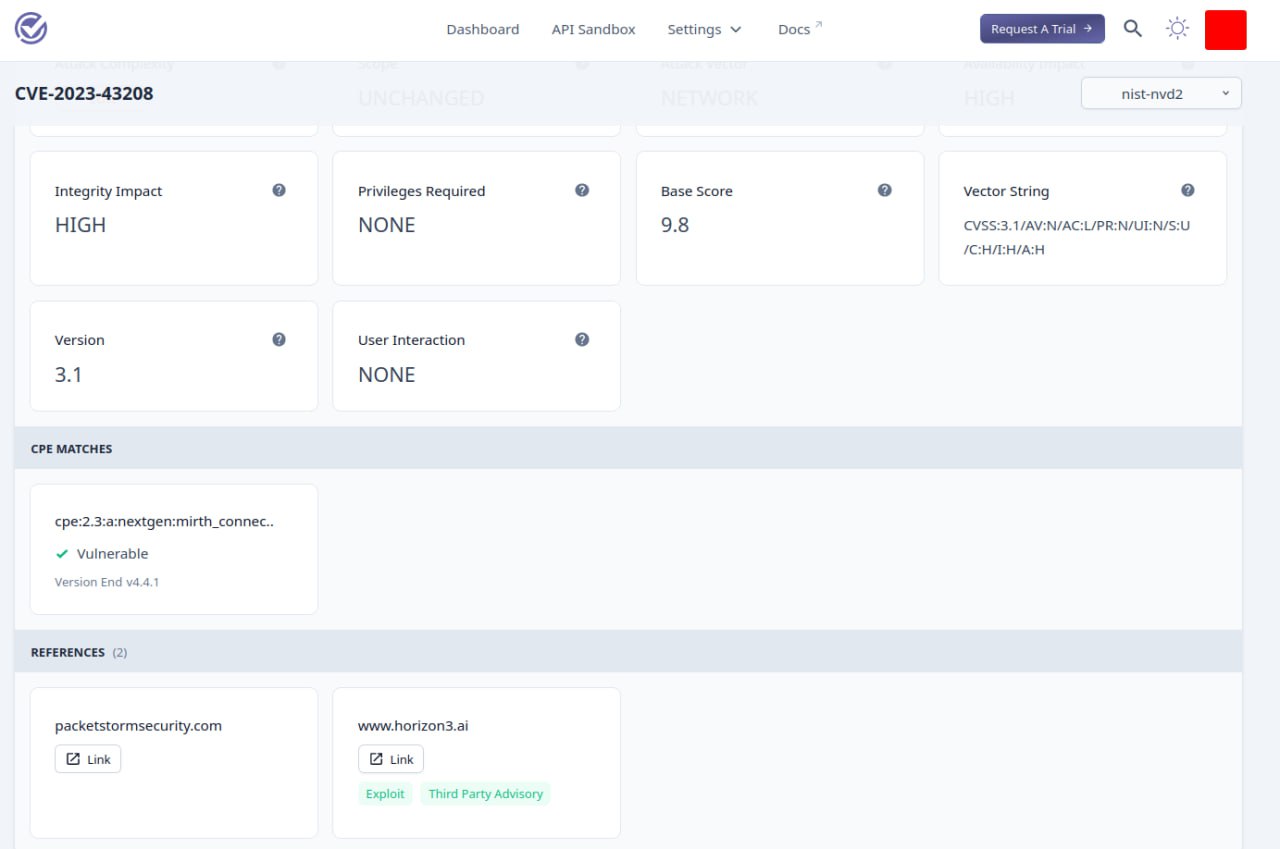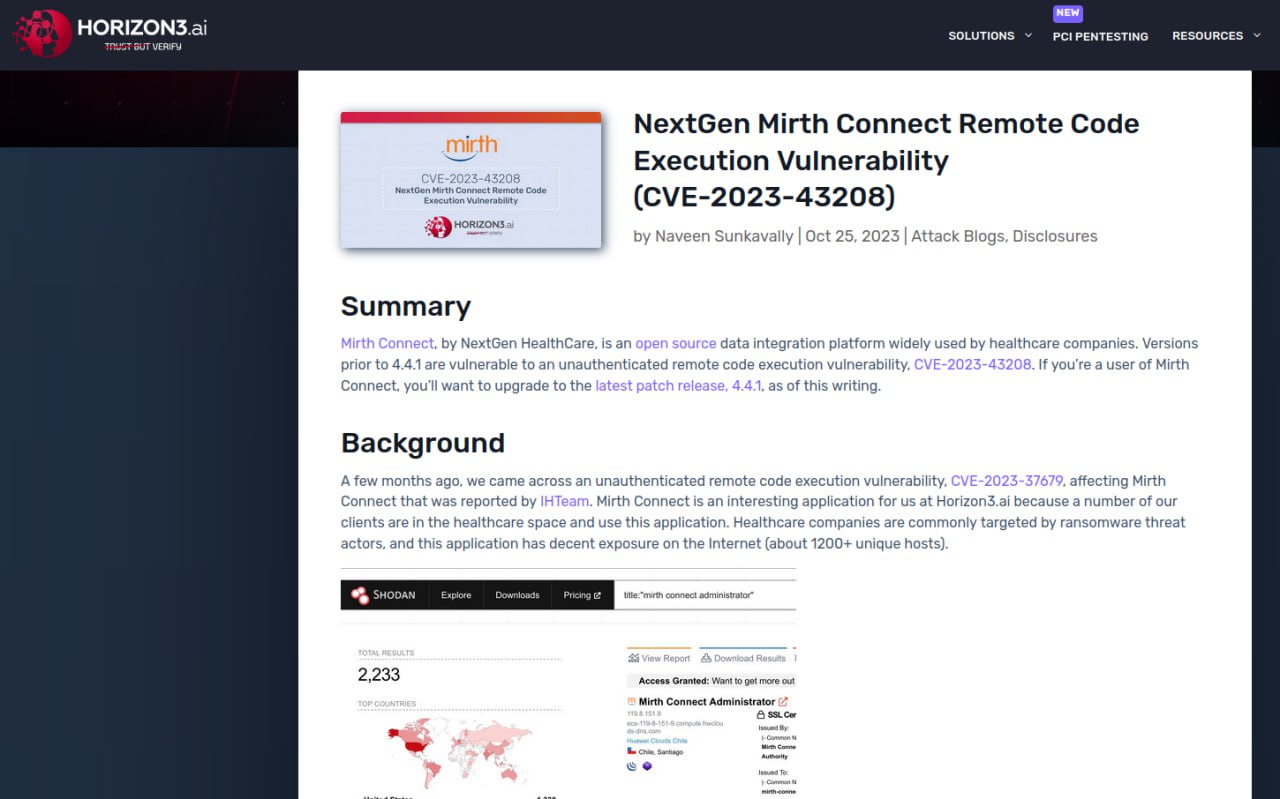
Information Disclosure vulnerability – Check Point Security Gateway (CVE-2024-24919) exploited in the wild. On May 28, Check Point released a security bulletin reporting a critical vulnerability in Check Point Security Gateways configured with the “IPSec VPN” or “Mobile Access” software blades.
📖 Almost immediately, technical details on the vulnerability appeared. The vulnerability allows an unauthenticated remote attacker to read the content of an arbitrary file located on an affected device. This allows an attacker to read the /etc/shadow file with password hashes for local accounts, including accounts used to connect to Active Directory. An attacker can obtain passwords from hashes, and then use these passwords for authentication and further development of the attack. Of course, if the Security Gateway allows password-only authentication.
🔨 Exploiting the vulnerability is trivial – one Post request is enough. There are already many scripts on GitHub for this.
👾 Attempts to exploit the vulnerability have been detected since April 7. In other words, 1.5 months before the vendor released the fixes. The vulnerability is already in CISA KEV.
Vulnerable products:
🔻 CloudGuard Network
🔻 Quantum Maestro
🔻 Quantum Scalable Chassis
🔻 Quantum Security Gateways
🔻 Quantum Spark Appliances
🔍 How many vulnerable hosts can there be? Qualys found 45,000 hosts in Fofa and about 20,000 hosts in Shodan. Most of all, of course, in Israel. Russia is not in the TOP 5 countries. Fofa shows 408 hosts for Russia. 🤷♂️
🩹 The vendor’s website provides hotfixes, a script for checking for compromise, and recommendations for hardening devices.
На русском