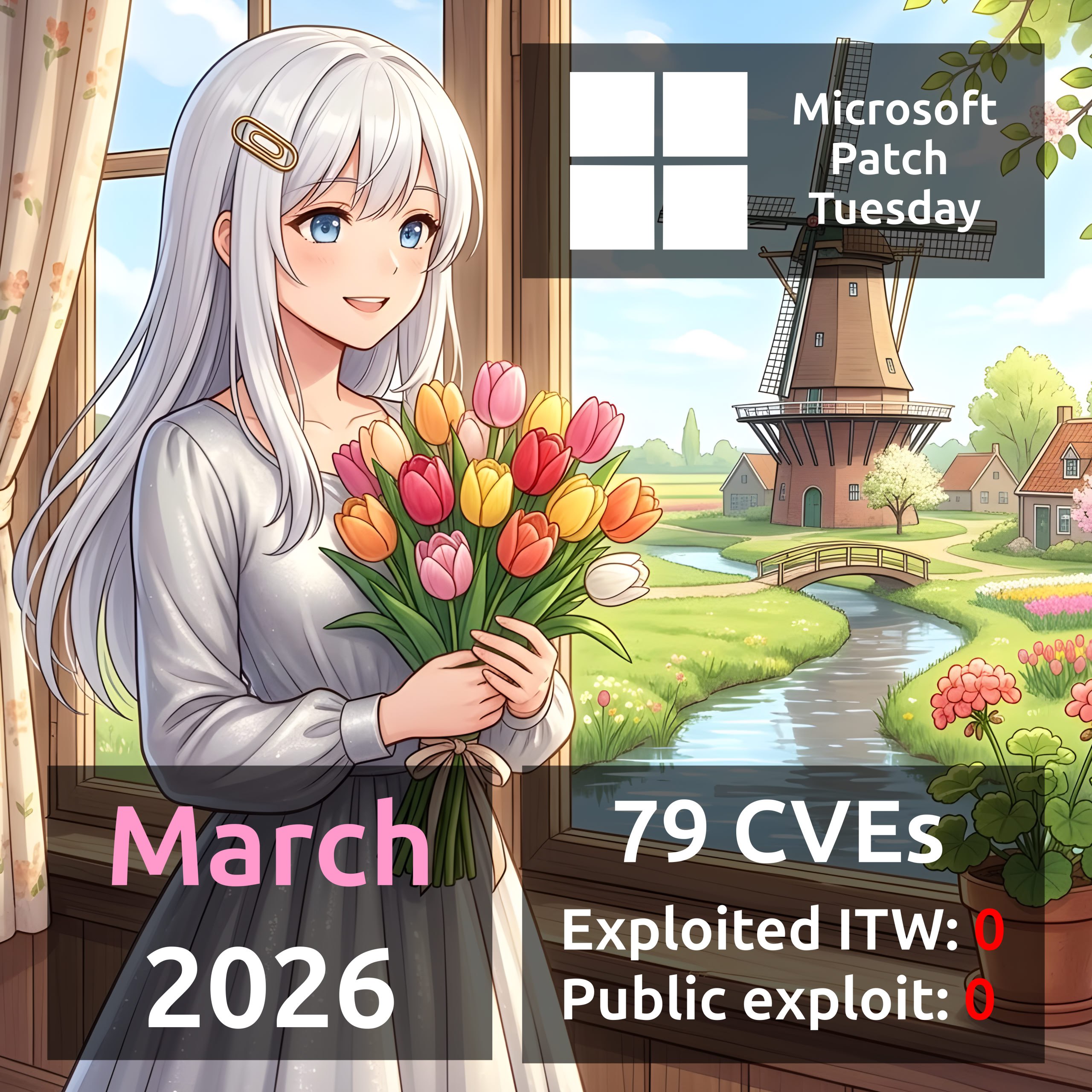
March Microsoft Patch Tuesday. A total of 79 vulnerabilities, about one and a half times more than in February. What’s truly unusual is that this time there were no vulnerabilities with signs of exploitation in the wild or a public exploit! 🤔 At least not yet. 😏
The following vulnerabilities can be highlighted:
🔹 RCE – Print Spooler (CVE-2026-23669), Office (CVE-2026-26110, CVE-2026-26113), Excel (CVE-2026-26107, CVE-2026-26108, CVE-2026-26109, CVE-2026-26112), SharePoint Server (CVE-2026-26106, CVE-2026-26114)
🔹 EoP – SQL Server (CVE-2026-21262, CVE-2026-26115, CVE-2026-26116), Windows Kernel (CVE-2026-24287, CVE-2026-24289, CVE-2026-26132), Windows Win32k (CVE-2026-24285), SMB Server (CVE-2026-24294, CVE-2026-26128), Windows Graphics Component (CVE-2026-23668), .NET (CVE-2026-26131)
🔹 DoS – .NET (CVE-2026-26127)