F-Secure Radar ticketing. I personally don’t use ticketing systems integrated in VM solutions. I think it’s hard to explain IT guys why they should use yet another ticketing system for patching tasks only additionally to their main Jira or whatever they use (see “Vulnerability scanners: a view from the vendor and end user side“).
But I assume that for some companies this feature may be useful or even critical.
Anyway, it’s always nice to see how the vendor works with vulnerability data to get some ideas for own ticketing procedures (see “VM Remediation using external task tracking systems“).
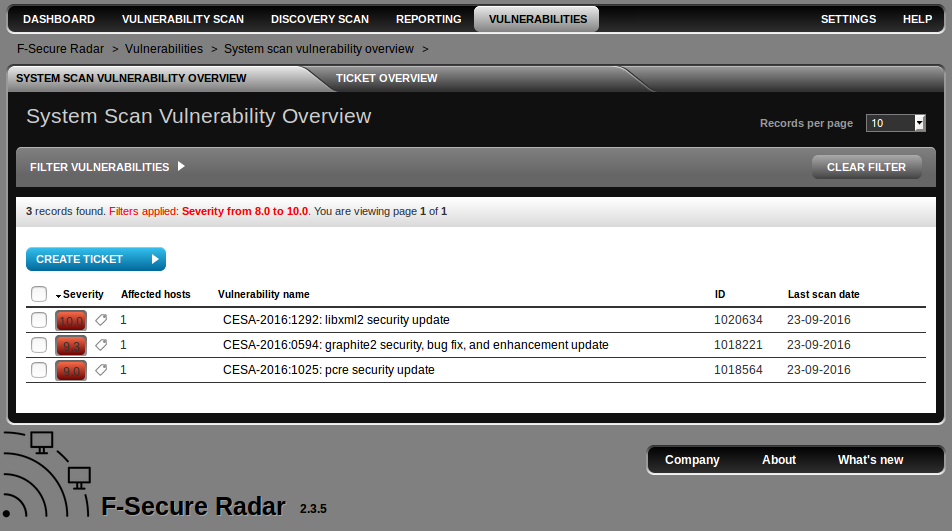
In F-Secure Radar you can create tickets at “Vulnerabilities” tabs. Here is the a whole list of detected vulnerabilities (filtered by CVSS > 8 by default).