PHDays VII: To Vulnerability Database and beyond. Last Tuesday and Wednesday, May 23-24, I attended PHDays VII conference in Moscow. I was talking there about vulnerability databases and the evolution process of vulnerability assessment tools, as far as I understand it.

But first of all, a few words about the conference itself. I can tell that since the last year the event got even better. I’ve seen lot of new faces. Some people I didn’t know, but they knew me by my blog and accounts in social networks. What a strange, strange time we live in! I was very pleased to see and to talk with you all, guys! 🙂
PHDays is one of the few events that truly brings all Russian community of security professionals together. I’ve seen people I have studied with in university, colleagues from the all places where I have been worked, and nearly all researchers and security practitioners that I follow. Big thanks for the organizers, Positive Technologies, for such an amazing opportunity!
It is also a truly international event. You can see speakers from all over the world. And all information is available both in Russian and English. Almost all slides are in English. Three parallel streams of reports, workshops and panel discussions were dubbed by professional simultaneous interpreters, like it is a United Nations sessions or something, recorded and broadcast live by the team of operators and directors. Final result looks really great.
Video of my presentation:
I was talking too fast and used some expressions that was hard to translate. The translator, however, did an awesome job. He is my hero! 🙂 If you didn’t understand something on video, I made a transcript bellow.
A version without translation for Russian-speakers is here.
Slides:
Unfortunately gif animation is not working in the Slideshare viewer.
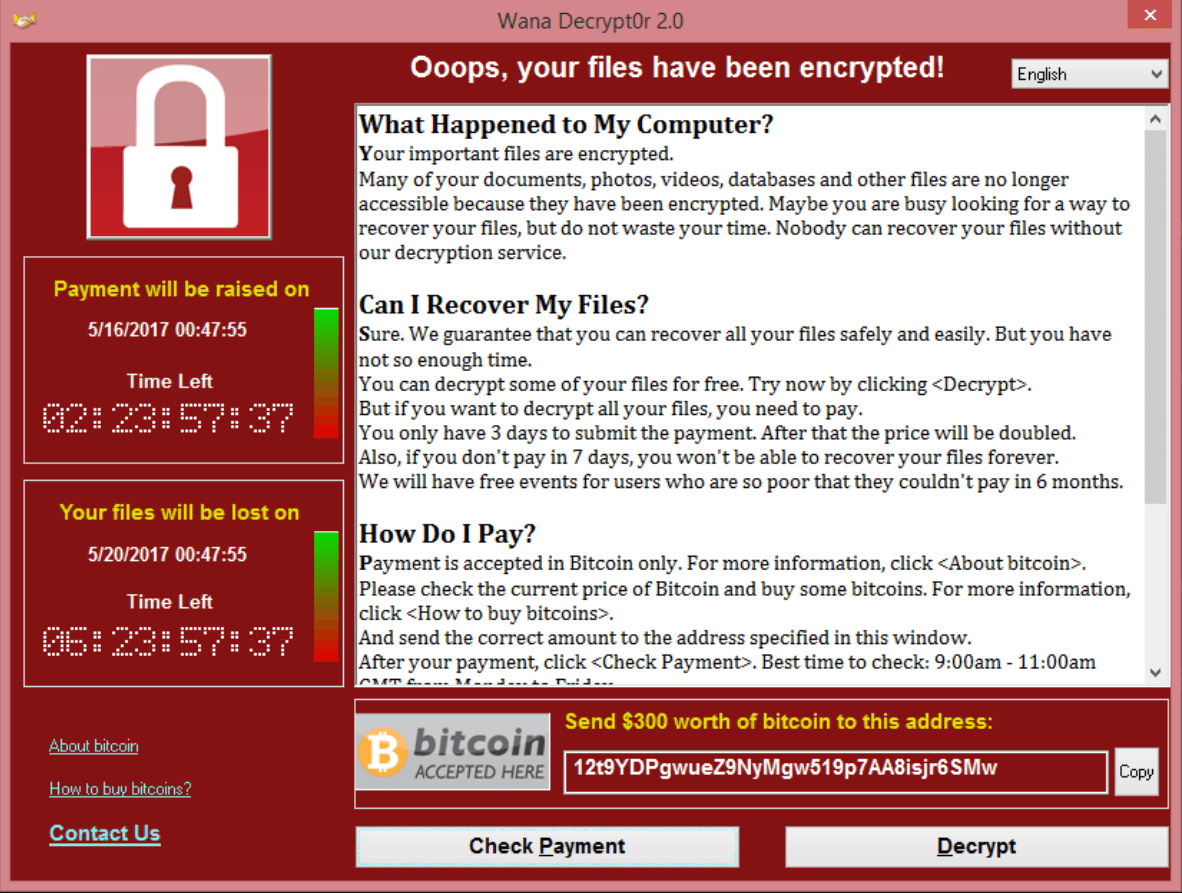
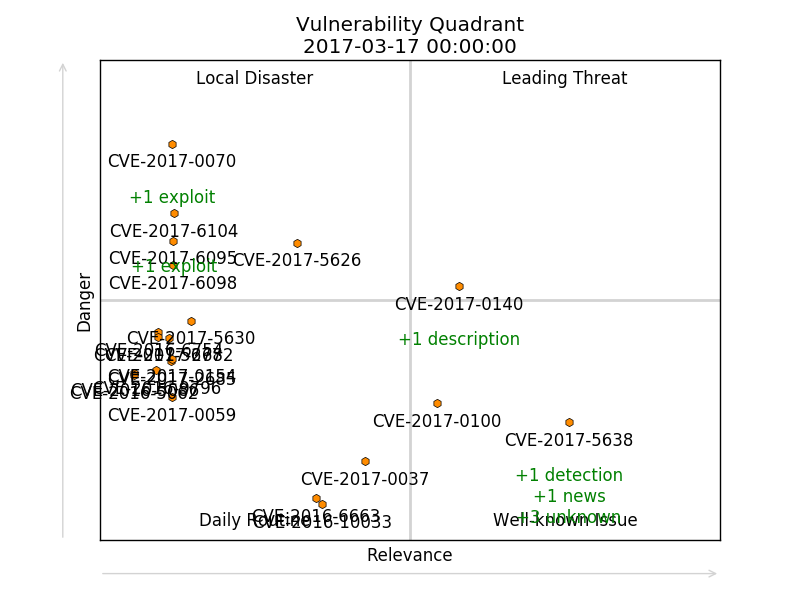
Today I would like to discuss vulnerability databases and how vulnerability assessment systems has been evolving. Prior to discussing vulnerability databases I need to say that any vulnerability is just a software error, a bug, that allowing hacker to do some cool things. Software developers and vendors post information about such vulnerabilities on their websites. And there are tons and tones of vendors, and websites, and software products, and vulnerabilities.