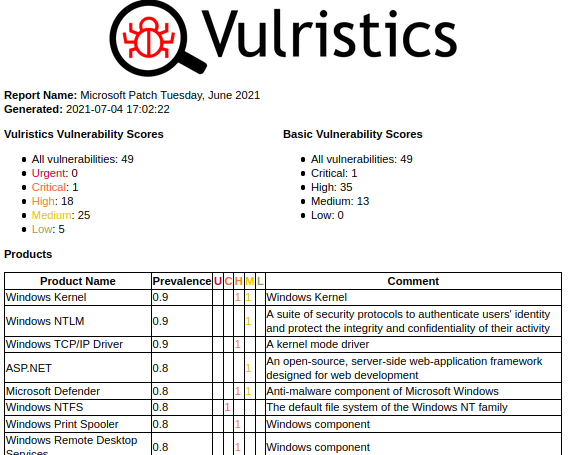
Vulristics: Microsoft Patch Tuesdays Q2 2021. Hello everyone! Let’s now talk about Microsoft Patch Tuesday vulnerabilities for the second quarter of 2021. April, May and June. Not the most exciting topic, I agree. I am surprised that someone is reading or watching this. For me personally, this is a kind of tradition. Plus this is an opportunity to try Vulristics in action and find possible problems. It is also interesting to see what VM vendors considered critical back then and what actually became critical. I will try to keep this video short.
First of all, let’s take a look at the vulnerabilities from the April Patch Tuesday. 108 vulnerabilities, 55 of them are RCEs. Half of these RCEs (27) are weird RPC vulnerabilities. “Researcher who reported these bugs certainly found quite the attack surface”. The most critical vulnerability is RCE in Exchange (CVE-2021-28480). This is not ProxyLogon, this is another vulnerability. ProxyLogon was in March. And this vulnerability is simply related to ProxyLogon, so it is believed that it is exploited in the wild as well. In the second place this Win32k Elevation of Privilege (CVE-2021-28310). It is clearly mentioned in several sources as being used in real attacks. “Bugs of this nature are typically combined with other bugs, such as a browser bug or PDF exploit, to take over a system”. And the only vulnerability with a public exploit is the Azure DevOps Server Spoofing (CVE-2021-28459). Previously known as Team Foundation Server (TFS), Azure DevOps Server is a set of collaborative software development tools. It is hosted on-premises. Therefore, this vulnerability can be useful for attackers.