January “In the Trend of VM” (#23): vulnerabilities in Windows, React and MongoDB. Traditional monthly roundup of trending vulnerabilities. Launching the 2026 season. 🙂
🗞 Post on Habr (rus)
🗒 Digest on the PT website (rus)
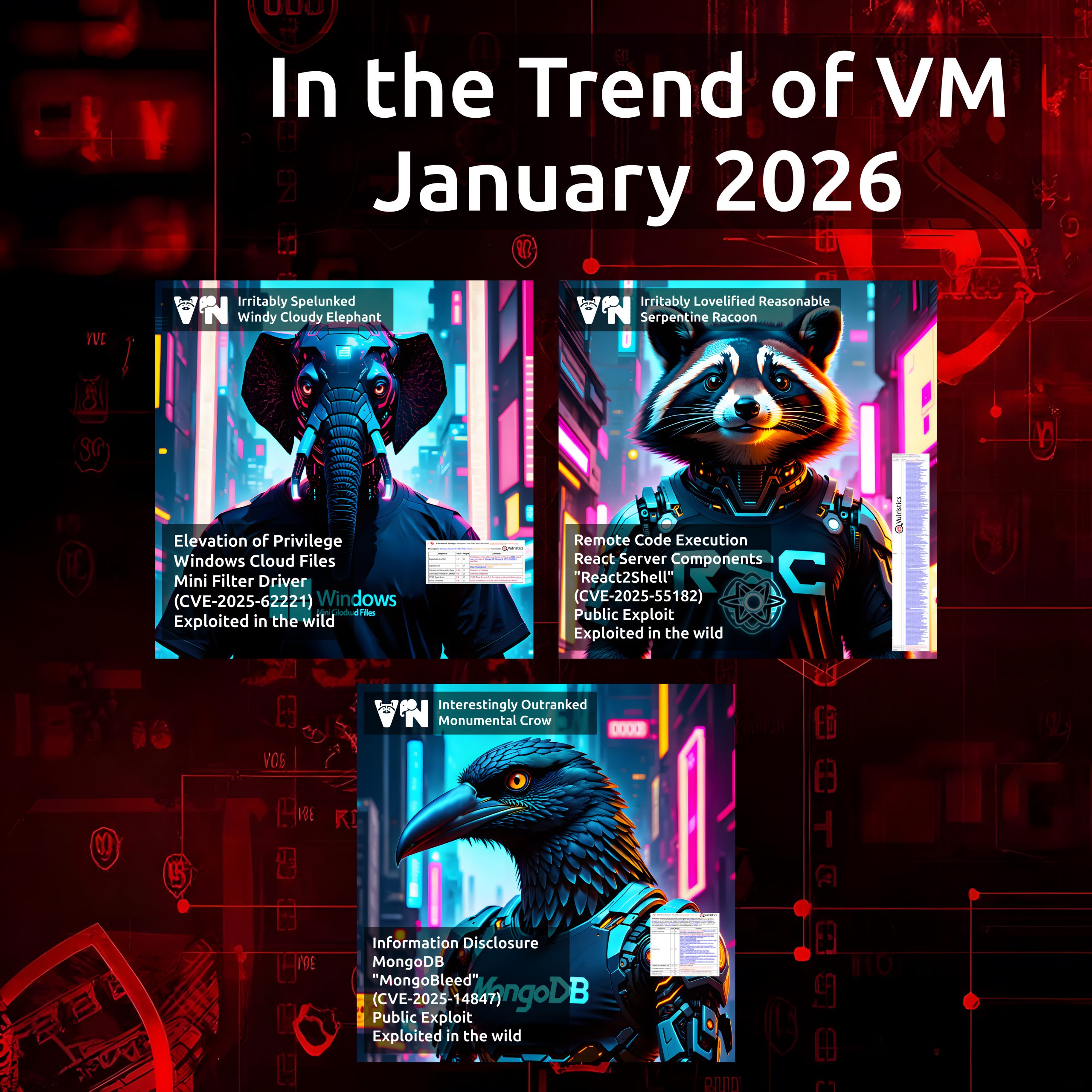
In total, three vulnerabilities:
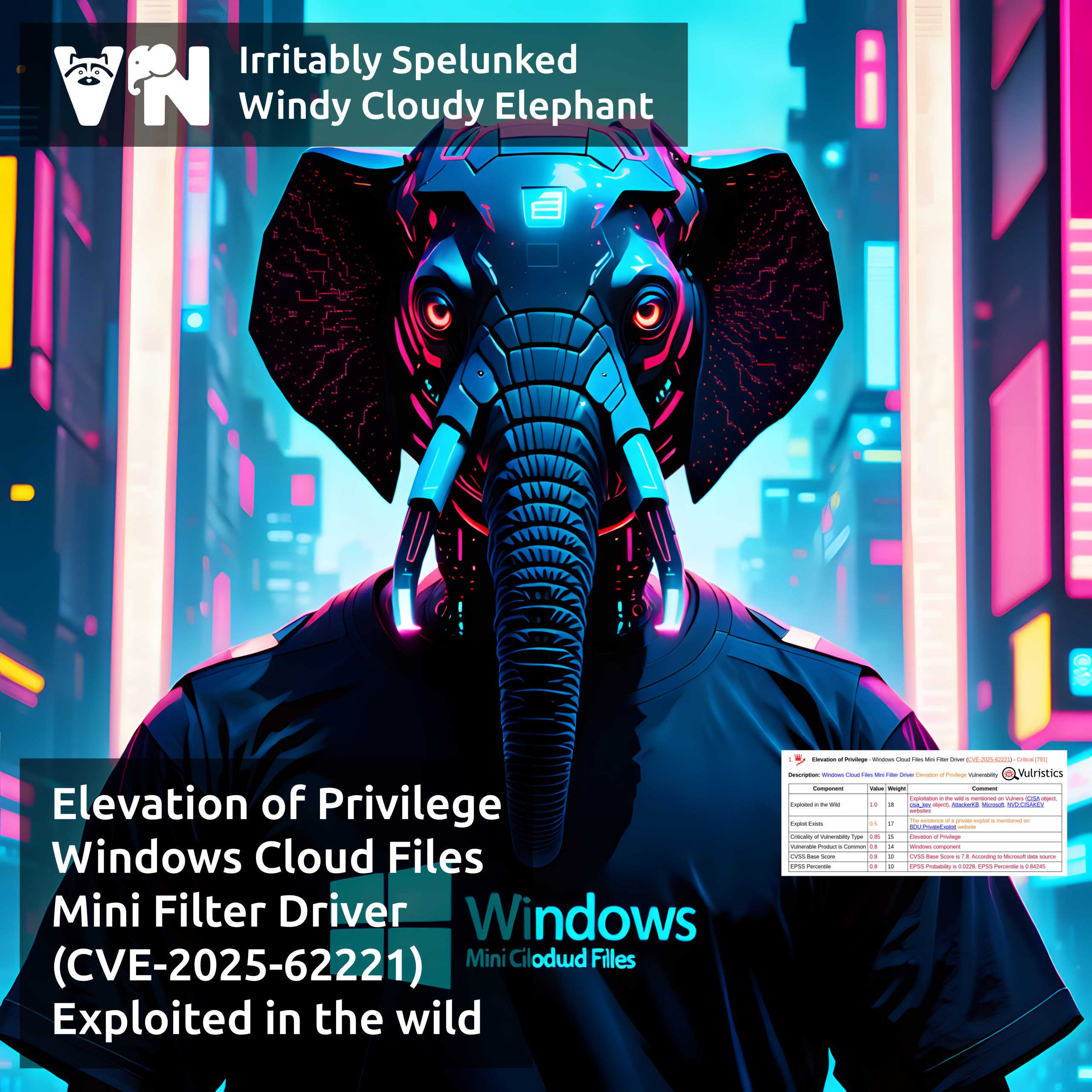
🔻 EoP – Windows Cloud Files Mini Filter Driver (CVE-2025-62221)
🔻 RCE – React Server Components “React2Shell” (CVE-2025-55182)
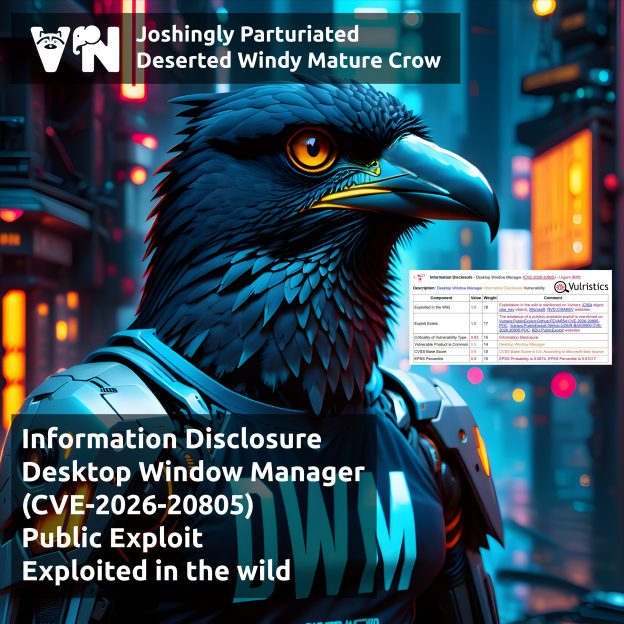
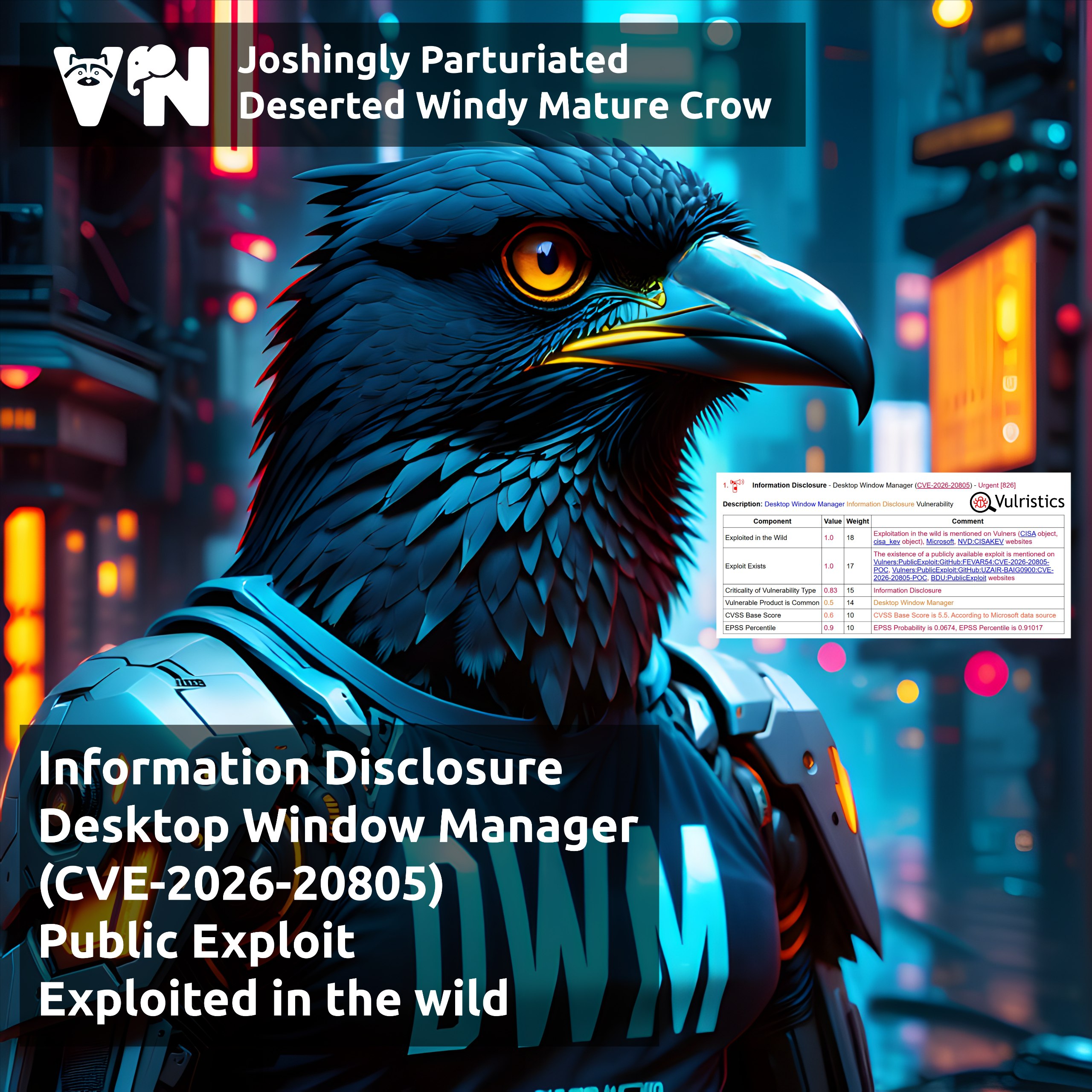
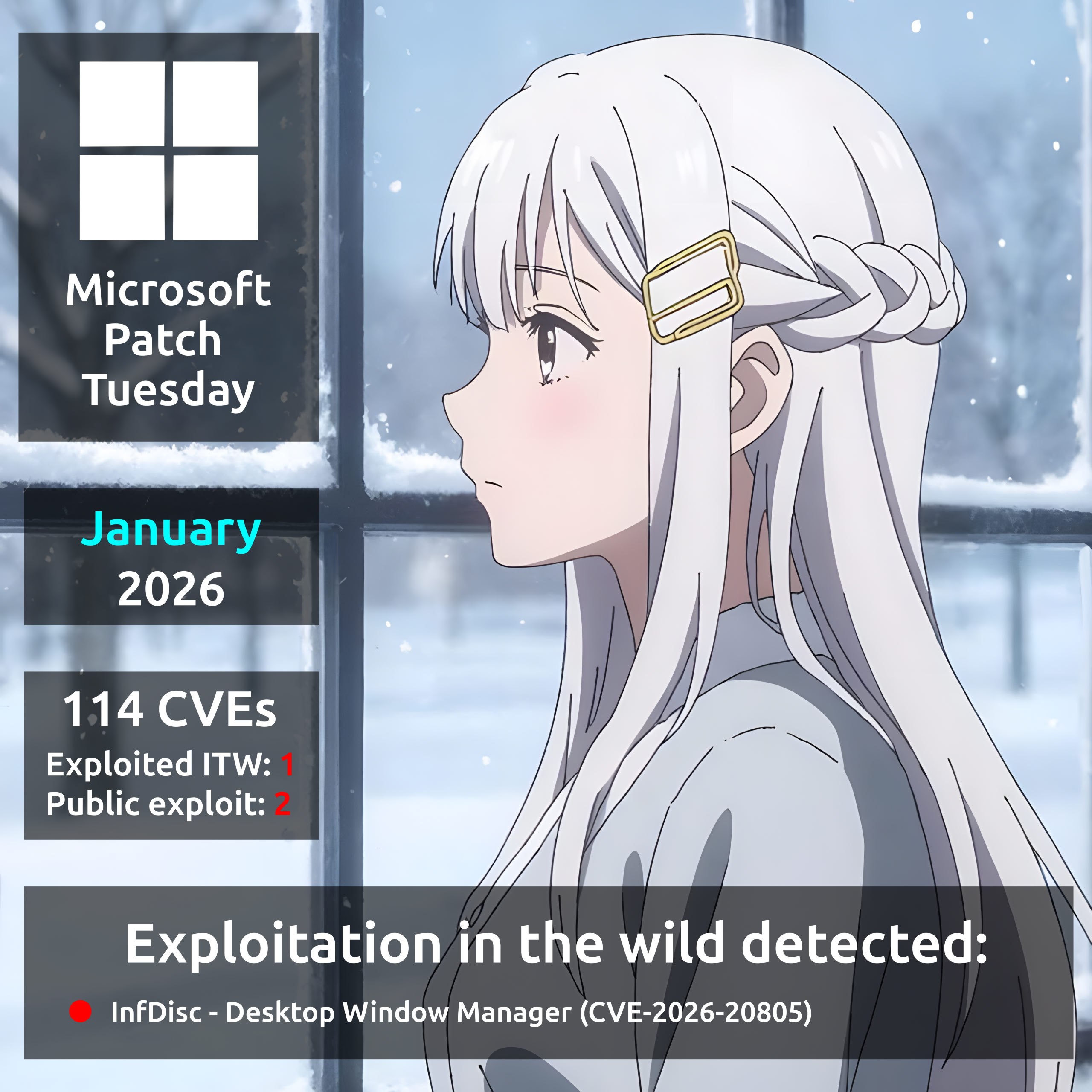
🔻 InfDisc – MongoDB “MongoBleed” (CVE-2025-14847)