New episode “In The Trend of VM” (#9): 4 trending vulnerabilities of October, scandal at The Linux Foundation, social “attack on the complainer”, “Ford’s method” for motivating IT specialists to fix vulnerabilities. The competition for the best question on the topic of VM continues. 😉🎁
📹 Video on YouTube, LinkedIn
🗞 Post on Habr (rus)
🗒 Digest on the PT website
Content:
🔻 00:37 Elevation of Privilege – Microsoft Streaming Service (CVE-2024-30090)
🔻 01:46 Elevation of Privilege – Windows Kernel-Mode Driver (CVE-2024-35250)
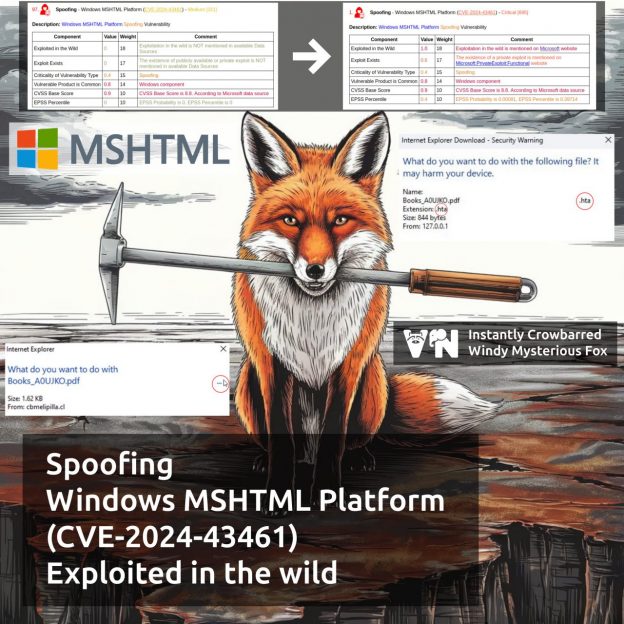
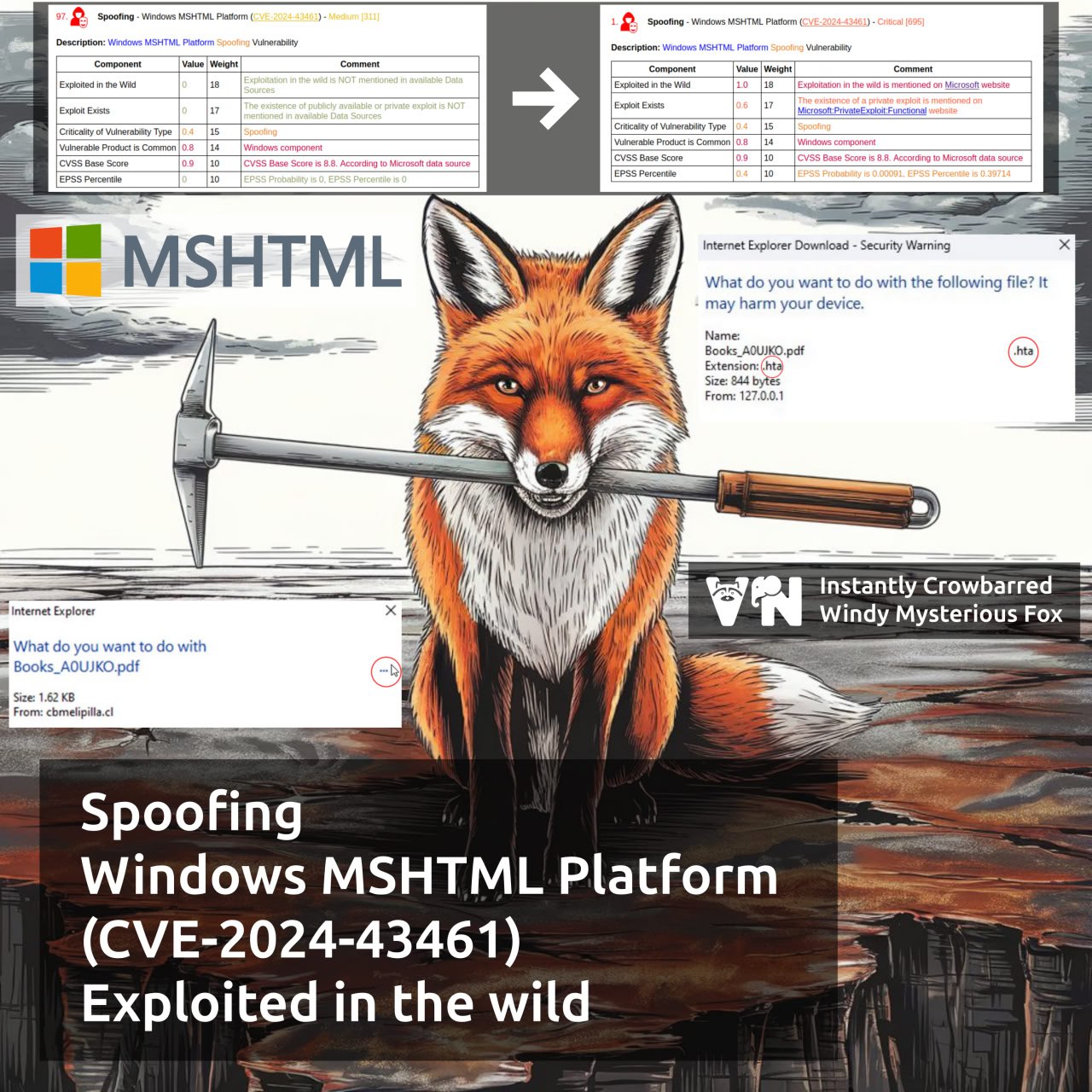
🔻 02:38 Spoofing – Windows MSHTML Platform (CVE-2024-43573)
🔻 03:43 Remote Code Execution – XWiki Platform (CVE-2024-31982)
🔻 04:44 The scandal with the removal of Russian maintainers at The Linux Foundation, its impact on security and possible consequences.
🔻 05:22 Social “Attack on the complainer“
🔻 06:35 “Ford’s method” for motivating IT staff to fix vulnerabilities: will it work?
🔻 08:00 About the digest, habr and the question contest 🎁
🔻 08:29 Backstage