Easiest task ever?
Making the reviews of Microsoft Patch Tuesday vulnerabilities should be an easy task. All vulnerability data is publicly available. Even better, dozens of reviews have already been written. Just read them, combine and post. Right?
Not really. In fact it is quite boring and annoying. It may be fun to write about vulnerabilities that were already used in some real attacks. But this is a very small part of all vulnerabilities. What about more than a hundred others? They are like “some vulnerability in some component may be used in some attack (or may be not)”. If you describe each of them, no one will read or listen this.
You must choose what to highlight. And when I am reading the reports from Tenable, Qualys and ZDI, I see that they choose very different groups of vulnerabilities, pretty much randomly.
My classification script
That’s why I created a script that takes Patch Tuesday CVE data from microsoft.com and visualizes it giving me helicopter view on what can be interesting there. With nice grouping by vulnerability type and product, with custom icons for vulnerability types, coloring based on severity, etc.
Exploited in the wild
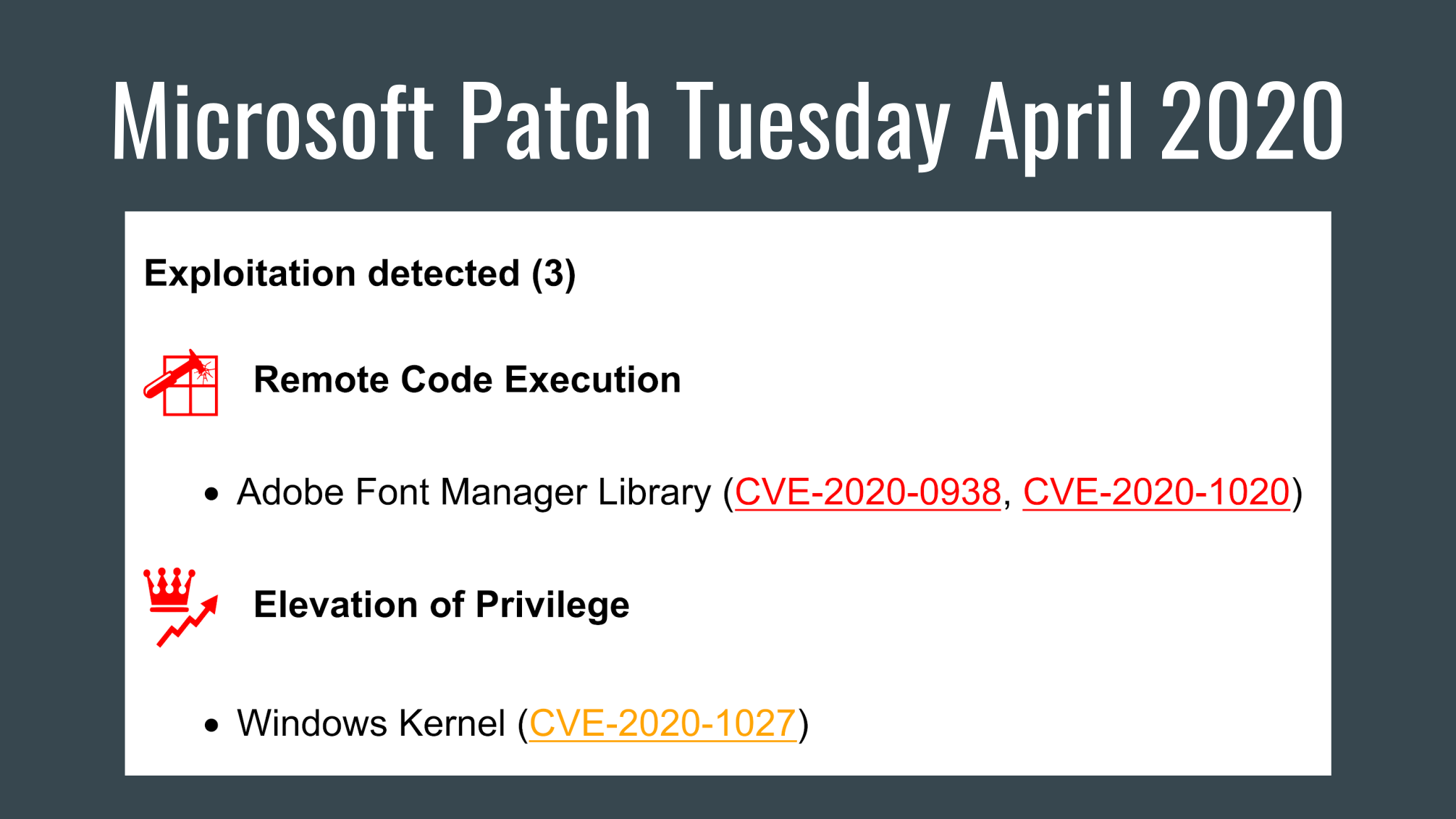
April 2020 Microsoft Patch Tuesday was published on 14.04.2020 and addressed 113 CVEs. 2 CVEs less than in March, but still too many to discuss them separately. 18 CVEs are critical (other reports say 19, but you can count it yourself) and 3 were exploited in the wild. These 3 are the most interesting, I’ve got them by “exploited” parameter in Microsoft CVE data.
Exploitation detected (3)
 Remote Code Execution
Remote Code Execution
- Adobe Font Manager Library (CVE-2020-0938, CVE-2020-1020)
 Elevation of Privilege
Elevation of Privilege
- Windows Kernel (CVE-2020-1027)
Microsoft has finally released a patch for the Adobe Type Manager vulnerability (CVE-2020-1020). The advisory ADV200006 appeared on Microsoft website 23.03.2020, 3 week before this patch. The advisory stated, that this vulnerability was used in targeted attack in the wild. That’s why it was discussed a lot. The idea is simple. If you open a special file or preview it in Explorer, remote code execution will occur. It is noted that previewing it in Microsoft Outlook is safe. This vulnerability is great for phishing attacks, in addition, it is also possible to exploit it through Web Distributed Authoring and Versioning (WebDAV). It is an extension of the HTTP that allows clients to perform remote Web content authoring operations. It is used, for example, in Microsoft SharePoint or ownCloud. And Microsoft claims that exploitation through WebDAV is the most likely attack vector.
I called this vulnerability “confusing” in the title because:
- It has “Adobe” in the name, but is not really related to Adobe. Adobe gave Microsoft the source code of ATM Light for inclusion in Windows 2000/XP. Microsoft maintained this source code after that.
- Microsoft initially stated that RCE exists in 40 version of Windows from Windows 7 to Windows 10 and from Windows Server 2008 to Windows Server 2019. And this is huge. But then they added that exploitation was detected only for Windows 7. And they “do not recommend that IT administrators running Windows 10 implement the workarounds described” in advisory. For Windows Server 2016 and Windows Server 2019 the vulnerability is only “Important”, not “Critical”. And the most vulnerable systems won’t get the updates by default: “to receive the security update for this vulnerability for Windows 7, Windows Server 2008, or Windows Server 2008 R2 you must have an ESU license”. Yet another good reason to upgrade to a newer version.
- The CVE number for this vulnerability was only assigned 3 weeks after it became publicly known. Before that, everyone called it by advisory ID ADV200006. So, CVE is not the ultimate identifier for vulnerabilities. And if you use only CVEs, some vulnerabilities will be out of scope.
Another vulnerability in the Adobe Font Manager Library (CVE-2020-0938) is very similar to previous CVE-2020-1020, although it impacts a different font renderer.
The last exploited vulnerability is the Elevation of Privilege (EoP) in Windows kernel (CVE-2020-1027). To exploit the vulnerability, a locally authenticated attacker should run a specially crafted application. Also all versions of Windows from Windows 7 to Windows 10 and from Windows Server 2008 to Windows Server 2019 are vulnerable.
More likely to be exploited
What else can be interesting? I filtered the CVEs with “Exploitation more likely” flag for current and older versions.
As you can see, the most interesting vulnerability is Scripting Engine Memory Corruption Vulnerability (CVE-2020-0968), which in fact affects Internet Explorer. An attacker can make a specially crafted website that is designed to exploit the vulnerability through Internet Explorer, or use the embedded an ActiveX control in application or Microsoft Office document. As a result, an attacker can execute arbitrary code in the context of the current user.
Exploitation more likely (7)
 Remote Code Execution
Remote Code Execution
- Internet Explorer (CVE-2020-0968)
 Elevation of Privilege
Elevation of Privilege
- DirectX (CVE-2020-0784, CVE-2020-0888)
- Windows Graphics Component (CVE-2020-1004)
- Windows Kernel (CVE-2020-0956, CVE-2020-0957, CVE-2020-0958)
Other more likely to be exploitable vulnerabilities are Elevation of Privilege in DirectX, Windows Graphics Component and Windows Kernel. Not much information is available for them. “An attacker could exploit this vulnerability by running a specially crafted application to take control over the affected system”.
Groups by product
What about other 103 vulnerabilities that are less likely to be exploited according to Microsoft. I made groups for products with more then 5 vulnerabilities.
Other Product based (52)
Jet Database Engine
 Remote Code Execution (CVE-2020-0889, CVE-2020-0953, CVE-2020-0959, CVE-2020-0960, CVE-2020-0988, CVE-2020-0992, CVE-2020-0994, CVE-2020-0995, CVE-2020-0999, CVE-2020-1008)
Remote Code Execution (CVE-2020-0889, CVE-2020-0953, CVE-2020-0959, CVE-2020-0960, CVE-2020-0988, CVE-2020-0992, CVE-2020-0994, CVE-2020-0995, CVE-2020-0999, CVE-2020-1008)
Media Foundation
 Memory Corruption (CVE-2020-0948, CVE-2020-0949, CVE-2020-0950)
Memory Corruption (CVE-2020-0948, CVE-2020-0949, CVE-2020-0950) Information Disclosure (CVE-2020-0937, CVE-2020-0939, CVE-2020-0945, CVE-2020-0946, CVE-2020-0947)
Information Disclosure (CVE-2020-0937, CVE-2020-0939, CVE-2020-0945, CVE-2020-0946, CVE-2020-0947)
Microsoft SharePoint
 Remote Code Execution (CVE-2020-0920, CVE-2020-0971, CVE-2020-0929, CVE-2020-0931, CVE-2020-0932, CVE-2020-0974)
Remote Code Execution (CVE-2020-0920, CVE-2020-0971, CVE-2020-0929, CVE-2020-0931, CVE-2020-0932, CVE-2020-0974) Cross Site Scripting (CVE-2020-0923, CVE-2020-0924, CVE-2020-0925, CVE-2020-0926, CVE-2020-0927, CVE-2020-0930, CVE-2020-0933, CVE-2020-0954, CVE-2020-0973, CVE-2020-0978)
Cross Site Scripting (CVE-2020-0923, CVE-2020-0924, CVE-2020-0925, CVE-2020-0926, CVE-2020-0927, CVE-2020-0930, CVE-2020-0933, CVE-2020-0954, CVE-2020-0973, CVE-2020-0978) Spoofing (CVE-2020-0972, CVE-2020-0975, CVE-2020-0976, CVE-2020-0977)
Spoofing (CVE-2020-0972, CVE-2020-0975, CVE-2020-0976, CVE-2020-0977)
Windows
 Denial of Service (CVE-2020-0794)
Denial of Service (CVE-2020-0794) Elevation of Privilege (CVE-2020-0934, CVE-2020-0983, CVE-2020-1009, CVE-2020-1011, CVE-2020-1015)
Elevation of Privilege (CVE-2020-0934, CVE-2020-0983, CVE-2020-1009, CVE-2020-1011, CVE-2020-1015)
Windows Kernel
 Elevation of Privilege (CVE-2020-0913, CVE-2020-1000, CVE-2020-1003)
Elevation of Privilege (CVE-2020-0913, CVE-2020-1000, CVE-2020-1003) Information Disclosure (CVE-2020-0699, CVE-2020-0821, CVE-2020-0955, CVE-2020-0962, CVE-2020-1007)
Information Disclosure (CVE-2020-0699, CVE-2020-0821, CVE-2020-0955, CVE-2020-0962, CVE-2020-1007)
So, the most interesting groups are Jet Database Engine and Microsoft SharePoint, both have RCEs.
Groups by vulnerability type
All other vulnerabilities in different products I combined by vulnerability type. Interesting EoP in OneDrive for Windows, but “most customers have been protected from this vulnerability because OneDrive has its own updater that periodically checks and updates the OneDrive binary”.
Other Vulnerability Type based (51)
 Remote Code Execution
Remote Code Execution
- Chakra Scripting Engine (CVE-2020-0969, CVE-2020-0970)
- Dynamics Business Central (CVE-2020-1022)
- GDI+ (CVE-2020-0964)
- Microsoft Excel (CVE-2020-0906, CVE-2020-0979)
- Microsoft Graphics (CVE-2020-0687)
- Microsoft Graphics Components (CVE-2020-0907)
- Microsoft Office (CVE-2020-0760, CVE-2020-0991)
- Microsoft Office Access Connectivity Engine (CVE-2020-0961)
- Microsoft Windows Codecs Library (CVE-2020-0965)
- Microsoft Word (CVE-2020-0980)
- VBScript (CVE-2020-0895, CVE-2020-0966, CVE-2020-0967)
- Windows Hyper-V (CVE-2020-0910)
 Authentication Bypass
Authentication Bypass
- Microsoft YourPhone Application for Android (CVE-2020-0943)
 Denial of Service
Denial of Service
- Windows DNS (CVE-2020-0993)
 Elevation of Privilege
Elevation of Privilege
- Connected User Experiences and Telemetry Service (CVE-2020-0942, CVE-2020-0944, CVE-2020-1029)
- Microsoft (MAU) Office (CVE-2020-0984)
- Microsoft Defender (CVE-2020-0835, CVE-2020-1002)
- Microsoft RMS Sharing App for Mac (CVE-2020-1019)
- Microsoft Remote Desktop App for Mac (CVE-2020-0919)
- Microsoft Visual Studio (CVE-2020-0899)
- Microsoft Windows Update Client (CVE-2020-1014)
- OneDrive for Windows (CVE-2020-0935)
- Visual Studio Extension Installer Service (CVE-2020-0900)
- Windows Hyper-V (CVE-2020-0917, CVE-2020-0918)
- Windows Push Notification Service (CVE-2020-0940, CVE-2020-1001, CVE-2020-1006, CVE-2020-1017)
- Windows Scheduled Task (CVE-2020-0936)
- Windows Update Stack (CVE-2020-0985, CVE-2020-0996)
- Windows Work Folder Service (CVE-2020-1094)
 Security Feature Bypass
Security Feature Bypass
- MSR JavaScript Cryptography Library (CVE-2020-1026)
- Windows Token (CVE-2020-0981)
 Information Disclosure
Information Disclosure
- Microsoft Dynamics Business Central/NAV (CVE-2020-1018)
- Microsoft Graphics Component (CVE-2020-0982, CVE-2020-0987, CVE-2020-1005)
- Windows GDI (CVE-2020-0952)
- Windows Push Notification Service (CVE-2020-1016)
 Cross Site Scripting
Cross Site Scripting
- Microsoft Dynamics 365 (On-Premise) (CVE-2020-1049, CVE-2020-1050)
Zero Day Initiative recommends to note Denial-of-Service in the Windows DNS service (CVE-2020-0993). “Considering the damage that could be done by an unauthenticated attacker”. At the same time Microsoft website says: “To exploit the vulnerability, an authenticated attacker could send malicious DNS queries to a target, resulting in a denial of service”. It seems like a mistake on ZDI or MS, but worth mentioning.
Updates for older vulners
So, that’s it for April Patch Tuesday. What about the interesting vulnerabilities from February and March?
- CVE-2020-0796 – Windows SMBv3 Client/Server Remote Code Execution Vulnerability. New exploit now available for this vulnerability, it’s even in Metasplot. But it’s not the one you have probably waited for. It does not attack remote hosts, it’s a local exploit for “(hopefully privileged) payload execution”.
upd. While I was working on this post I missed the news about CVE-2020-0796 RCE POC by Ricerca Security. The code is not available, here is technical description and video. - CVE-2020-0688 – Microsoft Exchange server “single e-mail” seizure. Exploit exists. Rapid7 made a nice report “What we found was that at least 357,629 (82.5%) of the 433,464 Exchange servers we observed were known to be vulnerable.”
- CVE-2020-0684 – .LNK files processing. Nothing new.
- CVE-2020-0662 – Mysterious Windows RCE. Nothing new.

Hi! My name is Alexander and I am a Vulnerability Management specialist. You can read more about me here. Currently, the best way to follow me is my Telegram channel @avleonovcom. I update it more often than this site. If you haven’t used Telegram yet, give it a try. It’s great. You can discuss my posts or ask questions at @avleonovchat.
А всех русскоязычных я приглашаю в ещё один телеграмм канал @avleonovrus, первым делом теперь пишу туда.

Pingback: Microsoft Patch Tuesday May 2020 | Alexander V. Leonov