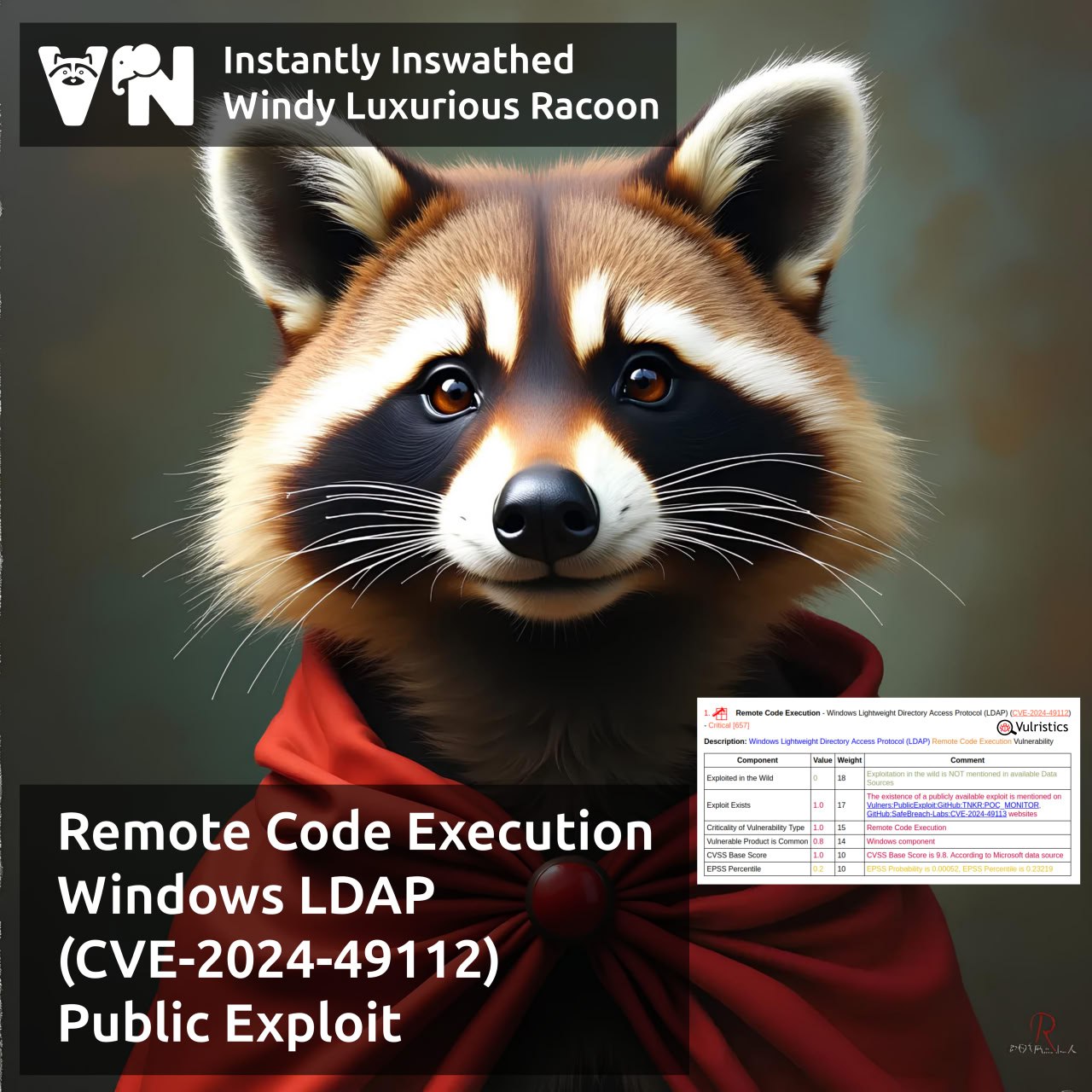
About Remote Code Execution – Windows Lightweight Directory Access Protocol (LDAP) (CVE-2024-49112). The vulnerability is from the December Microsoft Patch Tuesday. Three weeks later, on January 1, researchers from SafeBreach released a write-up on this vulnerability, labeled as LDAPNightmare, and an exploit PoC.
The exploit causes a forced reboot of Windows servers. One prerequisite: the victim domain controller’s DNS server must have Internet connectivity.
The attack flow starts with sending a DCE/RPC request to the victim server, causing the LSASS (Local Security Authority Subsystem Service) to crash and force a reboot when an attacker sends a specially crafted CLDAP (Connectionless Lightweight Directory Access Protocol) referral response packet.
But this is all about DoS, why RCE? 🤔 Researchers note that RCE can be achieved by modifying the CLDAP packet.

Hi! My name is Alexander and I am a Vulnerability Management specialist. You can read more about me here. Currently, the best way to follow me is my Telegram channel @avleonovcom. I update it more often than this site. If you haven’t used Telegram yet, give it a try. It’s great. You can discuss my posts or ask questions at @avleonovchat.
А всех русскоязычных я приглашаю в ещё один телеграмм канал @avleonovrus, первым делом теперь пишу туда.

Pingback: New episode “In the Trend of VM” (#12): 8 February CVEs & Why the Darknet Matters for VM Specialists | Alexander V. Leonov