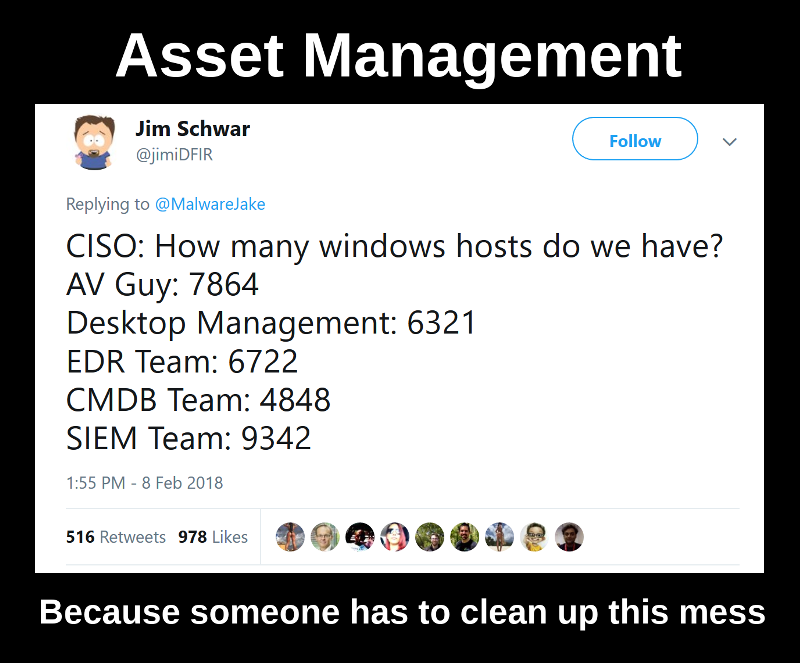
Microsoft Defender for Endpoint: Why You May Need It and How to Export Hosts via API in Python. Hello everyone! In this episode, I want to talk about Microsoft Defender for Endpoint. It’s not a well-known free Defender antivirus built in Windows 10, but an enterprise level solution with the similar name. Yes, the naming is pretty confusing.
I will not repeat Microsoft’s marketing thesis. Just the basic idea. The Windows endpoints on your network have built-in agents that can send some data to the Microsoft cloud. In the cloud, they process this data into security events. Users can see these events in the web interface on the Microsoft website.