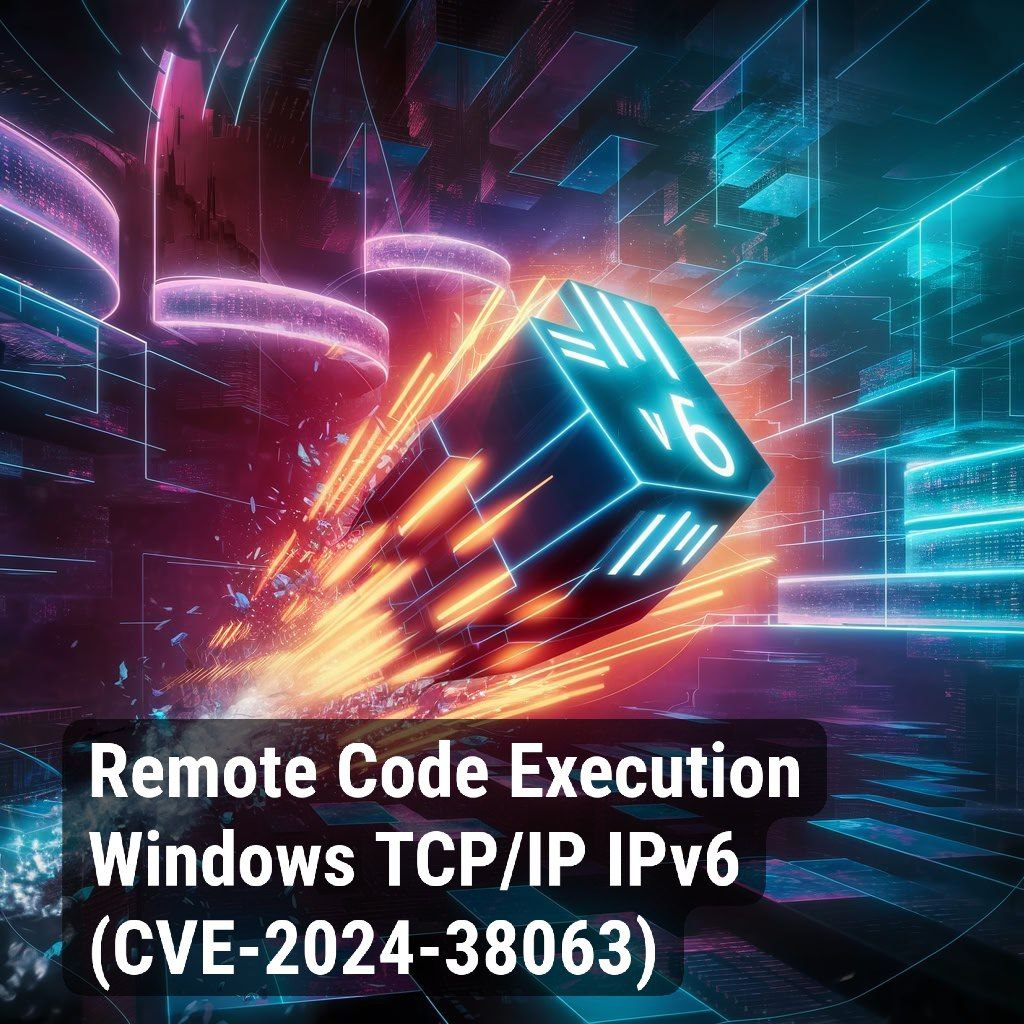
I found that the research data for Remote Code Execution – Windows Remote Desktop Licensing Service “MadLicense” (CVE-2024-38077), which I wrote about 3 weeks ago, was deleted. Both on GitHub and on Google Sites.
And what does this all mean? 🤔 Who knows. 🤷♂️ Considering that it disappeared on two platforms at once, it was probably deleted by the Chinese researchers themselves. Why did they do this? Perhaps they established a dialogue with Microsoft and MS asked them to remove everything from the public (which, of course, is stupid – the Internet remembers everything). Perhaps someone else asked them to do this. 🫡 Another reason to pay attention to this vulnerability.