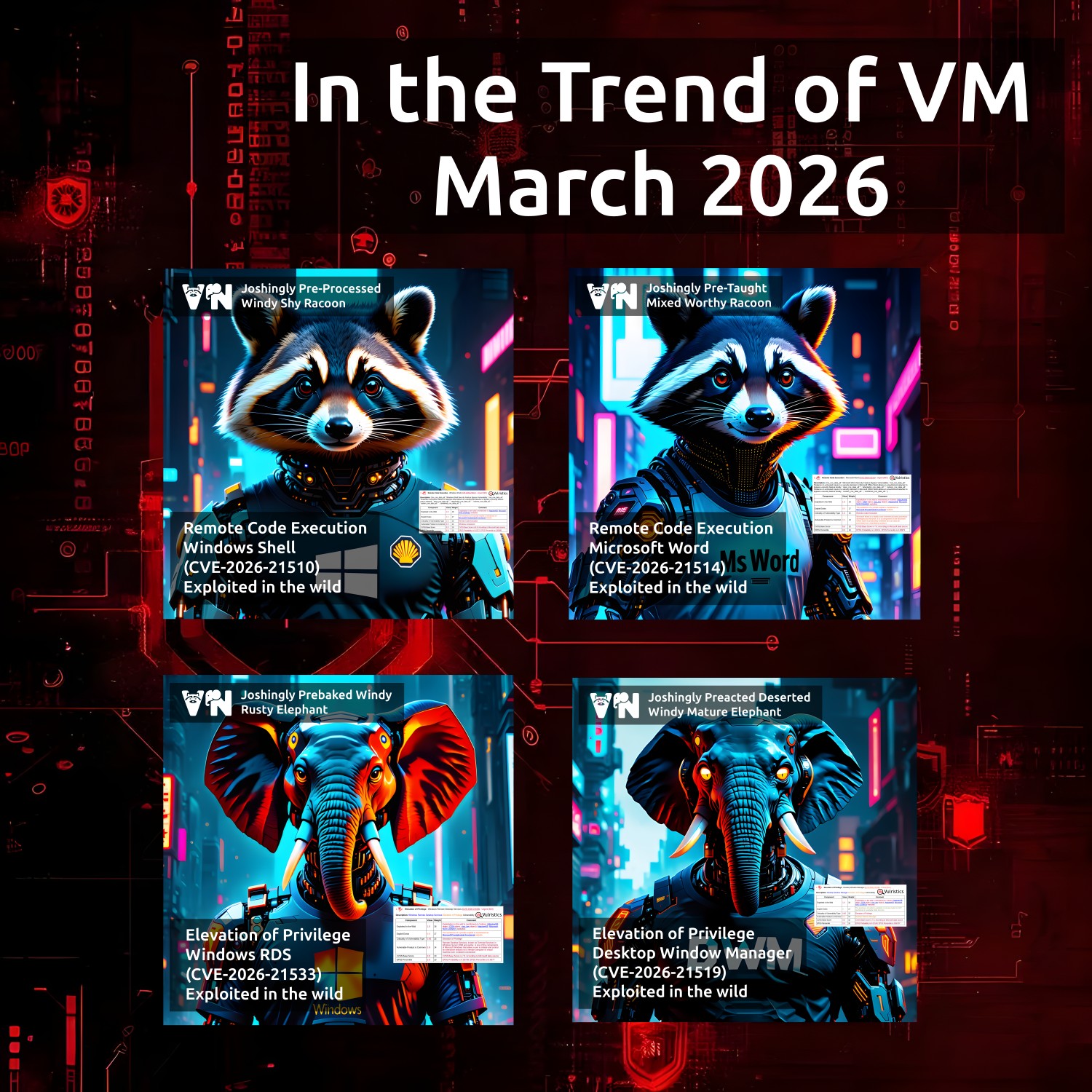
March “In the Trend of VM” (#25): once again, vulnerabilities are only in Microsoft products. I present the traditional monthly roundup of trending vulnerabilities according to Positive Technologies. As in February, it turned out to be quite compact and focused on a single vendor.
🗞 Post on Habr (rus)
🗒 Digest on the PT website (rus)
All four vulnerabilities are from the February Microsoft Patch Tuesday, and all are actively being exploited in the wild:
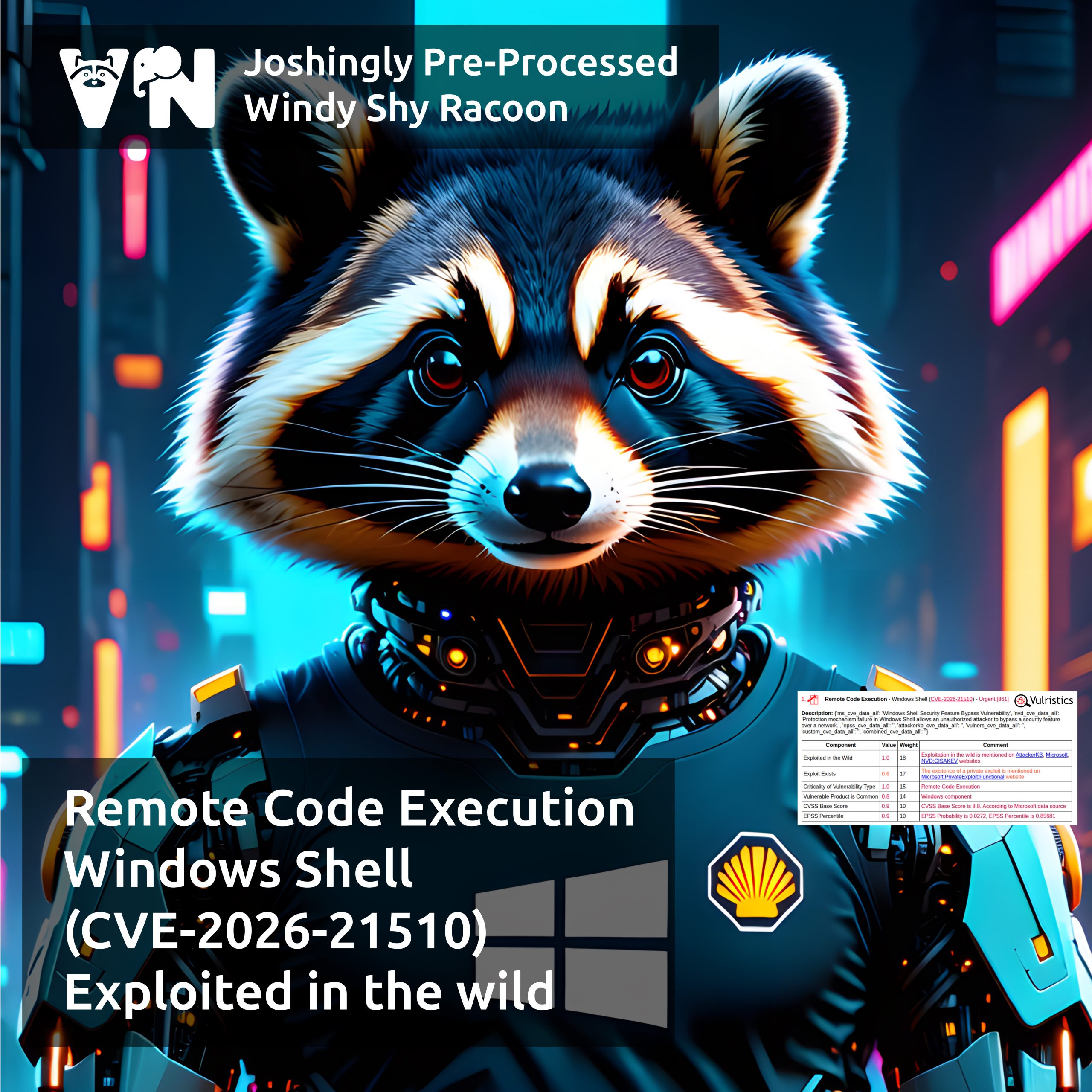
🔻 RCE – Windows Shell (CVE-2026-21510)
🔻 RCE – Microsoft Word (CVE-2026-21514)
💬 Microsoft classified the two vulnerabilities above as Security Feature Bypass, but in fact, they are Remote Code Execution.
🔻 EoP – Windows Remote Desktop Services (CVE-2026-21533)
🔻 EoP – Desktop Window Manager (CVE-2026-21519)
🟥 The full list of trending vulnerabilities can be found on the portal