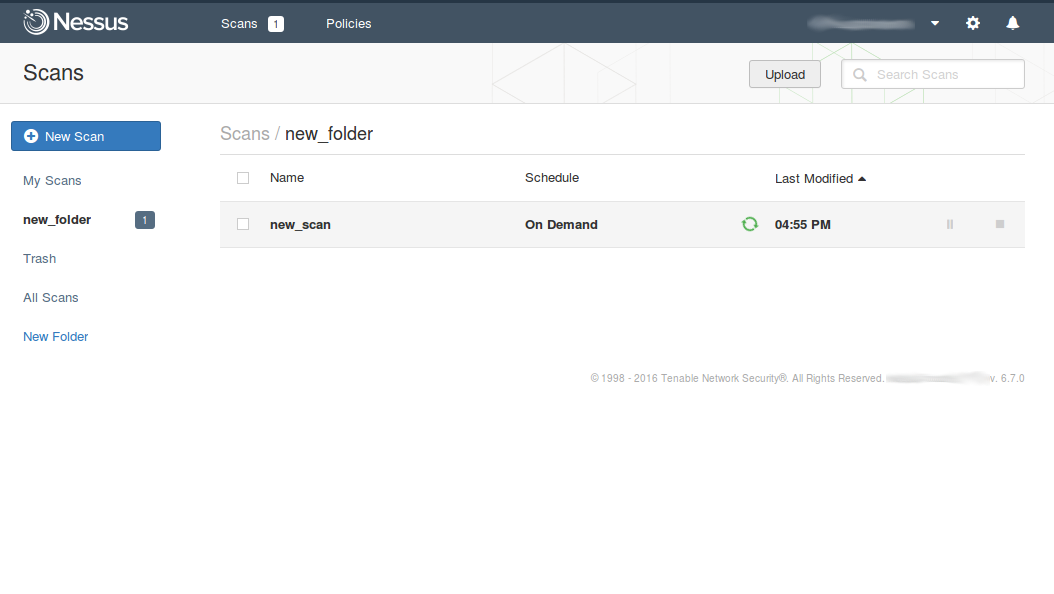
F-Secure API for scanning. This post will be about API of F-Secure Radar. API become a crucial feature when you have to scan a range of thousands hosts and you can’t just add it in one Vulnerability Scanning task. As I mentioned earlier in “F-Secure Radar Vulnerability Management solution” Vulnerability Scanning in Radar is for known active IPs only, for ranges – Discovery Scans. Basically, in F-Secure Radar there is always one vulnerability scan for one host. Unusual concept, but it have some advantages. And it’s quite convenient when you work with Radar via API.
So, my plan for this post is to get active IPs from discovery scan report, create vulnerability scans, run them and get reports. All using API.
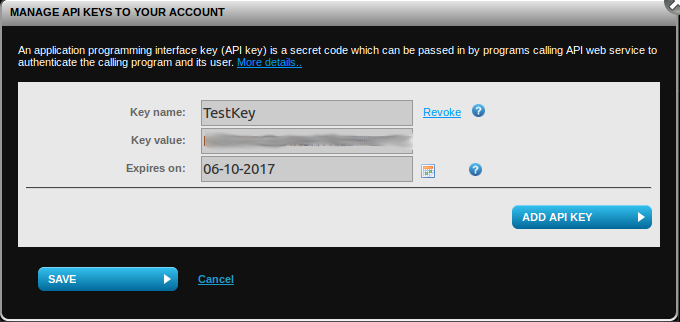
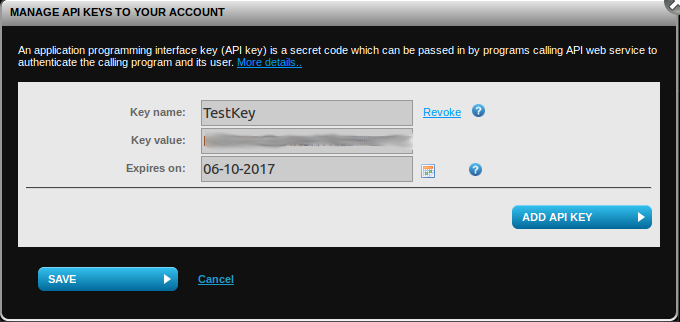
To use API you need to get API key at “F-Secure Radar -> Settings -> My profile”.
To check that API is working we may send a request:
GET /v1/Scans/Types HTTP/1.1
Host: api.radar.f-secure.com
Content-Type: application/json; charset=utf-8
UserName: radar_user@corporation.com
APIKey: JDOBH9MV24ZOENMS94QCO8QP
Continue reading →