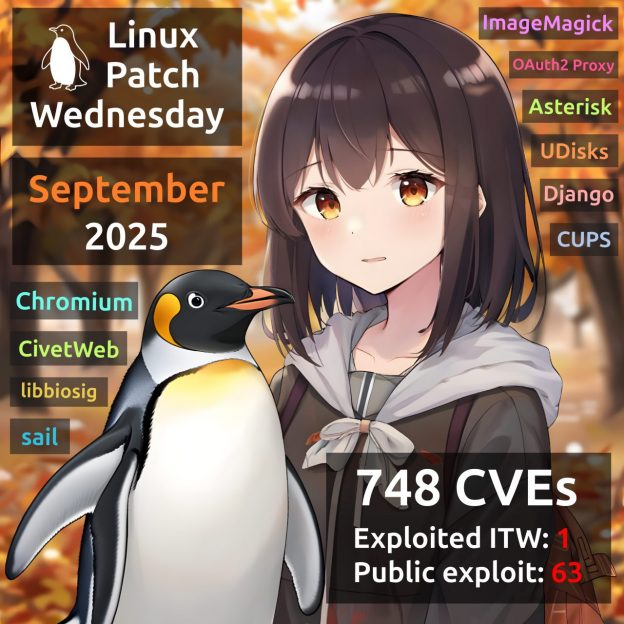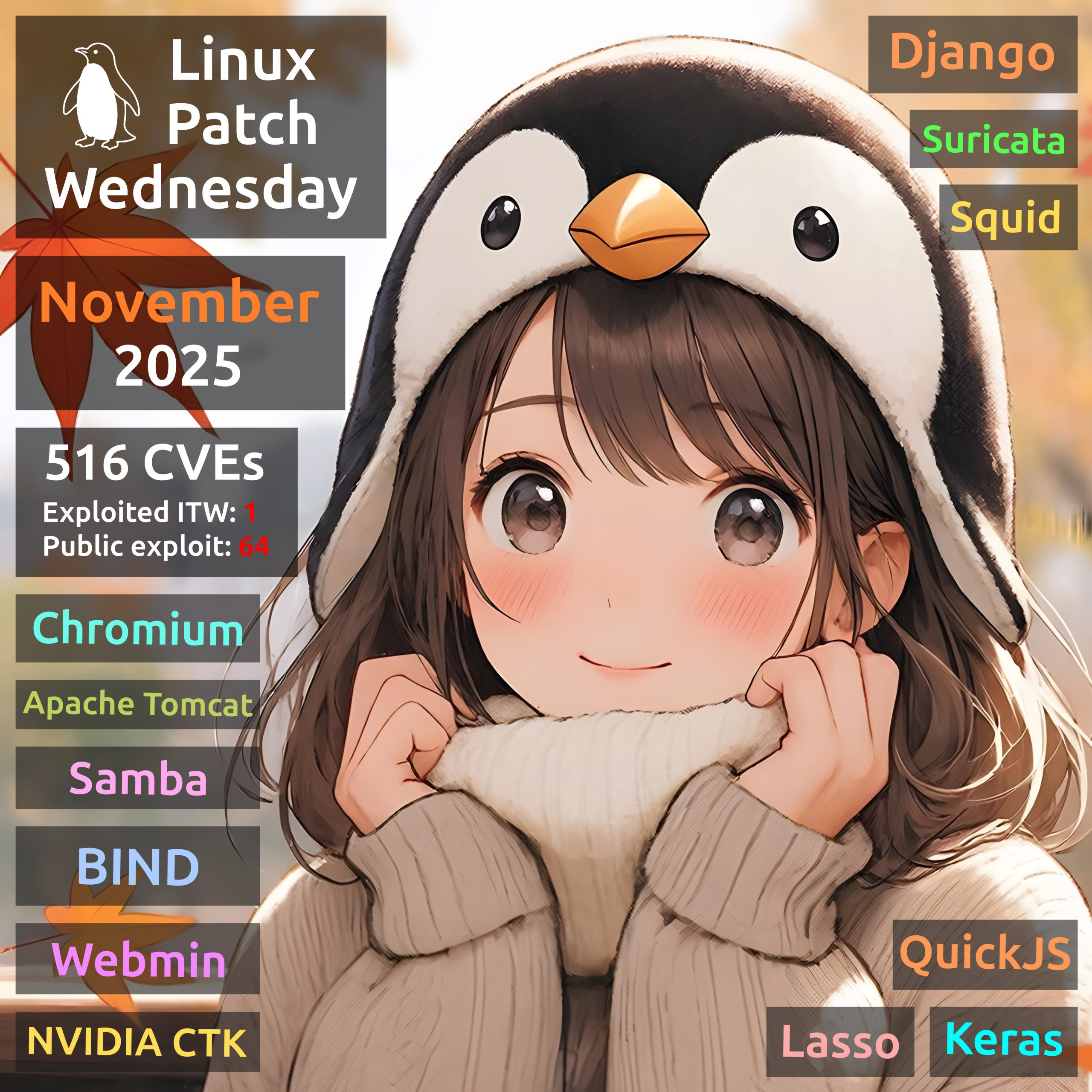
November Linux Patch Wednesday. In November, Linux vendors began fixing 516 vulnerabilities, one and a half times fewer than in October. Of these, 232 are in the Linux Kernel. One vulnerability is exploited in the wild:
🔻 MemCor – Chromium (CVE-2025-13223). Added to CISA KEV on November 19.
For 64 more vulnerabilities, public or suspected exploits exist. Notable ones:
🔸 RCE – Samba (CVE-2025-10230), Apache Tomcat (CVE-2025-55752), NVIDIA Container Toolkit (CVE-2024-0132, CVE-2025-23359), Lasso (CVE-2025-47151), QuickJS (CVE-2025-62494), Keras (CVE-2025-9905)
🔸 SQLi – Django (CVE-2025-64459)
🔸 InfDisc – Webmin (CVE-2024-44762), Squid (CVE-2025-62168), BIND (CVE-2025-31133), QuickJS (CVE-2025-62492, CVE-2025-62493)
🔸 SFB – BIND (CVE-2025-40778)
🔸 AuthBypass – Webmin (CVE-2025-61541)
🔸 MemCor – Suricata (CVE-2025-59150)