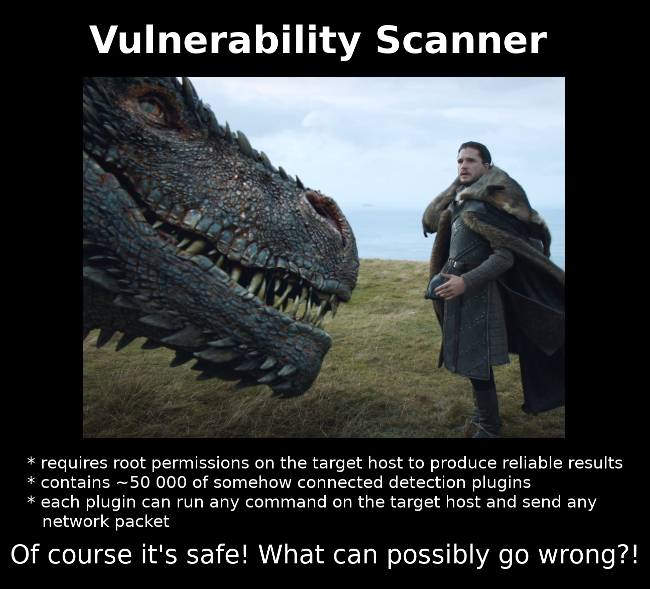
You even won’t be able to say which exactly commands/network packets affected the host, and make the scanner stop doing this. Knowledge base of a modern Vulnerability Scanner contains tens thousands interconnected vulnerability detection plugins that can send any network packets to the host, can run any command in the host OS and require root permissions to produce reliable scan results. Of course, in the case of authenticated scans – the ones that all VM vendors recommend to use, because unauthenticated scans makes a lot of false positives and affects the hosts even more.
So, after you make all the apologies, what can you do to prevent such situation in future?
- If the problem is with the application that was developed by your colleagues, you can, in theory, ask them to rewrite it in a proper way, so the scanner could not affect it. Good luck with this. 😉
- You can contact vendor’s customer support and try to troubleshoot the issue. You will probably need to collect dumps and logs several times, maybe do some debugging with vendor’s support engineers online and after some time (several weeks?) you will get the list of plugins that cause the problem. So, it will be possible to create a custom policy without these plugins.
- And you can just stop using Vulnerability Scanner on these hosts. Simple like this!
And now I am more and more for the third option, because it’s is manageable and it makes the minimal impact on the hosts. Especially when we talk about the operating systems where it’s relatively easy to collect versions of installed packages (god damn It, without active ssh connections!), process these versions and detect vulnerabilities. You can use Vulners Audit for this or make your own detection script. I am going to write a posts on this topic soon.
Once again, Vulnerability Scanners become absolutely monstrous and the idea that you will let them full access to all the systems is completely insane. To build a better Vulnerability Management process in the organization we have to be more flexible. If the systems can only be assessed using vulnerability scanner, ok, let it be it. But if you have any chance to assess the systems without active scanning (at least for the Linux hosts), do it! The idea that we need complex Enterprise level Vulnerability Management solution that will assess every host is not working and can be pretty dangerous. And I am not even talking about the price of such solutions.
upd. Everything can be tuned somehow and the plugin that cause troubles can be excluded from the scan policy, but it requires time, additional efforts and does not guarantee that you won’t face this problems in future. I think if the vendor doesn’t provide a clear view what the scanner does on the target host and the ability to control this behavior, it’s better not to use this scanner for regular automated vulnerability assessment. Of course, if it’s possible.

Hi! My name is Alexander and I am a Vulnerability Management specialist. You can read more about me here. Currently, the best way to follow me is my Telegram channel @avleonovcom. I update it more often than this site. If you haven’t used Telegram yet, give it a try. It’s great. You can discuss my posts or ask questions at @avleonovchat.
А всех русскоязычных я приглашаю в ещё один телеграмм канал @avleonovrus, первым делом теперь пишу туда.

Pingback: Why Asset Management is so important for Vulnerability Management and Infrastructure Security? | Alexander V. Leonov
Pingback: Code IB 2019: Vulnerability Management Masterclass | Alexander V. Leonov