December Linux Patch Wednesday. In December, Linux vendors began fixing 650 vulnerabilities, roughly the same as in November. Of these, 399 are in the Linux Kernel. No vulnerabilities with signs of in-the-wild exploitation were detected.
For 29 vulnerabilities, public exploits are available or there are indications of their existence. The following can be highlighted:
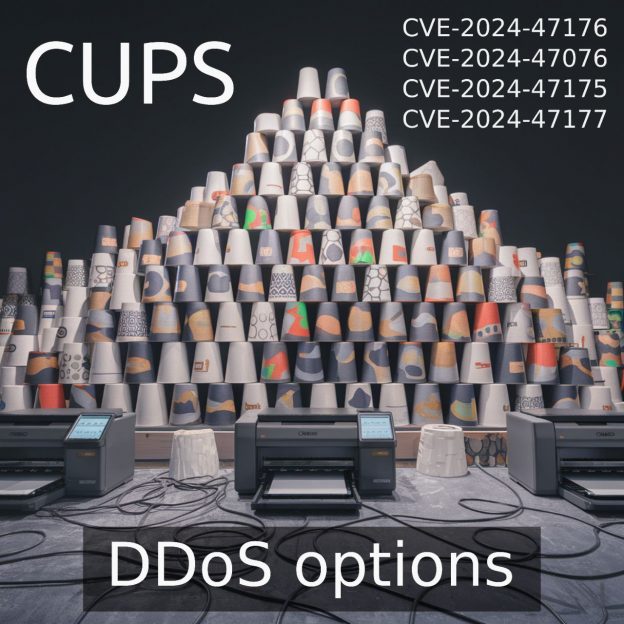
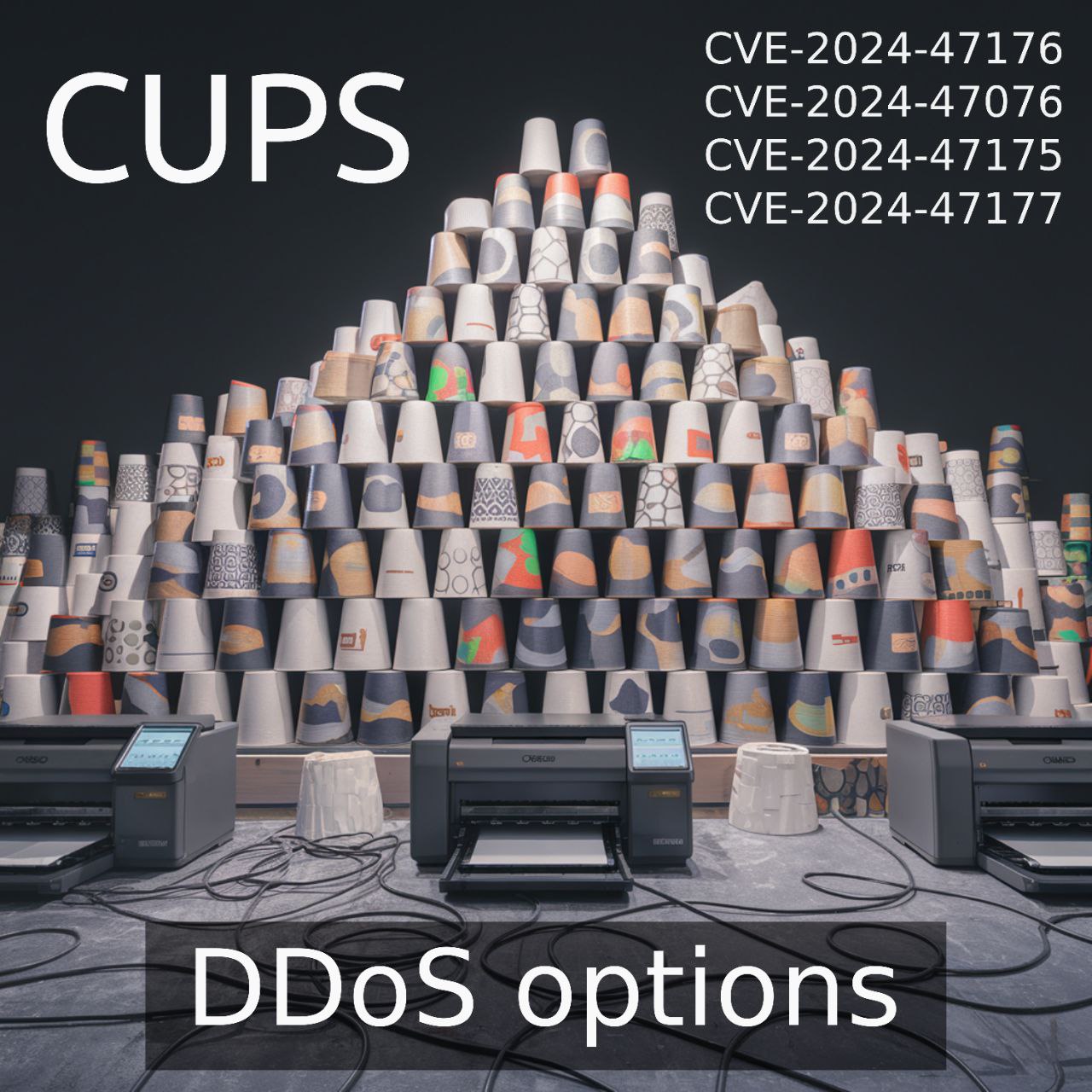
🔸 RCE – JupyterLab Extension Template (CVE-2024-39700), fontTools (CVE-2025-66034), Cacti (CVE-2025-66399), CUPS (CVE-2025-64524)
🔸 XXE – Apache Tika (CVE-2025-66516)
🔸 SQLi – phpPgAdmin (CVE-2025-60797, CVE-2025-60798)
🔸 AuthBypass – cpp-httplib (CVE-2025-66570)
🔸 OpenRedirect – Chromium (CVE-2024-13983)