Processing Vulners collections using Python. Vulners collection is a zip archive containing all available objects of some type (e.g. CentOS security bulletins or OpenVAS detection plugins) from the Vulners Knowledge Base. Let’s see how to work with this data using powerful Python scripting language. You can read more about Vulners itself at “Vulners – Google for hacker“.

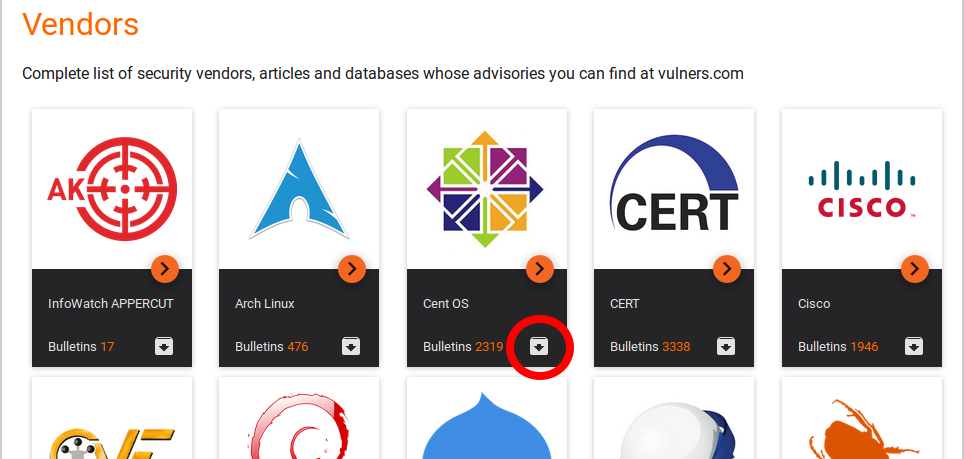
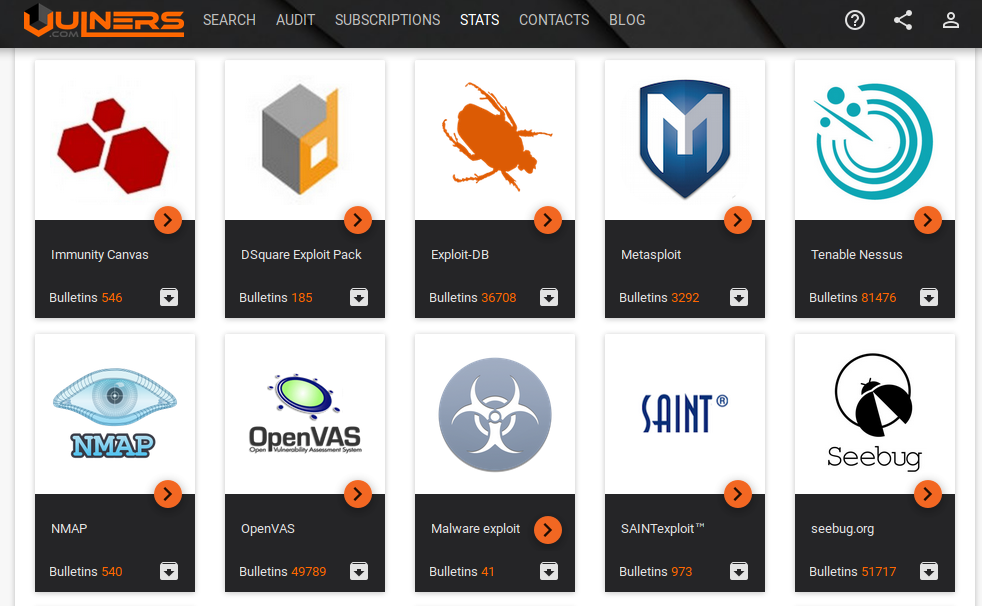
All collections are listed at https://vulners.com/#stats:
Note a gray icon with black arrow. Press it to download particular vulners collection.
OpenVAS collection link: https://vulners.com/api/v3/archive/collection/?type=openvas
If you need to get all objects for further analysis, you don’t need to make huge amount simmilar Search API requests. You just need to download one file. It’s takes less time and efforts and makes less load on Vulners service.
Continue reading