Hello everyone! In this episode, I will try to revive Security News with a focus on Vulnerability Management.
On the one hand, creating such reviews requires free time, which could be spent more wisely, for example, on open source projects or original research. On the other hand, there are arguments in favor of news reviews. Keeping track of the news is part of our job as vulnerability and security specialists. And preferably not only headlines.
Alternative video link (for Russia): https://vk.com/video-149273431_456239095
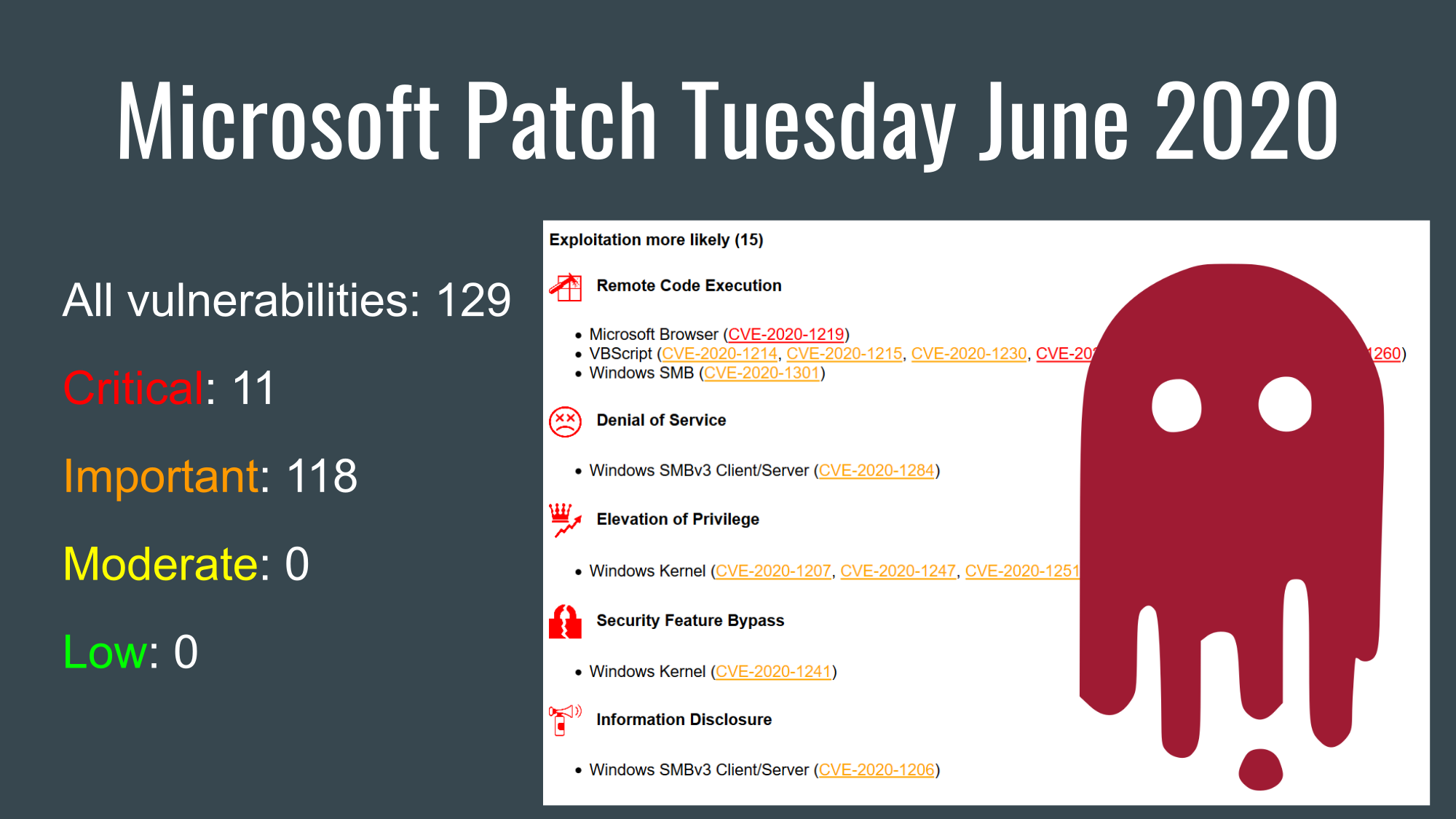
I usually follow the news using my automated telegram channel @avleonovnews. And it looks like this: I see something interesting in the channel, I copy it to Saved Messages so that I can read it later. Do I read it later? Well, usually not. Therefore, the creation of news reviews motivates to read and clear Saved Messages. Just like doing Microsoft Patch Tuesday reviews motivates me to watch what’s going on there. In general, it seems it makes sense to make a new attempt. Share in the comments what you think about it. Well, if you want to participate in the selection of news, I will be glad too.
I took 10 news items from Saved Messages and divided them into 5 categories:
- Active Vulnerabilities
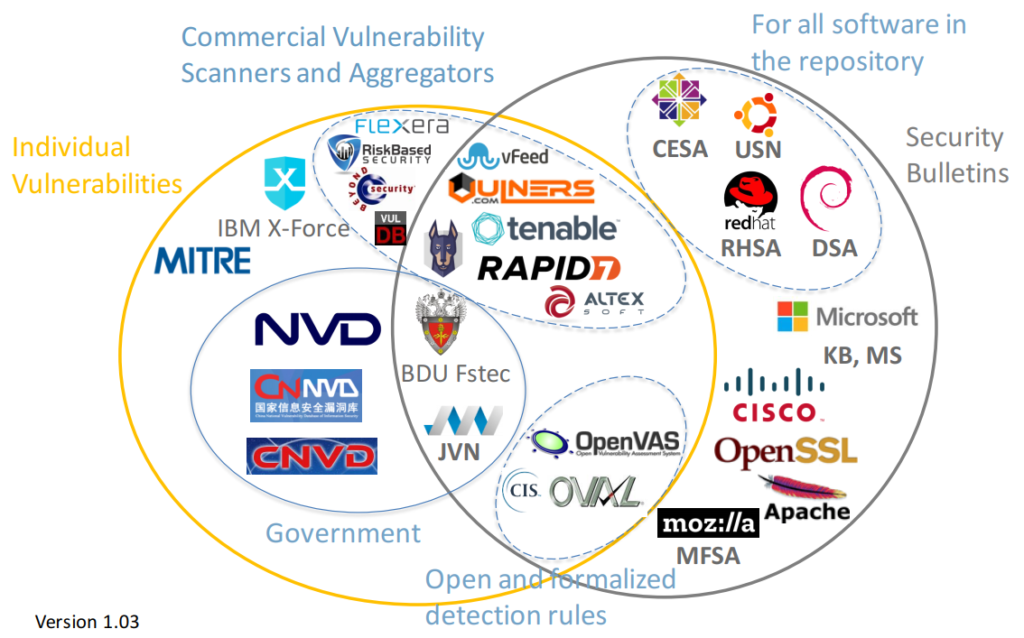
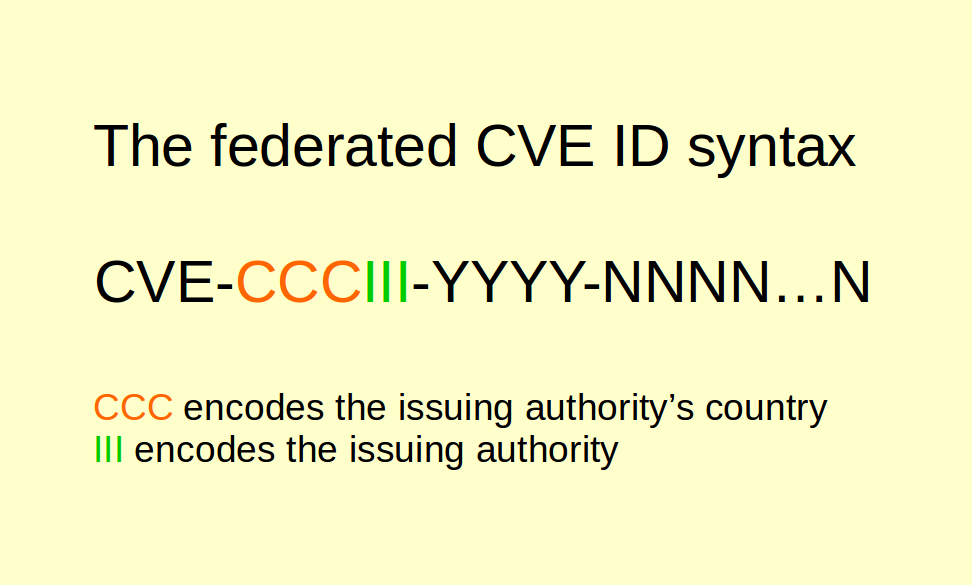
- Data sources
- Analytics
- VM vendors write about Vulnerability Management
- de-Westernization of IT