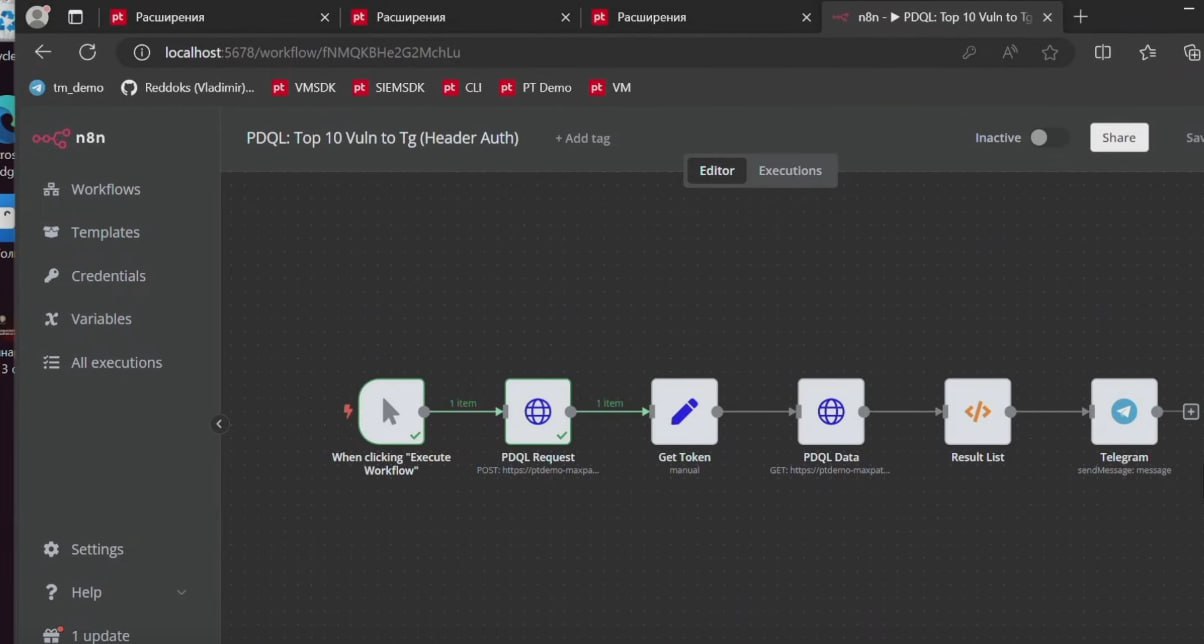
About Remote Code Execution Vulnerability – n8n (CVE-2025-68613). n8n is a workflow automation platform available under a fair-code license. Improper Control of Dynamically-Managed Code Resources (CWE-913) in the n8n workflow expression evaluation system allows a remote authenticated attacker without administrative privileges to execute arbitrary code.
⚙️ The vulnerability was fixed in late December 2025.
⚒️ Exploits on GitHub have been available since December 22, including those for combined exploitation with CVE-2026-21858 (Ni8mare).
👾 On December 26, a detailed write-up by Resecurity was published, reporting signs of exploitation in the wild. On February 27, Akamai reported exploitation of the vulnerability by Zerobot malware. On March 11, the vulnerability was added to the CISA KEV.
🌐 In January, CyberOK SKIPA recorded just under 9,000 active n8n instances in the Runet, ~70% of which were vulnerable.