Getting Hosts from Microsoft Intune MDM using Python. Today I want to talk about Microsoft Intune. It is a Mobile Device Management platform.
Well, I think that the importance of MDM systems has become much higher than it was before the days of covid-19. Simply because a lot more people now work remotely using corporate laptops. And if these people don’t connect to the corporate network using a VPN, you most likely won’t see any activity from their devices in Active Directory. This means that you will not understand whether the device is active or not. And it will be impossible to get the correct security metrics for these devices.
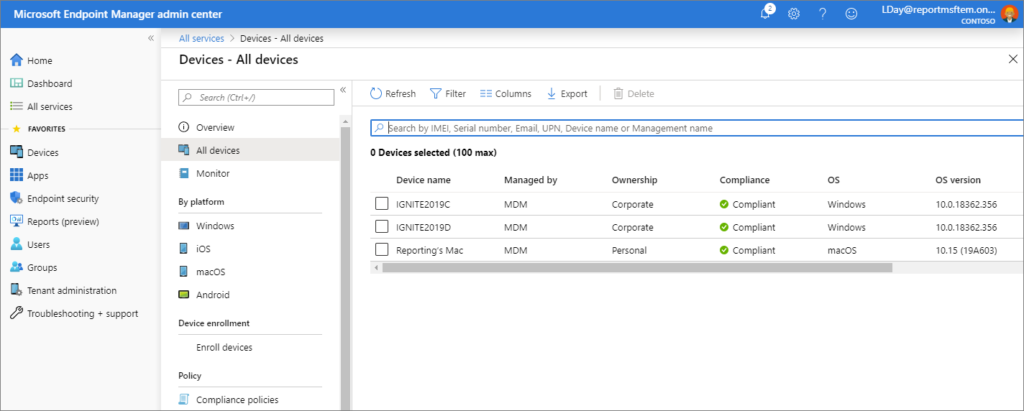
Mobile device management is a solution to this problem as it maintains a connection between the laptop and the cloud server. MDM can collect various parameters from hosts, but for me the most important parameter is the timestamp. I will not describe all the features of Microsoft Intune here. Simply because at this stage they are not very interesting to me. The task I needed to solve was how to get the timestamp of the last activity for all hosts in Microsoft Intune using the official API. And since this is poorly documented, I want to share it with you.



![Elevation of Privilege - Sudo (CVE-2021-3156) - High [595]](https://avleonov.com/wp-content/uploads/2021/03/image-2.png)