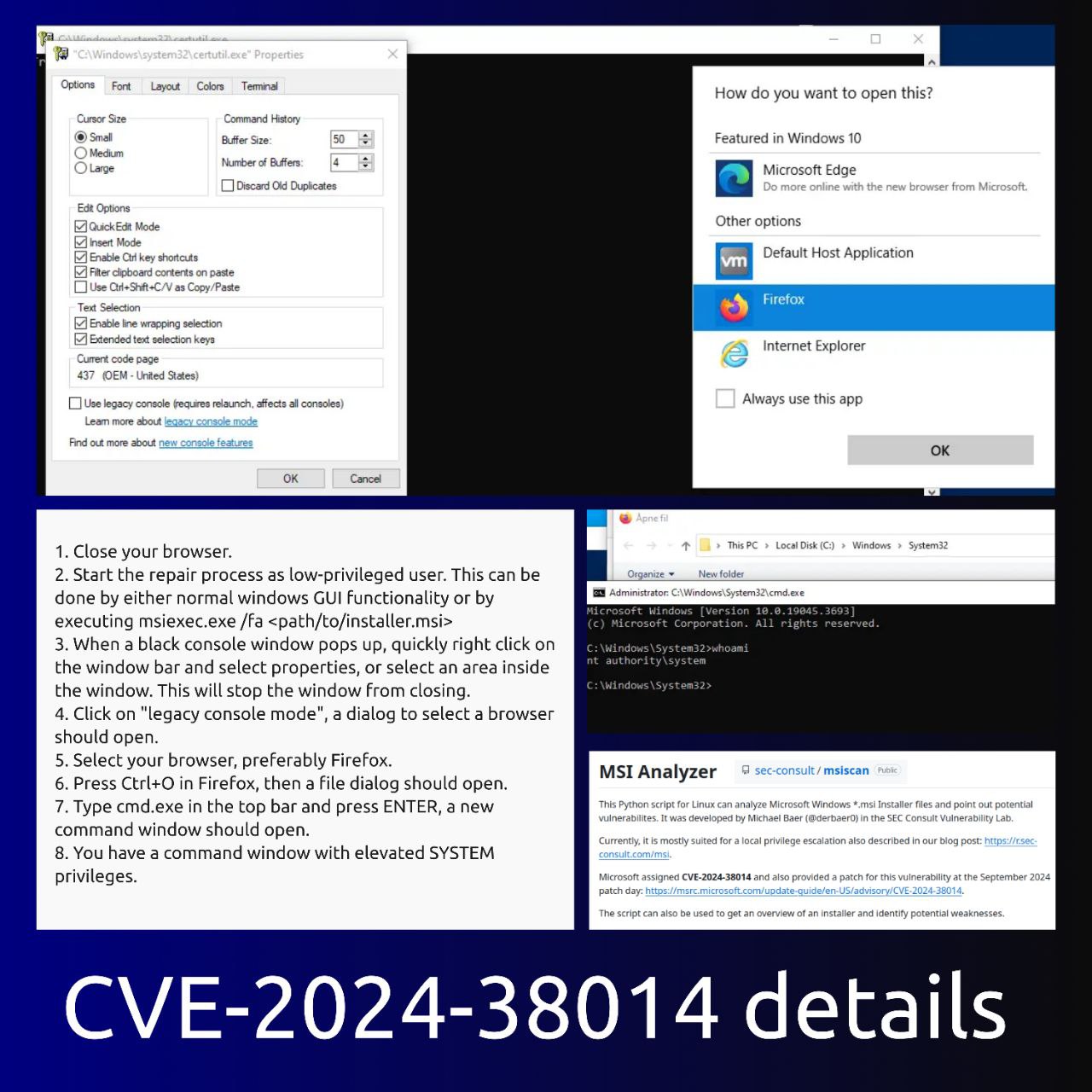
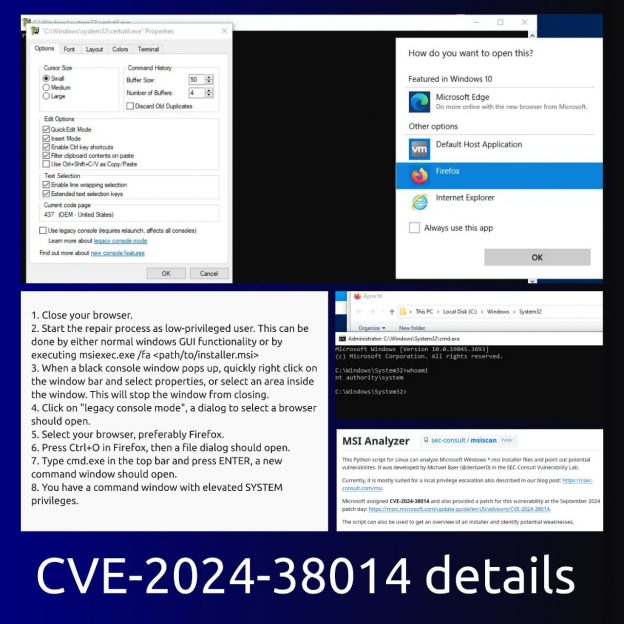
A few details about Elevation of Privilege – Windows Installer (CVE-2024-38014). So that you don’t get the impression that this vulnerability can be exploited absolutely universally.
🔹 The attacker needs access to the Windows GUI. Naturally, the console window needs to be seen and “caught”. Just with the mouse. The task can be simplified by the SetOpLock utility, which does not allow the window to close.
🔹 The attacker needs a web browser installed on the host. Moreover, the current Edge or IE will not work, Firefox or Chrome is needed. And the browser should not be running before the attack. And Edge or IE should not be set as the default browser.
🔹 This will not work for every MSI file. SEC Consult has released a utility called msiscan to detect MSI files that can be used to exploit this and similar vulnerabilities.

Hi! My name is Alexander and I am a Vulnerability Management specialist. You can read more about me here. Currently, the best way to follow me is my Telegram channel @avleonovcom. I update it more often than this site. If you haven’t used Telegram yet, give it a try. It’s great. You can discuss my posts or ask questions at @avleonovchat.
А всех русскоязычных я приглашаю в ещё один телеграмм канал @avleonovrus, первым делом теперь пишу туда.

Pingback: September episode of “In The Trend of VM”: 7 CVEs, fake reCAPTCHA, lebanese pagers, VM and IT annual bonuses | Alexander V. Leonov