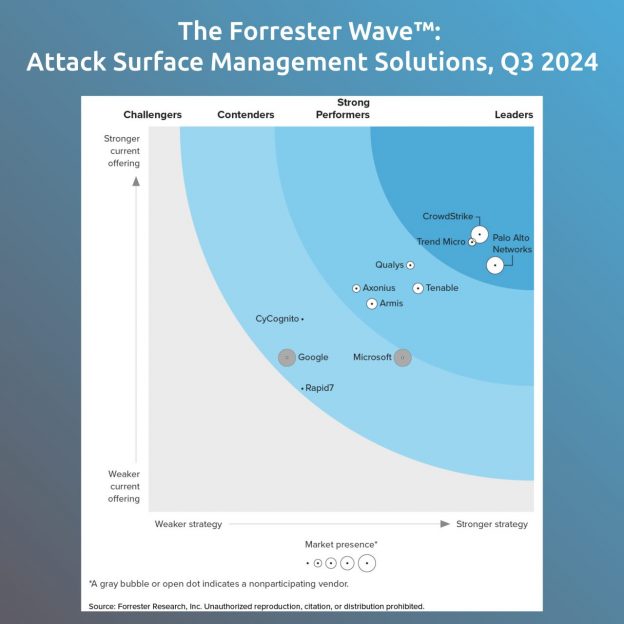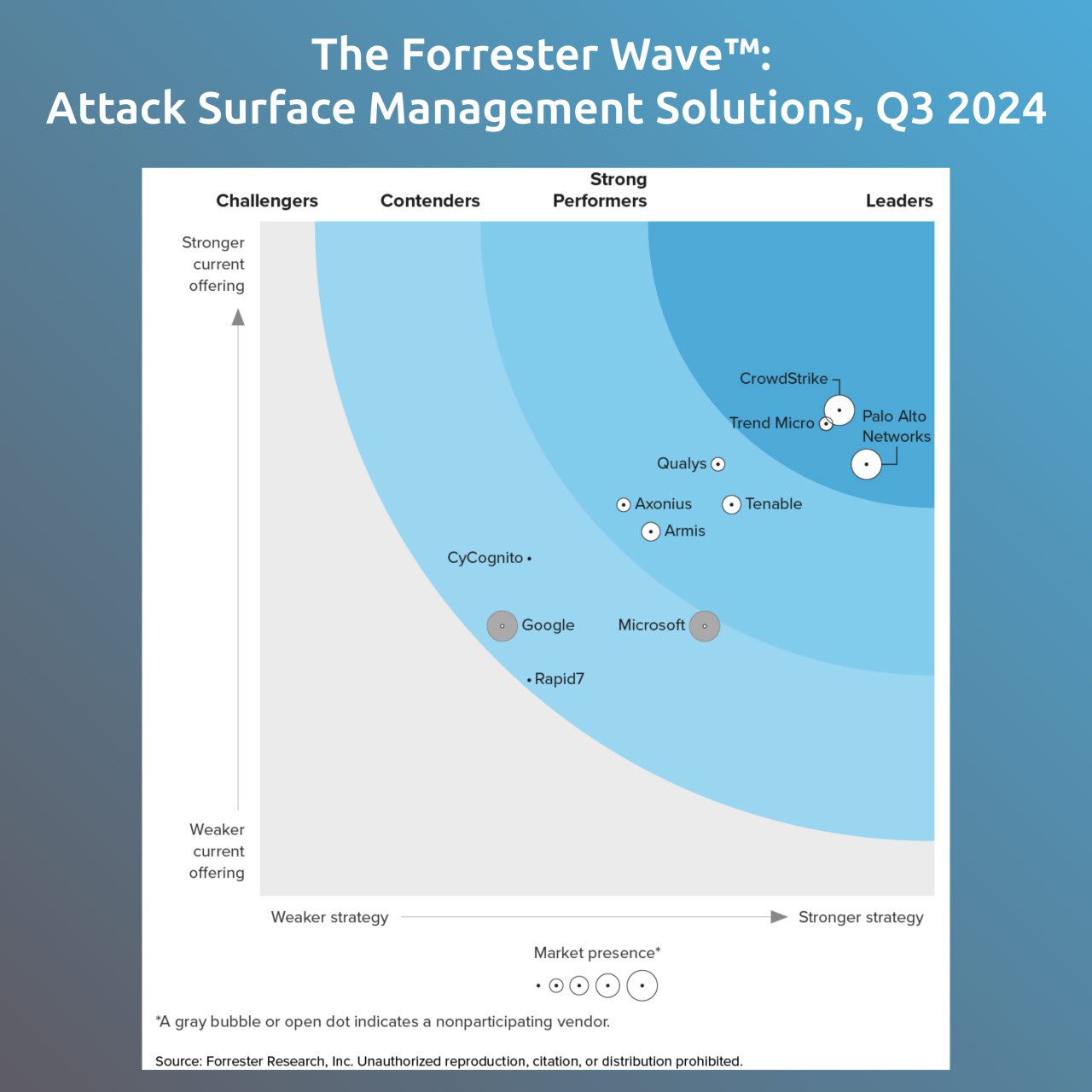
I looked at the Forrester Wave on ASM for Q3 2024. The reprint was posted by Trend Micro. Forrester understands ASM to be something that evolved from EASM or CAASM. “Attack surface management […] gives you a depiction of what is attackable and whether it’s being monitored and hardened appropriately”. The goal is to provide a complete cyber asset inventories. So is this a kind of view on Asset Management from the information security side (like Qualys CSAM)? 🤔
CrowdStrike, Palo Alto Networks and Trend Micro are among the Leaders. And traditional vendors with vulnerability detection expertise either in Strong Perfomers (Qualys, Tenable), or even in Contenders (Rapid7).
IMHO, this happened because the assessment focused on CAASM, not EASM features. For example, there is nothing about vulnerability detection for network perimeter. And the criteria are rather vague, like “Cyber asset inventory: asset contextualization” or “Srategy: Vision”. 😉