VMconf 22: Blindspots in the Knowledge Bases of Vulnerability Scanners. Hello everyone! This video was recorded for the VMconf22 Vulnerability Management conference. I want to talk about the blind spots in the knowledge bases of Vulnerability Scanners and Vulnerability Management products.
This report was presented in Russian at Tenable Security Day 2022. The video is here.
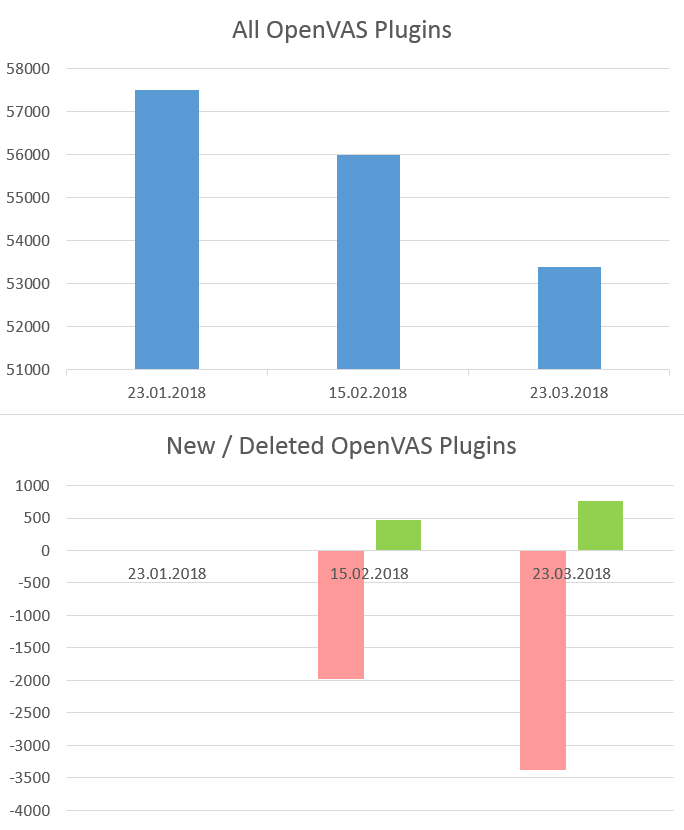
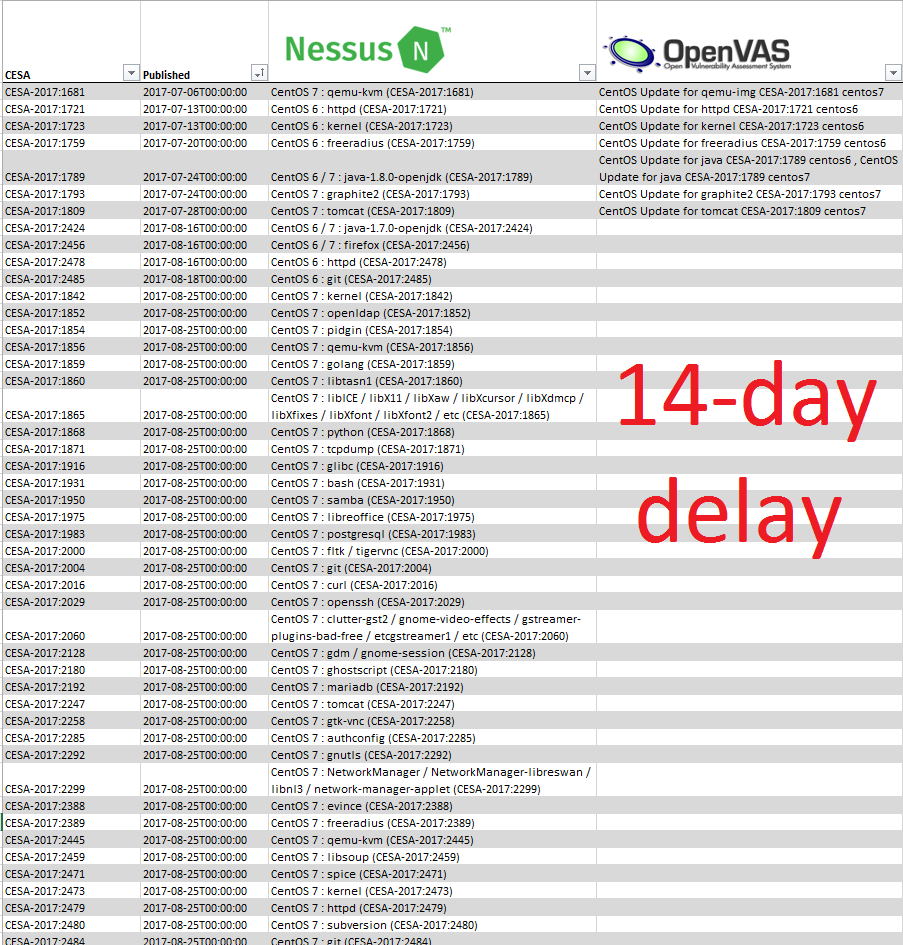
Potential customers rarely worry about the completeness of the Knowledge Base when choosing a Vulnerability Scanner. They usually trust the VM vendors’ claims of the “largest vulnerability base” and the total number of detection plugins. But in fact the completeness is very important. All high-level vulnerability prioritization features are meaningless unless the vulnerability has been reliably detected. In this presentation, I will show the examples of blindspots in the knowledge bases of vulnerability management products, try to describe the causes and what we (as customers and the community) can do about it.