Add new features to Notepad++ using Python scripts: keyboard shortcut to insert current time. I have to say, I spend a lot of time daily in Notepad++ text editor for Windows. I keep my “logbook” there. I record what I am doing now and what needs to be done. This allows me not to keep everything in my head and switch the context more efficiently. I can recommend this to everyone. And it is especially useful to note when you started working on a task and when you finished. This gives an understanding of what actually takes your time. I’m not a fan of very strict and formal techniques such as pomodoro, but using some form of time management is good.
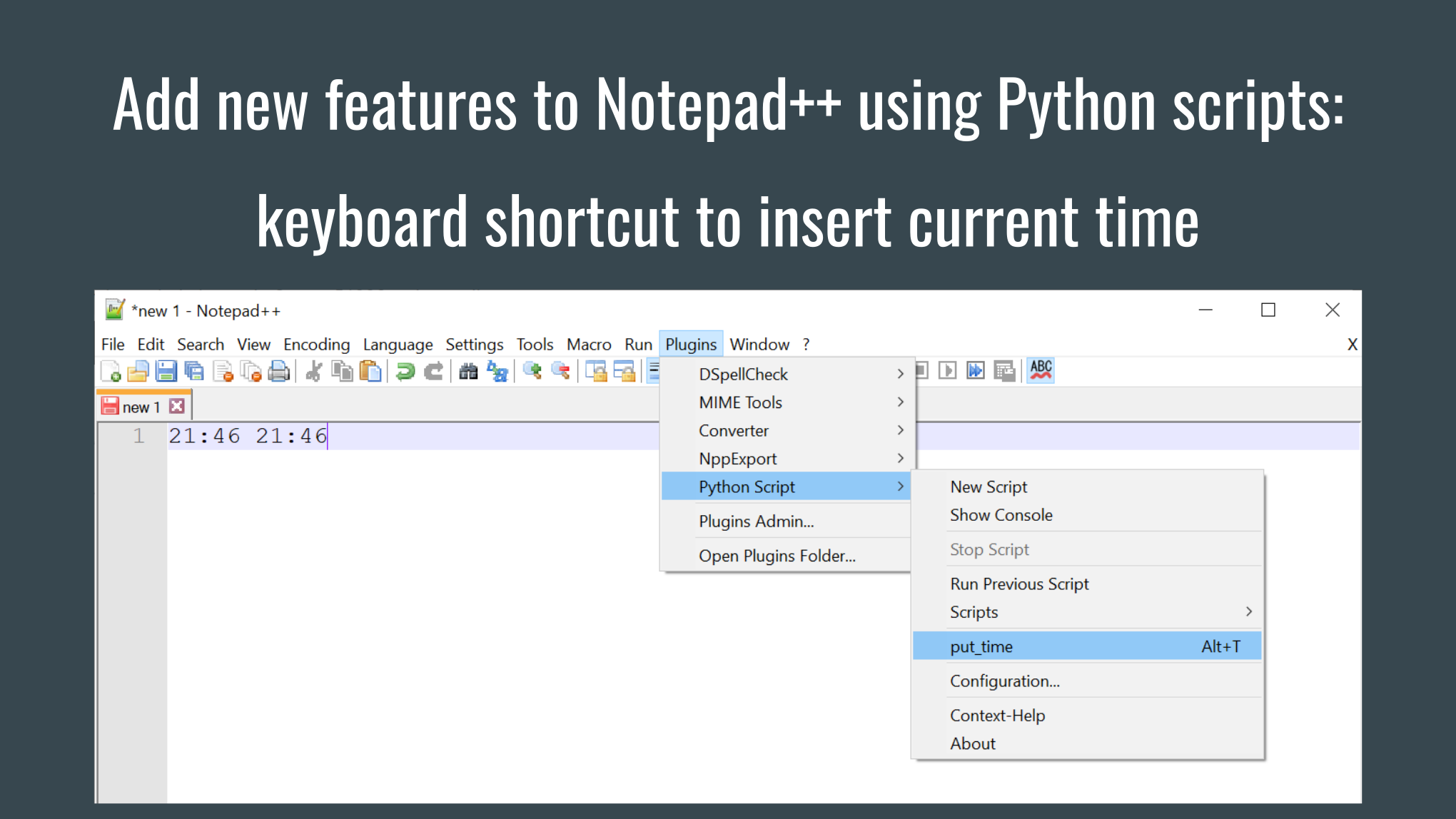
Recording timestamps manually is inconvenient. It would be much easier to press a key combination and automatically insert the current timestamp into the document. It turned out that this is possible, and even more – you can get the results of any Python script this way!