PHDays8: Digital Bet and thousands tons of verbal ore. It’s time to write about Positive Hack Days 8: Digital Bet conference, which was held May 15-16 at the Moscow World Trade Center. It was the main Russian Information Security event of the first half of 2018. More than 4 thousand people attended! More than 50 reports, master classes and round tables held in 7 parallel streams. And, of course, impressive CTF contest for security experts and hackers with an fully-functioning model of the city.

I was very pleased that there was a separate section dedicated to Vulnerability Management. Something similar happened only at ISACA meetup last year. But here we had an event for several thousand people!
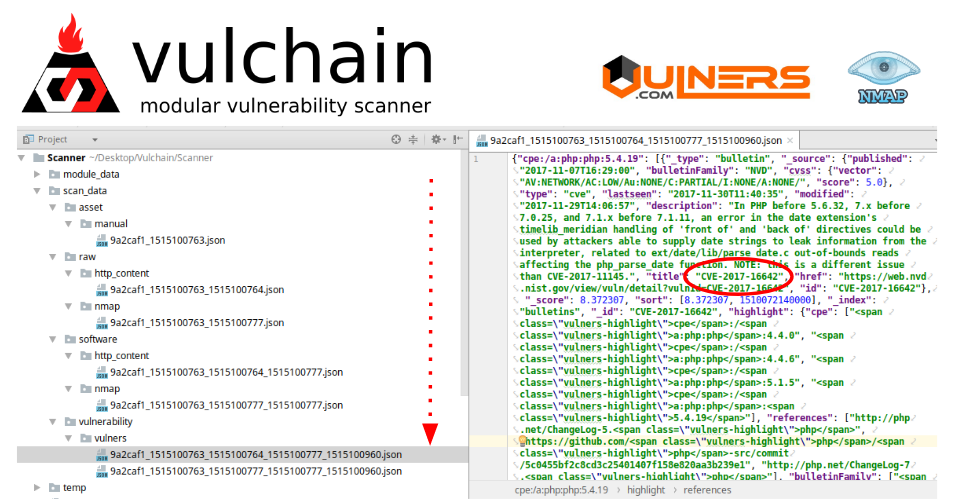
The session was held in Fast Track format: 20 minutes for the presentation and questions. I was the first to speak. My report was called “Vulnerability Databases: sifting thousands tons of verbal ore”. Here is the video:
And here’s a link to the version with only Russian sound track.