Qualys Vulnerability Management GUI and API. It has been a long time since I wrote something about Qualys, but today I will write not just about their free product or service, like SSL Labs, but about the main Cloud Platform.
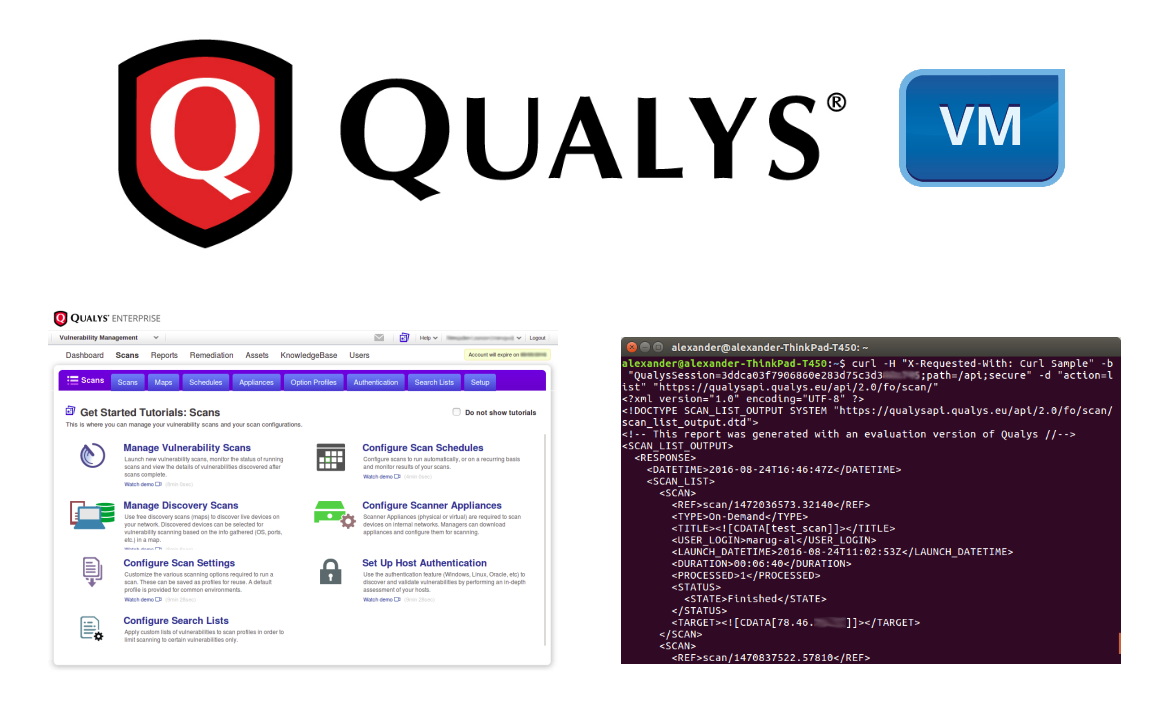
Qualys pioneered cloud Vulnerability Management. How the cloud VM works? In simple terms, there is a web portal https://qualysguard.qualys.com (or .eu for Europe). You can login there, specify a list of IP addresses you want to check and Qualys server(-s) will scan this hosts and show you a vulnerability report.
Ok, it’s clear with perimeter, but what if some hosts are only accessible from your internal network? In this case, you need to purchase Qualys network appliance, which will communicate Qualys server (read more at “Using Qualys Virtual Appliance“). You create a scan task on Qualys web portal to scan hosts in your internal network, Qualys server gives an order to appliance to gather information about these hosts and to send it back to the server for analysis. Most of the security analysis is done “in the cloud” by remote Qualys servers. End-user manage VM service either through Qualys web-portal GUI, or API.