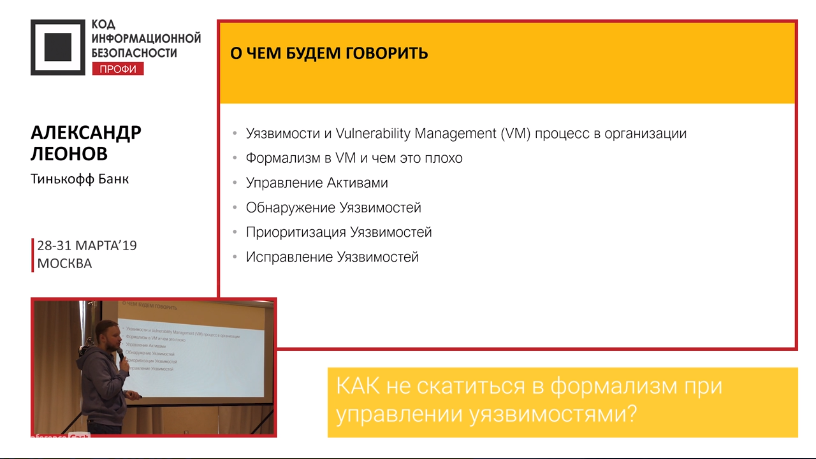
On March 29, I held one hour master class “HOW to avoid excessive formalism in Vulnerability Management process” at Code IB Profi 2019. Everything went quite well and I’ve got 88% positive ratings. Not bad result ^_^.

The main feature of the conference was a very special audience. The only way to visit this event was to buy a real ticket (there were no promotional codes, invites, free tickets from sponsors, etc.). So, the people who came were really interested in the content. Target audience: CISO, their deputies, leading experts from all industries. The whole event was up to 200 people, it lasted for 2 days with 4 threads of masterclasses.
This year organizers decided that titles of all masterclasses should start with “How to” (to keep them practical) and there should be checklists for each masterclass as a handout. I am going to translate my checklist Into English and publish it in this blog soon.
In fact, there were 2 masterclasses on Vulnerability Management at the conference! The second was held by Lev Paley. However, our content did not intersect: I spoke mostly about technical stuff (and I criticized VM vendors as usual), and he spoke mainly about the organizational part and high-level processes.
Vulnerability Management Masterclass
My main message was that Asset Management is the cornerstone for all Infrastructure Security and especially for Vulnerability Management.
- If you know about all the hosts in your infrastructure at any time (at least the hostname, IP address, OS, project, owner, scopes), then you can make further assessment even with some home grown script. And what is the most important, you can measure your progress.
- If you do not have this visibility, then even the most expansive vulnerability scanner won’t help you – there will be blind spots, that attackers can easily use.
By tradition, I criticized Vulnerability Management vendors and their product:
- detection methods (see “No left boundary for Vulnerability Detection“);
- detection plugin structure (see “What’s wrong with patch-based Vulnerability Management checks?“);
- lack of effective differentiation between exploitable and unexploitable vulnerabilities (see “Guinea Pig and Vulnerability Management products“);
- potential danger of active vulnerability scanning (see “Can a Vulnerability Scan break servers and services?“);
- lack of effective vulnerability remediation tools (see “Vulnerability Management vendors and Vulnerability Remediation problems“)
Basically, we have the following sad facts:
- active scanning is dangerous;
- detected vulnerabilities are mostly “theoretically exploitable” ;
- continuous patching requires lots of resources mainly from IT (see “Why *they* don’t patch vulnerabilities“).
This leads to very unpleasant situation when Vulnerability Management becomes a formal procedure, needed only for policy compliance. That’s why the IT teams try to avoid it by all means (especially the final Remediation part). And there are plenty ways how IT can effectively sabotage the VM process. So, do not provoke them!
What can be opposed to this? I don’t have a silver bullet or solution that would be suitable for every organization, but in my opinion current Vulnerability Management solutions are not good enough for big companies with complex infrastructure. Basically, for all organizations, that need a separate Vulnerability Management team. For such organizations it’s much better to make custom and vendor-neutral processes:
- Flexible Asset Management;
- Automation for Vulnerability Scanning (several Vulnerability Assessment products);
- Vulnerability Prioritization;
- Remediation Task Management;
- Vulnerability Management Metrics.
Btw, you can buy video of the masterclass (in Russian and without english subtitles) for $19.33 or all the videos from the conference in a pack for $159.43. I don’t get any money from this, so decide for yourself if it is worth it. It may be better to request a consultation from me directly. 😉
Team work in the Information Security
I also participated as an expert and one of the jury members in a very interesting workshop on “Agile/Scrum/Lean/Six Sigma approaches, etc. for developing software, projects and information security documents” held by Ilya Borisov and Lev Paley.

About 8 teams were working together on specific information security project and presented it the technical side (what solutions to choose, how to use, how much it will cost) and the organizational side. For example, there were projects on import substitution (sadly, but this is a real problem in Russia), cloud infrastructure protection, vulnerability management, etc. It was quite interesting.
In conclusion
I liked the event. The audience was very active and the questions after the masterclass were really good. I’ve learned a lot from the colleagues about Vulnerability Management process in their organizations. It hardly depends on the industry. For example, in industrial production or energy sector, everything is very different than in banks. But some ideas can be reused in our sphere too. 😉
The organization was great. Many thanks for this! Excellent catering, the cakes were especially yummy ^ _ ^. In the souvenirs, I liked the slogan “better late than cryptolocker”. The event was held in Palmira Business Club, it is a good place, the only thing is that the way from it to the nearest subway station is pretty inconvenient.
In the morning I walked a bit on the nearby territory of the former Danilovskaya manufactory. Awesome historic buildings made of red bricks were converted into offices in industrial style, where Rambler&Co, HackerU, Gazeta.Ru and other well-know IT companies are now located. It looks like a quite comfortable location. 🙂

Hi! My name is Alexander and I am a Vulnerability Management specialist. You can read more about me here. Currently, the best way to follow me is my Telegram channel @avleonovcom. I update it more often than this site. If you haven’t used Telegram yet, give it a try. It’s great. You can discuss my posts or ask questions at @avleonovchat.
А всех русскоязычных я приглашаю в ещё один телеграмм канал @avleonovrus, первым делом теперь пишу туда.

Dataset requesting assistance, we explore the most webpages existed to get newest information for our dataset, this will be help our database as a researcher