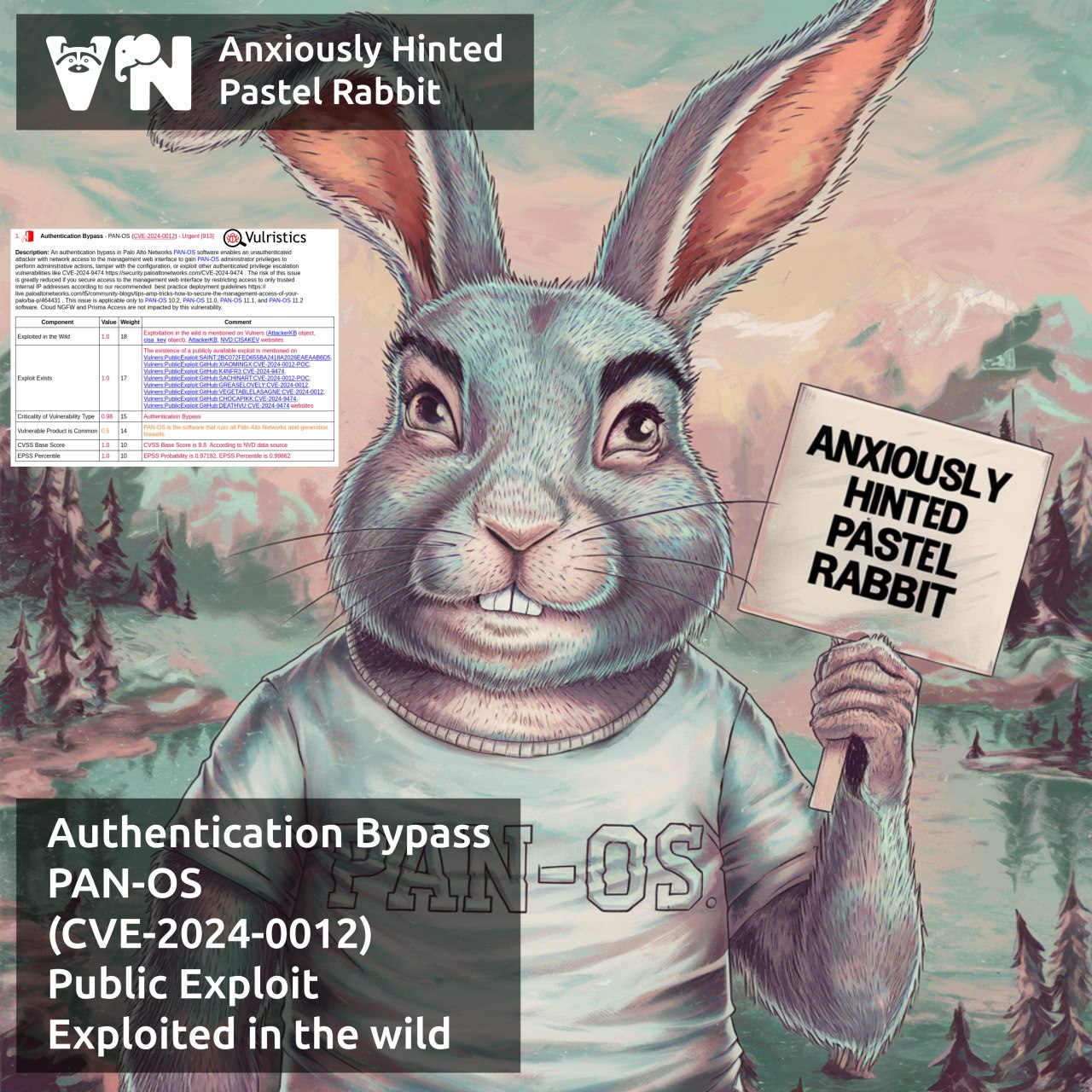
About Authentication Bypass – PAN-OS (CVE-2024-0012) vulnerability. An unauthenticated attacker with network access to the Palo Alto device web management interface could gain PAN-OS administrator privileges to perform administrative actions, tamper with the configuration, or exploit other authenticated vulnerabilities. Firewalls of the PA, VM, CN series and the Panorama management platform are vulnerable. The vendor recommends restricting access to the management web interface to trusted internal IP addresses only.
🔻 On November 8, a Palo Alto bulletin was released
🔻 On November 15, signs of attacks were noticed, labeled as “Operation Lunar Peek”
🔻 On November 18, the vulnerability was added to the CISA KEV
🔻 On November 19, watchTowr Labs released a post with technical details (“supply the off value to the X-PAN-AUTHCHECK HTTP request header, and the server helpfully turns off authentication”) 😏 and exploits soon appeared on GitHub

Hi! My name is Alexander and I am a Vulnerability Management specialist. You can read more about me here. Currently, the best way to follow me is my Telegram channel @avleonovcom. I update it more often than this site. If you haven’t used Telegram yet, give it a try. It’s great. You can discuss my posts or ask questions at @avleonovchat.
А всех русскоязычных я приглашаю в ещё один телеграмм канал @avleonovrus, первым делом теперь пишу туда.

Pingback: About Elevation of Privilege – PAN-OS (CVE-2024-9474) vulnerability | Alexander V. Leonov
Pingback: New episode “In The Trend of VM” (#10): 8 trending vulnerabilities of November, zero budget VM and who should look for patches | Alexander V. Leonov