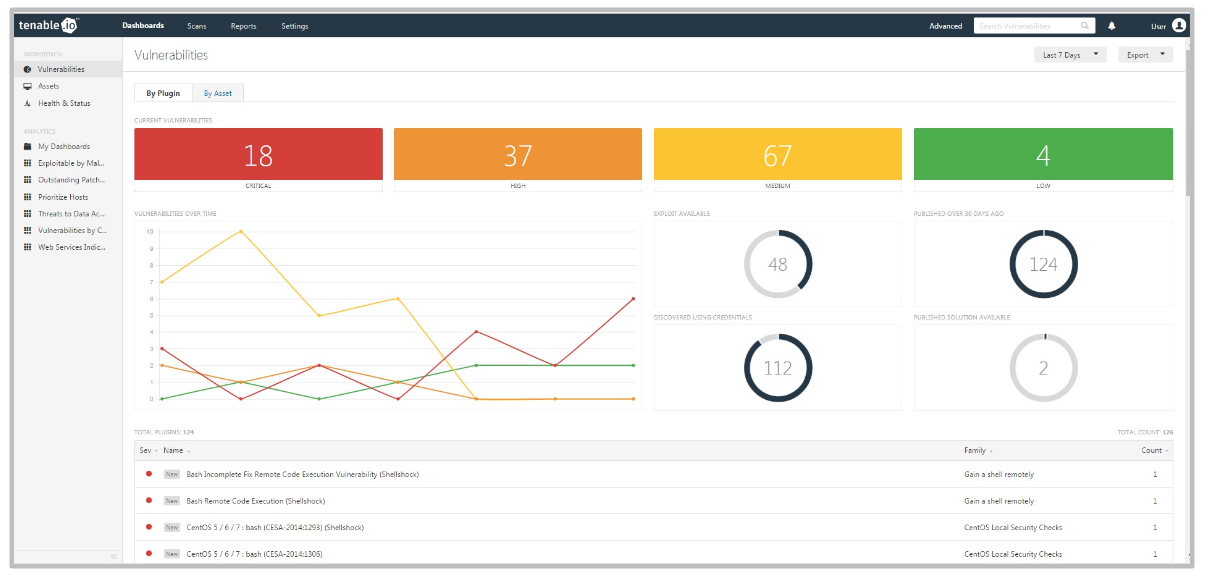
What I expect from IT Asset Inventory. The main problem of vulnerability management, in my opinion, is that it is not always clear whether we know about ALL network hosts existing in our infrastructure or not. So, not the actual process of scanning and the detection of vulnerabilities, but the lack of knowledge what we should scan.
Knowing the total number of active hosts, this must be such a simple and basic thing. But for a large organization, this is not so trivial. To tell the truth, I do not know how to do IT Asset Inventory right. I’m not even sure who should be responsible this. There are so many different technological and organizational nuances. I will mention some of them below.
But I can say with confidence that my basic requirement for IT Asset Inventory system will be the completeness of the scope, not the number of collected parameters. The very minimum is just to see that some network host existed and seemed active at some time.