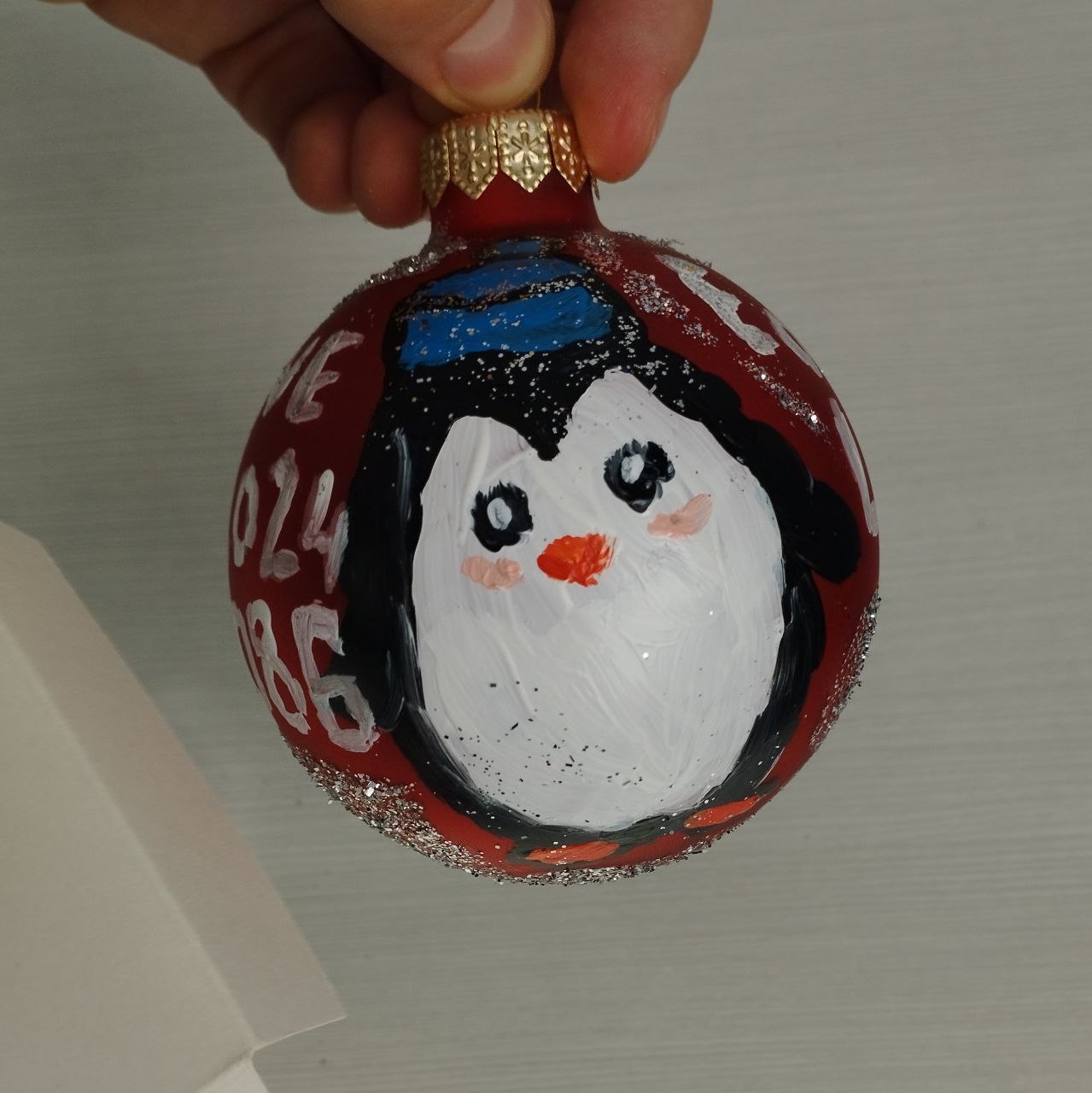
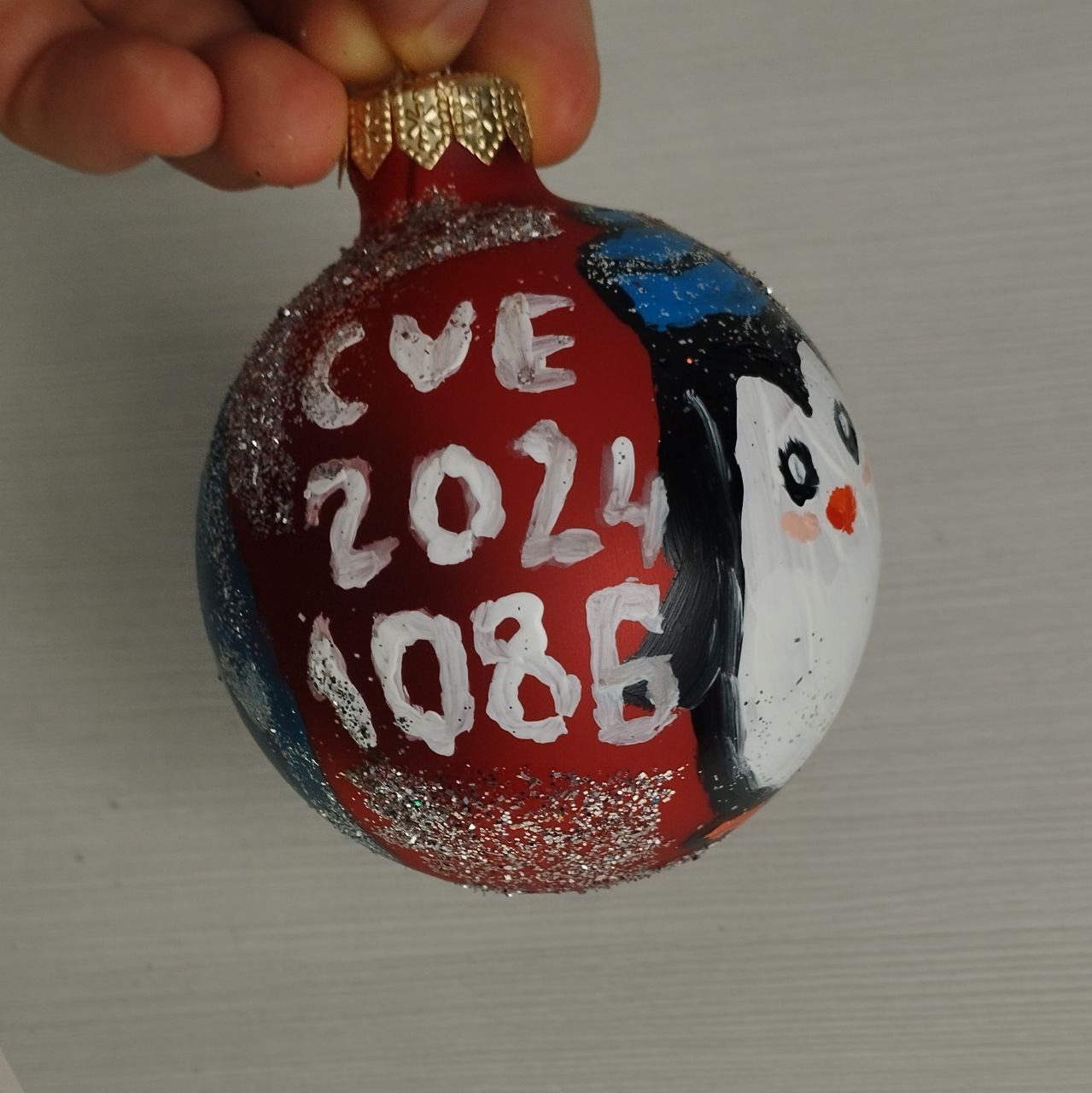
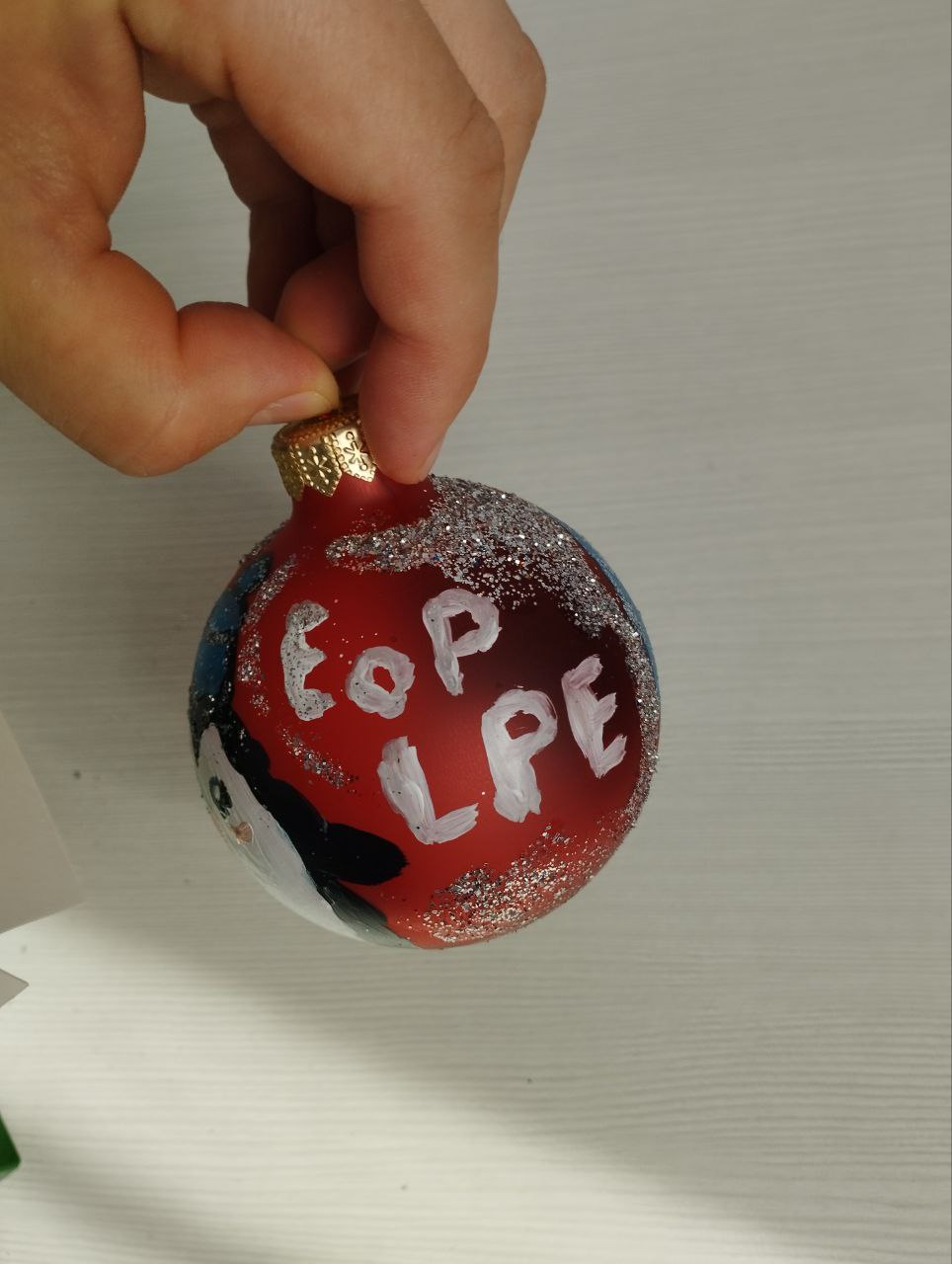
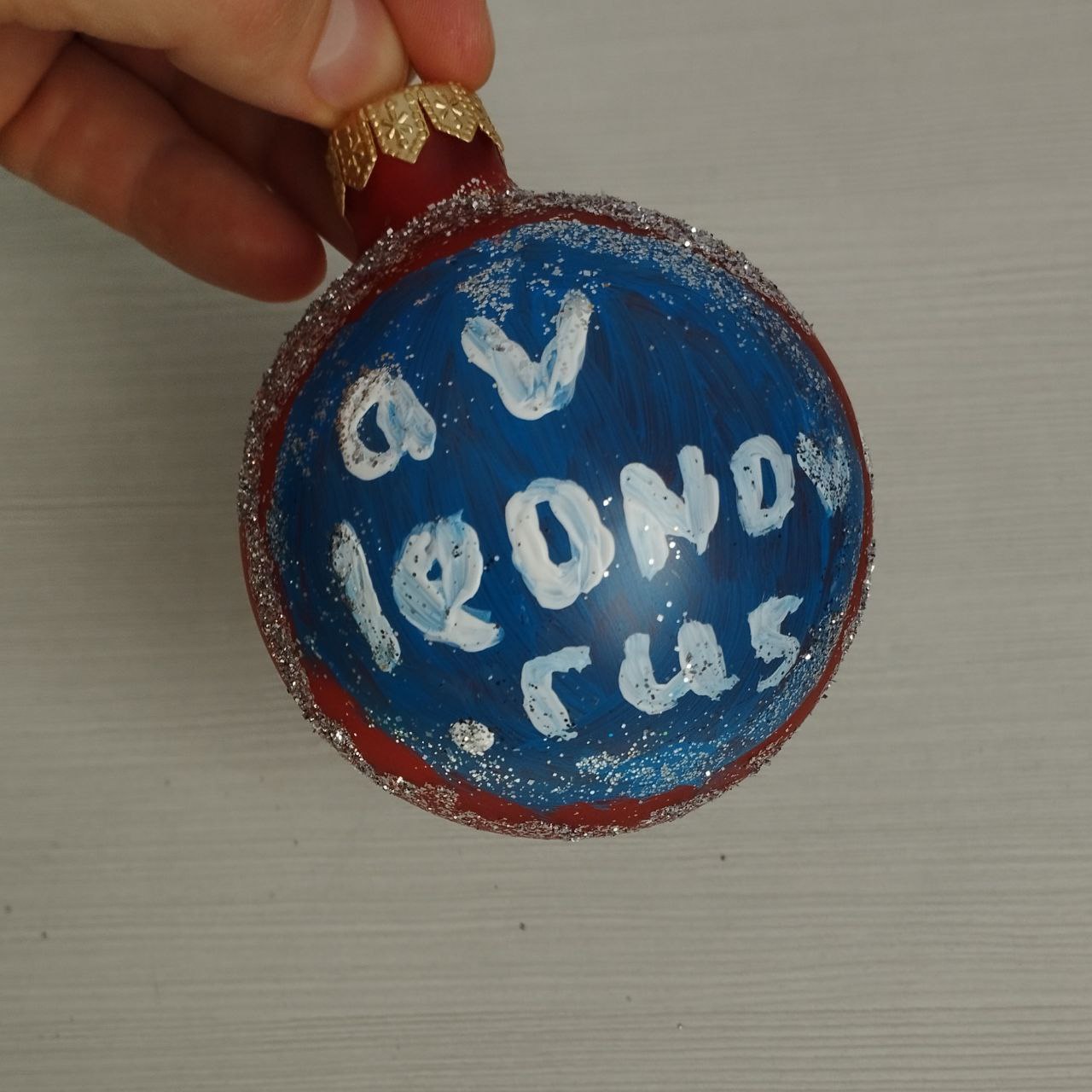
The master class on painting Christmas tree decorations was a success. 👍 They said that you can draw anything. 😏 I drew Elevation of Privilege (Local Privilege Escalation) – Linux Kernel (CVE-2024-1086). 😅

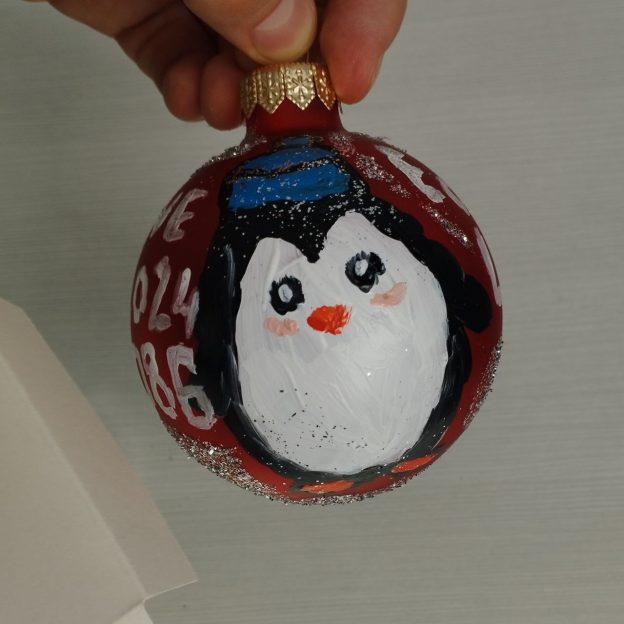
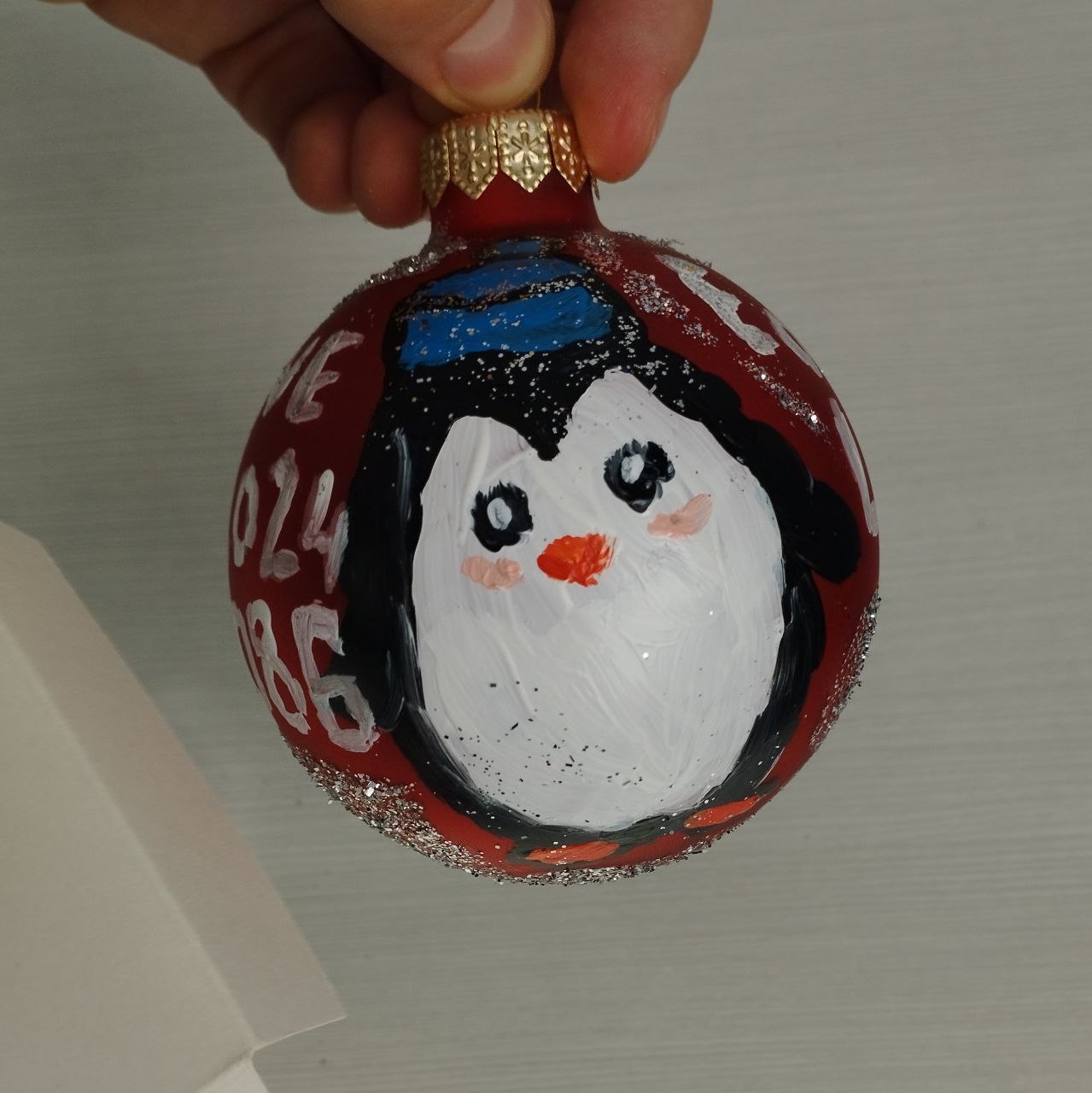
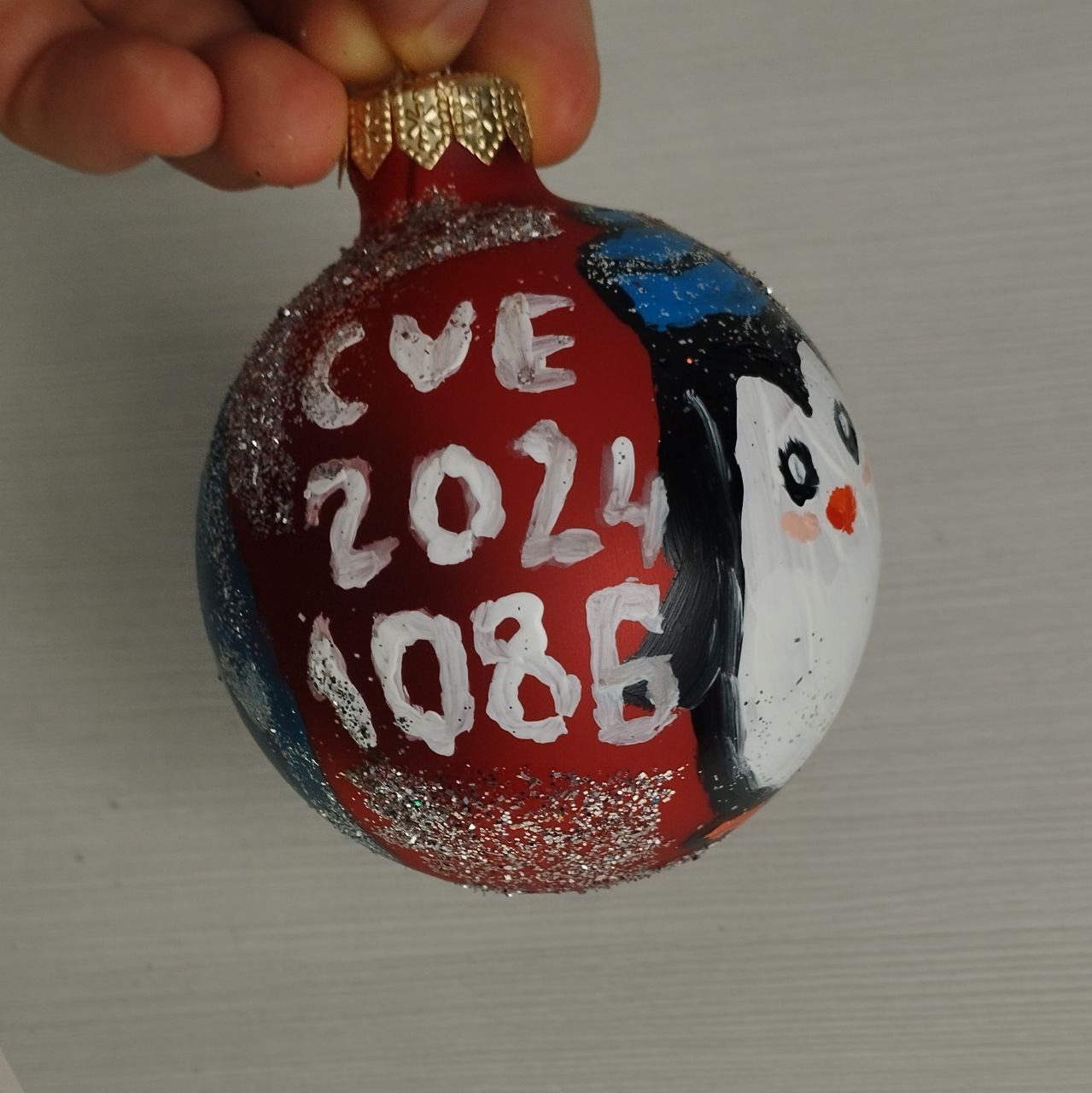
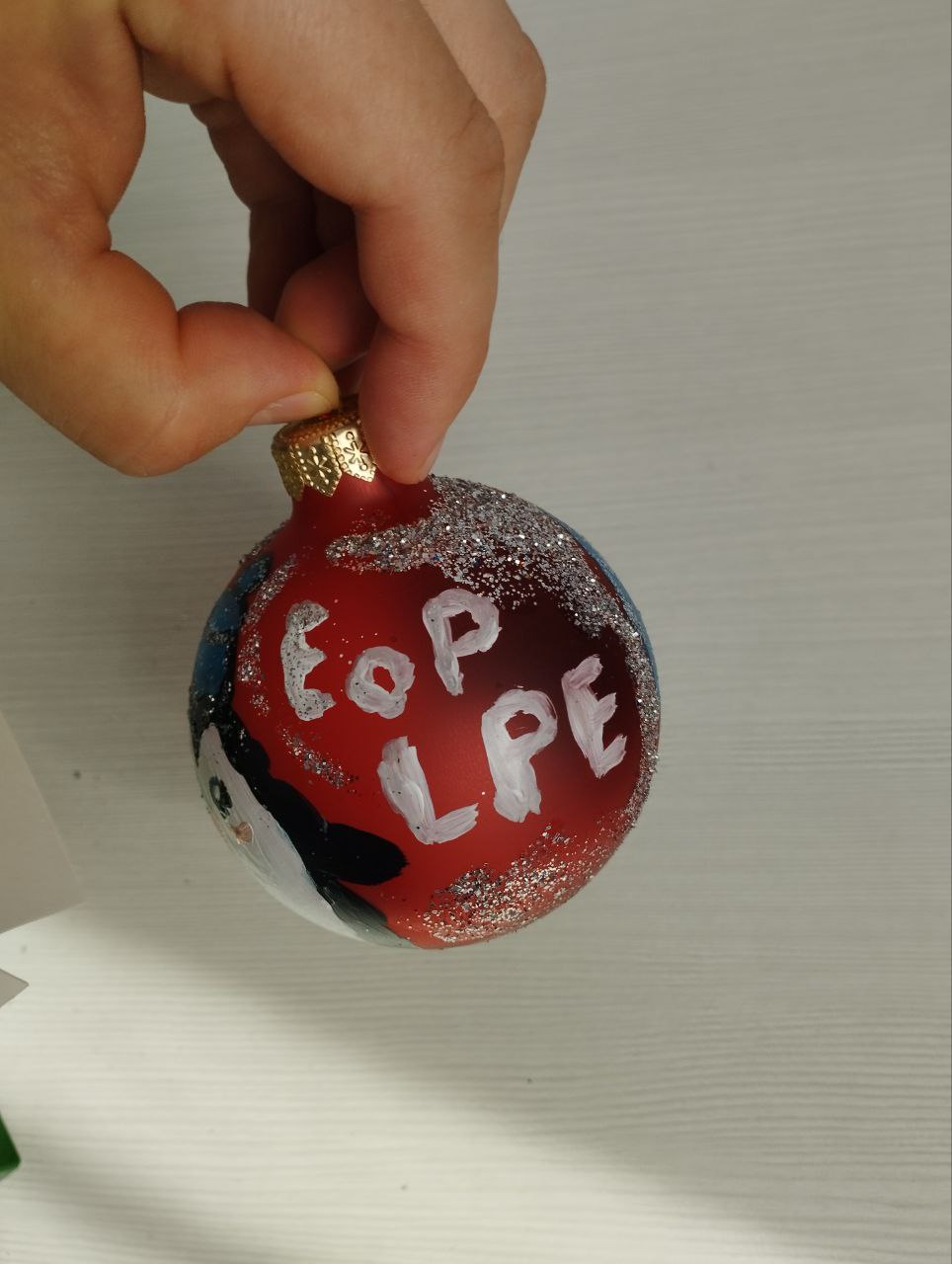
The master class on painting Christmas tree decorations was a success. 👍 They said that you can draw anything. 😏 I drew Elevation of Privilege (Local Privilege Escalation) – Linux Kernel (CVE-2024-1086). 😅
Trending vulnerabilities for June according to Positive Technologies. Traditionally, in 3 formats (in Russian):
📹 The section “Trending VM” in the SecLab news video (starts at 15:03)
🗞 Post on the Habr website, in fact this is a slightly expanded scenario for the “Trending VM” section
🗒 Compact digest with technical details on the official PT website
List of vulnerabilities:
🔻 EoP in Microsoft Windows CSC (CVE-2024-26229)
🔻 EoP in Microsoft Windows Error Reporting (CVE-2024-26169)
🔻 EoP in Microsoft Windows Kernel (CVE-2024-30088)
🔻 RCE in PHP (CVE-2024-4577)
🔻 EoP in Linux Kernel (CVE-2024-1086)
🔻 InfDisclosure in Check Point Security Gateways (CVE-2024-24919)
🔻 RCE in VMware vCenter (CVE-2024-37079, CVE-2024-37080)
🔻 AuthBypass in Veeam Backup & Replication (CVE-2024-29849)
Elevation of Privilege (Local Privilege Escalation) – Linux Kernel (CVE-2024-1086) has been added to CISA KEV. The vulnerability itself is relatively old, from January. I already wrote about it in March, when the write-up and public exploit were released.
Despite the fact that the exploitation of this vulnerability is trivial (the attacker launches a local utility and gains root privileges), until recently there were no signs of exploitation in the wild. This is quite strange: such a useful exploit should immediately be included in the attackers’ toolkit. So either the practical exploitation of this vulnerability is somehow complicated, or the attackers did not leave any traces. 🤔
In any case, on May 30, the vulnerability was added to CISA KEV, and this means the fact of its exploitation in attacks has been proven. But there are no details yet. Please be aware of this vulnerability when upgrading Linux hosts.


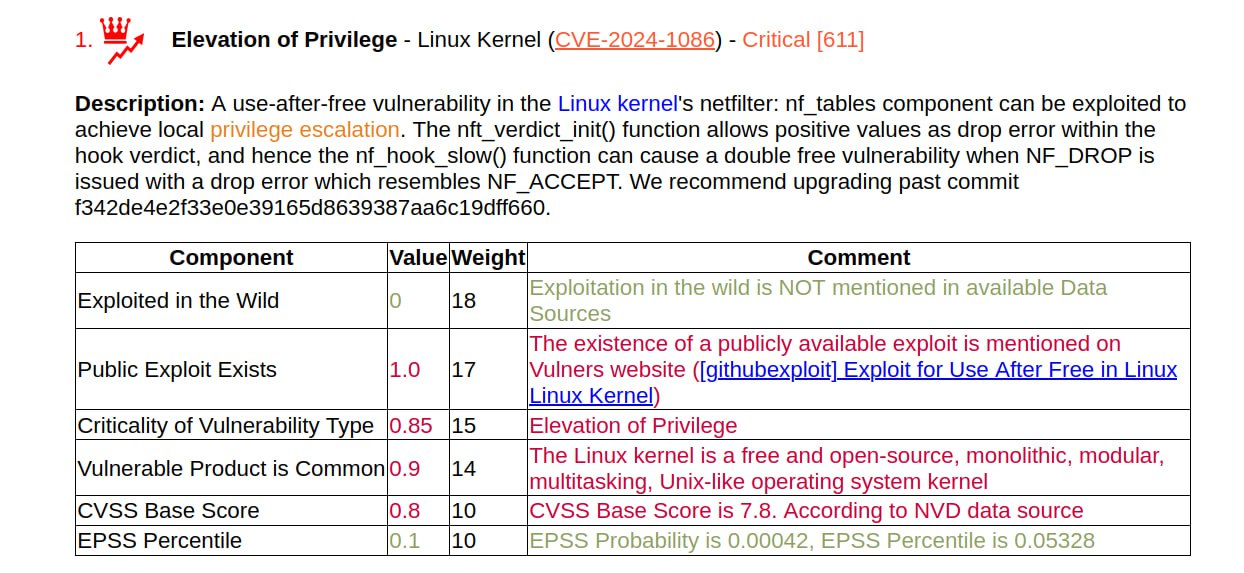
For the January Elevation of Privilege (Local Privilege Escalation) – Linux Kernel (CVE-2024-1086), the write-up and PoC were released on March 26. The video demo for the script looks impressive: they run the script as a regular user and after a couple of seconds they get a root shell. According to the author, the exploit works with most Linux kernels between versions 5.14 and 6.6, including Debian, Ubuntu and KernelCTF.
🔻 The exploit requires kconfig CONFIG_USER_NS=y; sh command sysctl kernel.unprivileged_userns_clone = 1; kconfig CONFIG_NF_TABLES=y. The author writes that this is the default for Debian, Ubuntu, and KernelCTF, and for other distributions it is necessary to test it.
🔹 The exploit does not work with kernels v6.4> with kconfig CONFIG_INIT_ON_ALLOC_DEFAULT_ON=y (including Ubuntu v6.5)
NSFOCUS writes that Redhat is also vulnerable. 🤷♂️
This is my personal blog. The opinions expressed here are my own and not of my employer. All product names, logos, and brands are property of their respective owners. All company, product and service names used here for identification purposes only. Use of these names, logos, and brands does not imply endorsement. You can freely use materials of this site, but it would be nice if you place a link on https://avleonov.com and send message about it at me@avleonov.com or contact me any other way.