As I already wrote in “Installing OpenVAS 9 from the sources“, since May 2017 OpenVAS 9 is available in a form of free virtual appliance. It is called GSM Community Edition (GCE) and is based on Greenbone commercial product GSM ONE.
What’s the difference between GSM ONE and free GCE? GSM Community Edition uses different Community Feed of NASL plugins, it can’t be updated automatically and does not have some management features. The most important, in my opinion, is that it does not support OpenVAS Management Protocol (OMP), API for managing scanners. Only HTTPS for WebGUI and SSH are available.
Talking about different NASL plugin feeds, I need to mention recent message by Jan-Oliver Wagner in Openvas-announce list.
That seems like Greenbone is rather tired of developing OpenVAS by themselves and watching how other companies use theirs engine and feeds, positioning themselves as an “alternative to Greenbone’s product at a better price”. So, they decided:
- “OpenVAS NVT Feed” will be renamed to “Greenbone Community Feed”
- Public access to the “openvas-nvts” SVN repository will be forbidden, but the license of nasl plugins won’t be changed.
- Now Community Feed lags 14 days from commercial feed, but Greenbone would like to make an actual feed, but without some features for enterprise customers.
I really care about Greenbone and they, of course, do as they think is better for the company and OpenVAS community, but at the same time it reminds me situation with Tenable and Nessus. Maybe not so radical. But definitely in the same direction.
Feed delayed for 2 week can’t be used effectively for obvious reasons. If you see exploitation of critical vulnerability like WannaCry in the wild and will need to wait 2 weeks to check your infrastructure, it’s a nonsense! 🙂 That’s mean that you just can’t rely on OpenVAS anymore. And if you use it, you should think about migration on commercial solution, for example on Greenbone’s GSM, or think about getting actual plugin feed somewhere else.
The good thing, it might show customers once again that knowledge base of Vulnerability Management solution is important and stimulate other security content developers to make own nasl scripts and feeds.
But let’s go back to GSM Community Edition. Detailed description of installation process you can find on official site. I will just describe my own experience.
I couldn’t open small OVA to GSM-CE-4.0.5-init.ova
So I created virtual machine manually using recommendations on the official site. I created one NAT network interface with configured port forwarding.
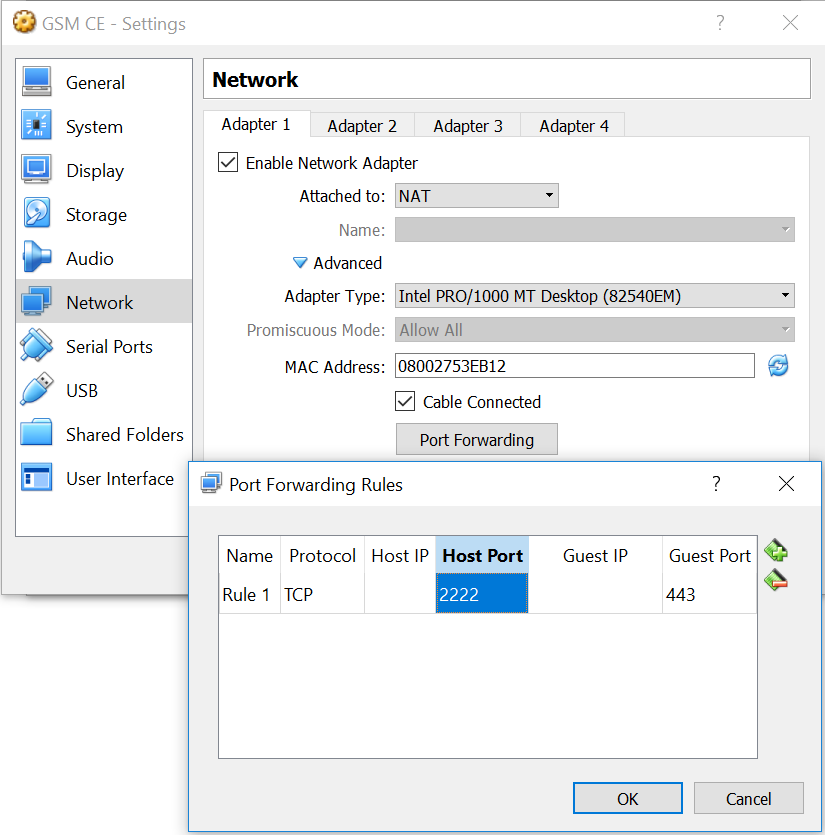
Then I downloaded iso http://dl.greenbone.net/download/VM/gsm_ce_4.0.5.iso attached it to the virtual machine and switched it on.
Installation process is pretty straightforward:
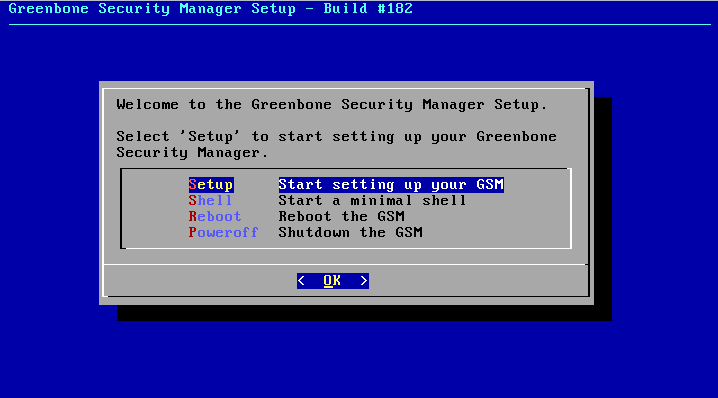
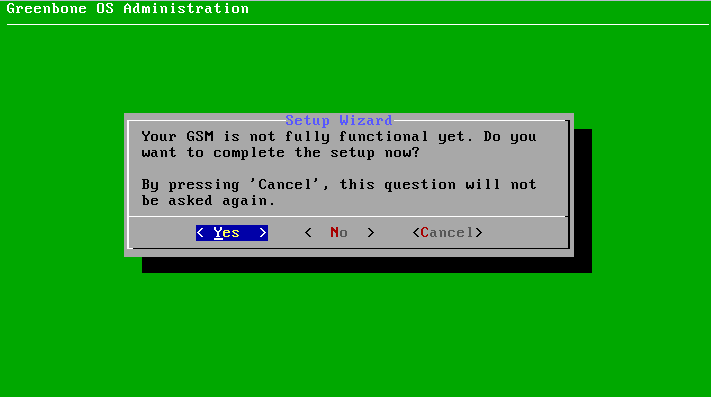
Setup -> Yes (Want to continue)
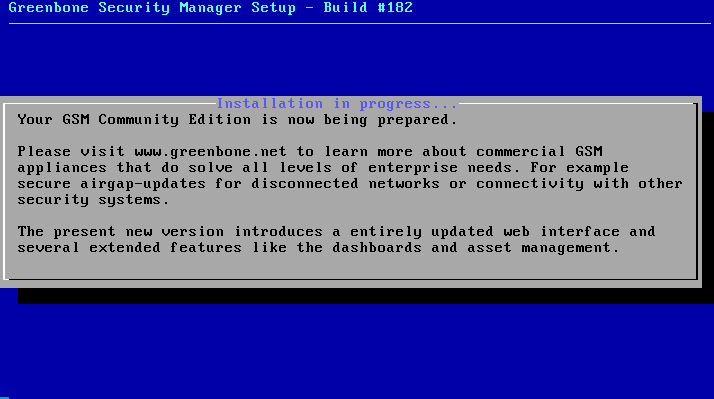
Create admin user (admin/1)
Success!
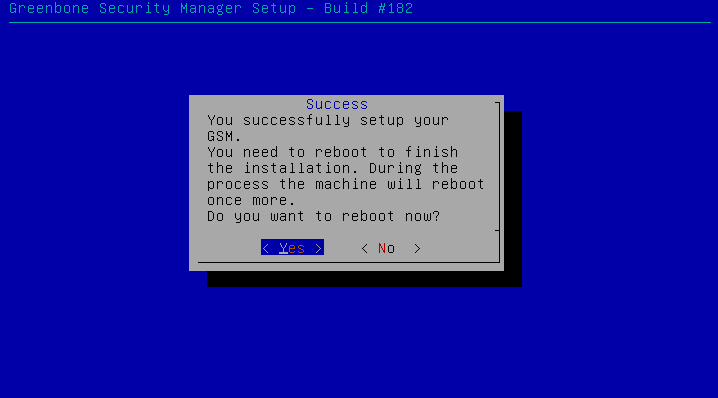
GRUB Screen:
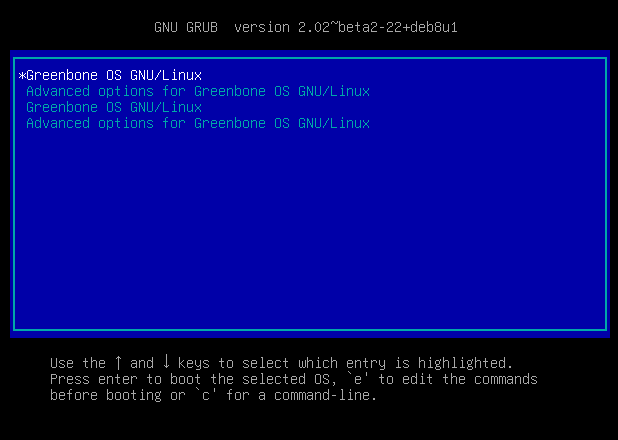
It will boot and then reboot automatically some seconds later. Finally, we can see “Welcome to Greenbone OS 4.0”:
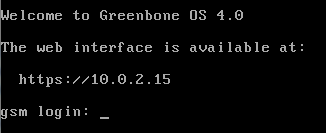
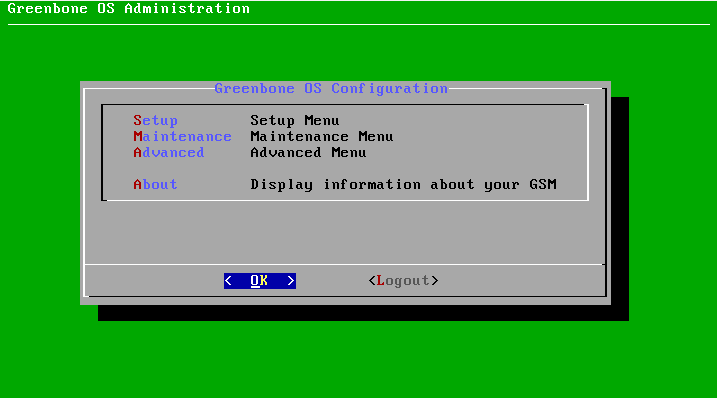
After login you will see the screen to complete setup:
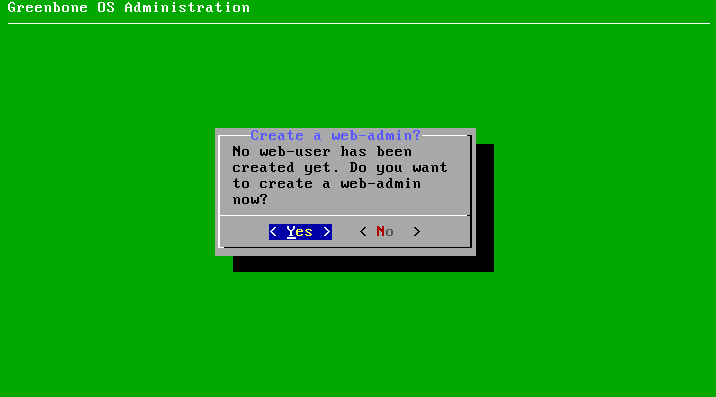
We need to create web-admin user:
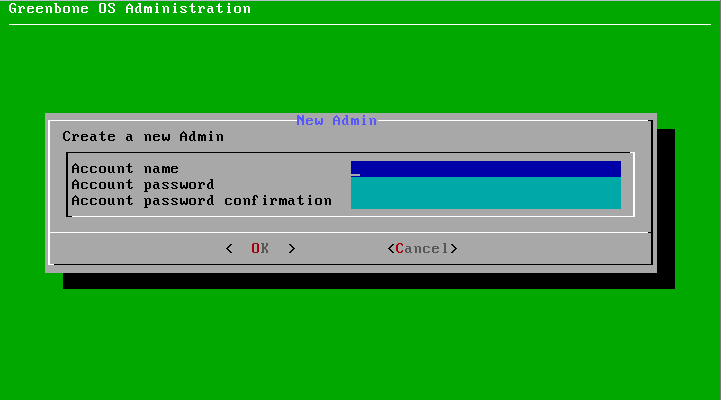
admin/1:
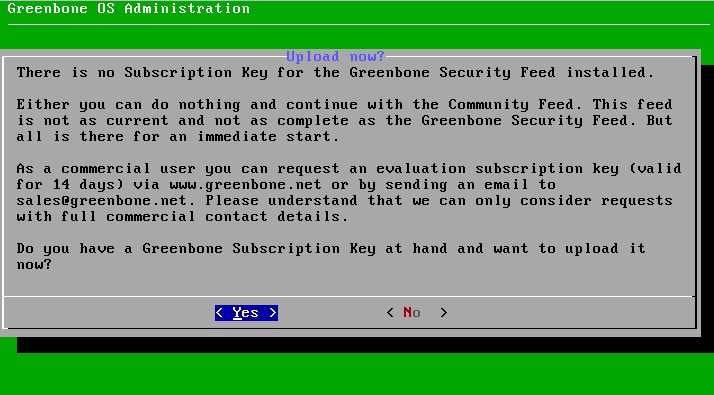
Choose subscription key (if you have one). I will choose “No” and Community Feed.
Than GCE shows recommendation to update feed from the setup menu.
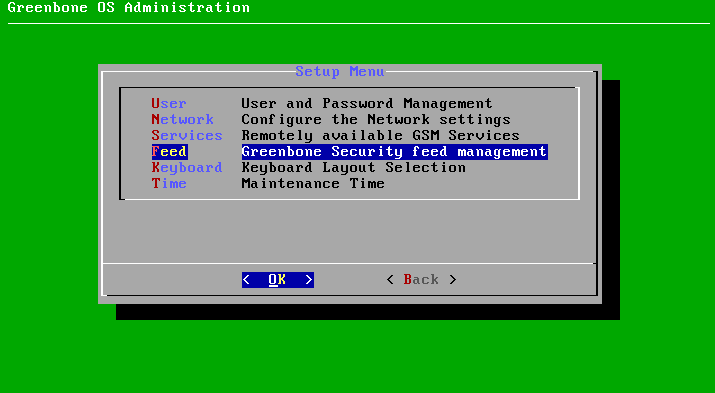
The main setup menu looks like this. To update the vulnerability feed I choose Maintenance:
Then Feed:
And finally press Update:
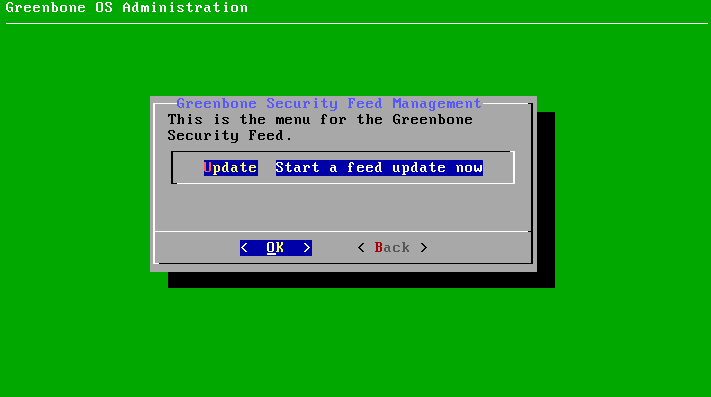
Greenbone Community Edition does some work in background, but whether it has finished updating the Feed or not is not clear.
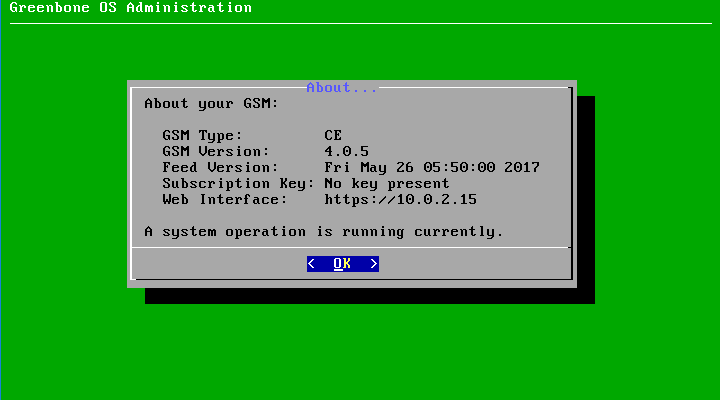
I had a problem here, because GCE did not re-build database automatically. So I did it manually in console.
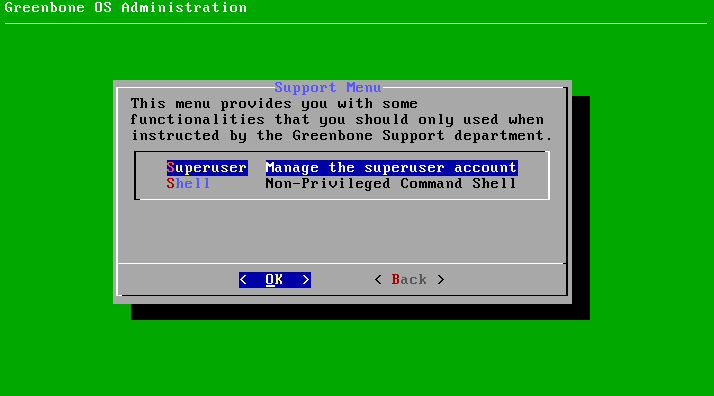
You can get root access to the appliance in Advanced -> Support -> Superuser
And then go to Advanced -> Support -> Shell
And now in shell you can rebuild openvasmd database manually:
![]()
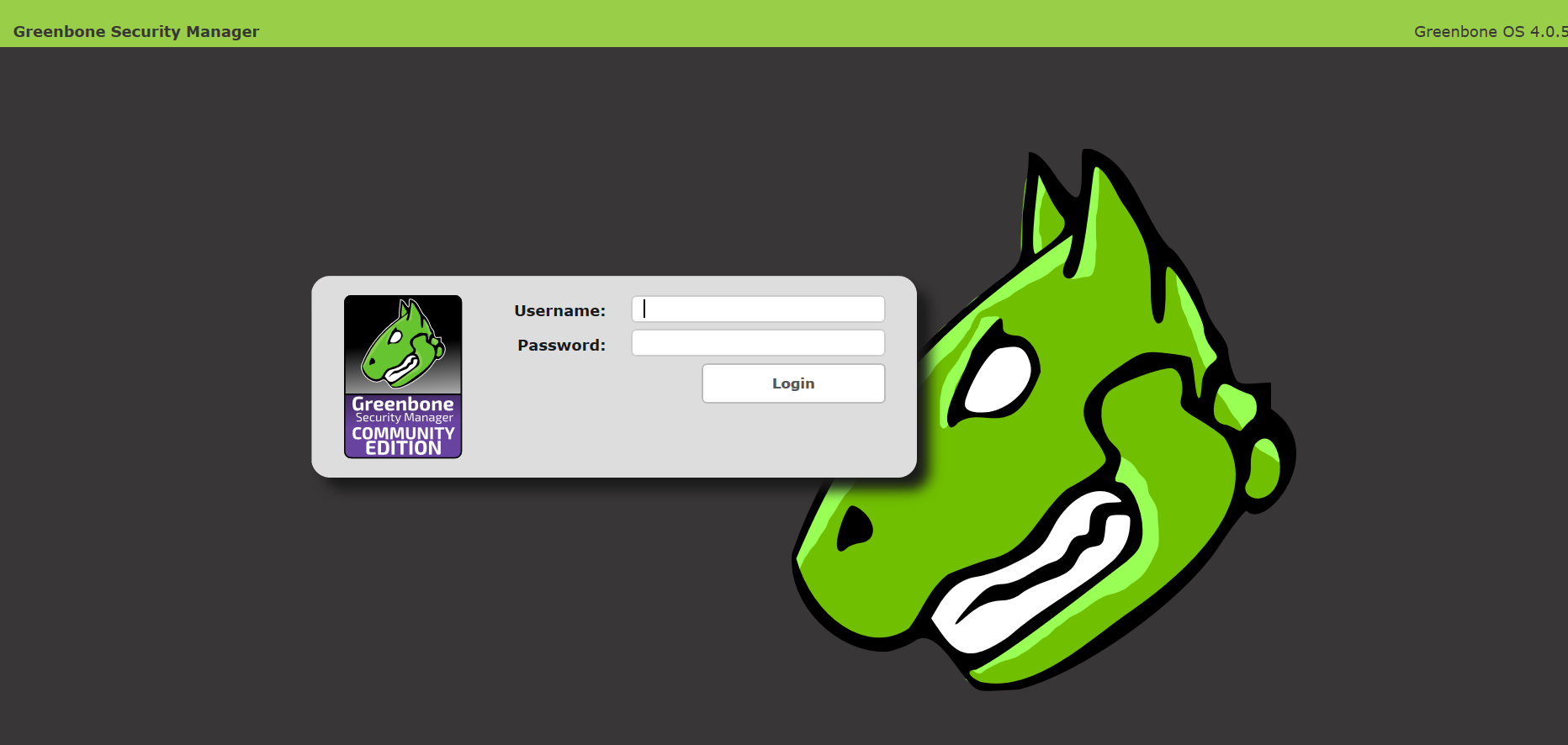
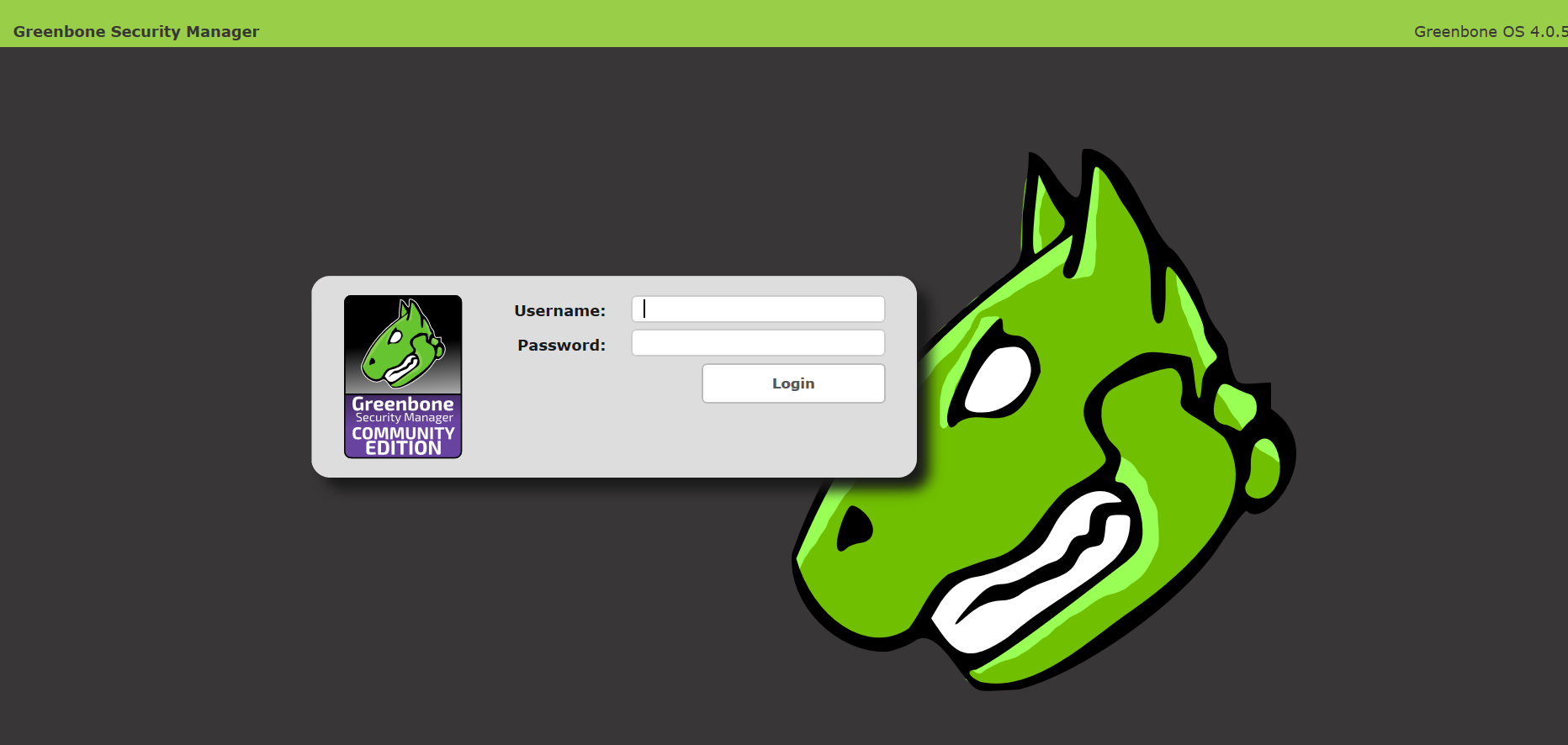
Now we can go to https://localhost:2222, authenticate with web-user password:
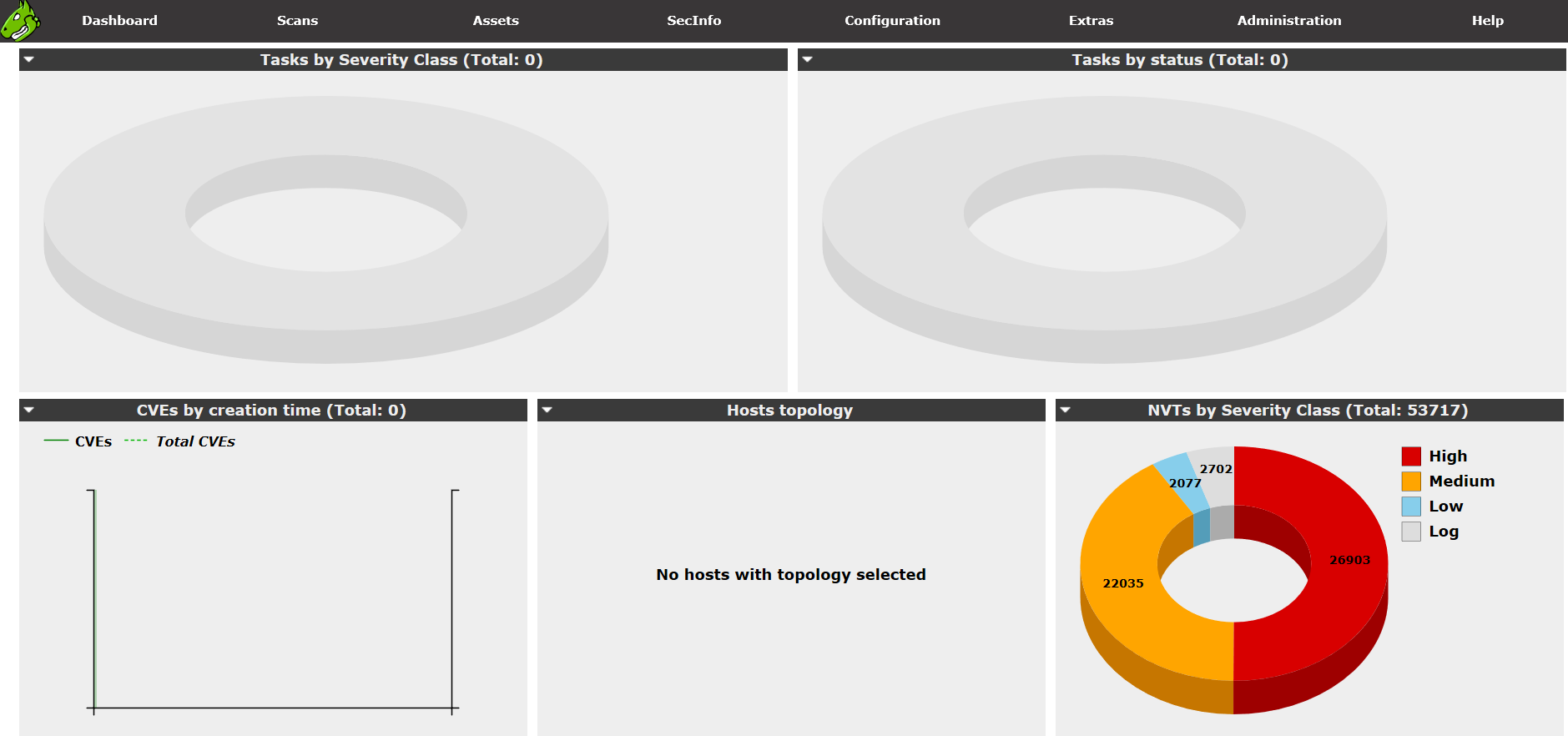
As you can see, detection plugins (NVTs) are in the database, but not SCAP content and CVEs. However, this will be enough for vulnerability scanning.
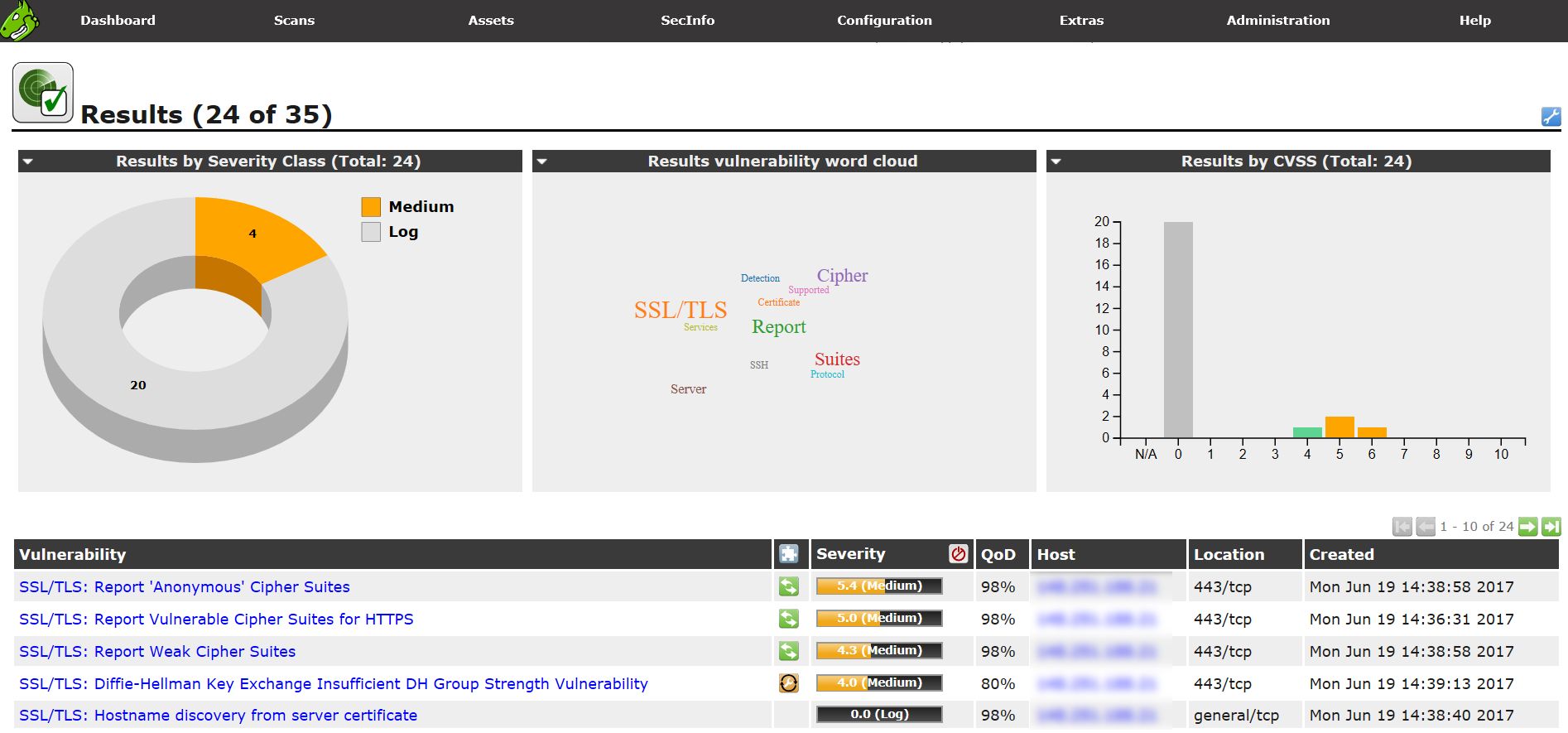
And it scans remote hosts pretty fine:
Conclusions
- You can use GCE for scanning. But I will continue installing OpenVAS from the sources or from Ubuntu packages. First of all, because it’s not possible to use the API with GCE. It certainly can be corrected manually, but it seems not ethical to me.
- Old-school text interface for configuring appliance is cool. Maybe I’ll do something similar for openvas_commander.
- Delayed OpenVAS plugin feed is a very bad news. Maybe we need to develop an alternative feed. If this bothers you too, let me know in the comments below.

Hi! My name is Alexander and I am a Vulnerability Management specialist. You can read more about me here. Currently, the best way to follow me is my Telegram channel @avleonovcom. I update it more often than this site. If you haven’t used Telegram yet, give it a try. It’s great. You can discuss my posts or ask questions at @avleonovchat.
А всех русскоязычных я приглашаю в ещё один телеграмм канал @avleonovrus, первым делом теперь пишу туда.

Pingback: Adding third party nasl plugins to OpenVAS | Alexander V. Leonov
Hello
I have just tripped over the same issue and absolutely sharing your opinion.
I`ve been playing around in the config files of OpenVAS and saw that it would be possible to integrate
other security feeds….but which one ?
Next I thought about on maybe creating a consolidated Sec Feed from multiple sources with maybe
MineMeld from Palo alto Networks.
Source: ( https://www.paloaltonetworks.com/products/secure-the-network/subscriptions/minemeld )
Any thoughts on this, if it`s possible?
Cheers
Christian
Pingback: Great OpenVAS news: delay in plugin feed will be dropped, new GVM-Tools for remote management released | Alexander V. Leonov
Hi, i have a question. when i update the NVT and rebuild the NVT cache, some plugins are do not seem to work properly. I can find the device type by gb_ssh_cisco_ios_get_version before i update. After update, the plugin is still exisit, but the openvas do not seem to use it and i can not find the device type. can you give some advice?
thank you
sincely
hi
I have a problem installing
error is .
your gsm community edition is now being prepared.
please visit http://www.greenbone.net to learn more about commercial GSM appliance that solve all levels of enterprise needs.for example secure airgap-update for disconnect network or connectivity with other security system.
Hey,
Is there a way to update the openvas software (not the feed) in the VM? OR do we have to download the latest version of the VM and reinstall?
Hi Dennis!
“Feed updates happen on a regular basis, but the system itself can not be updated. ”
http://www.openvas.org/vm.html
Hi All,
Is it possible that latest FEED’s can be manually downloaded from any website and manually been updated in GSM, where GSM dont have internet access?
Regards
RaaZeeV