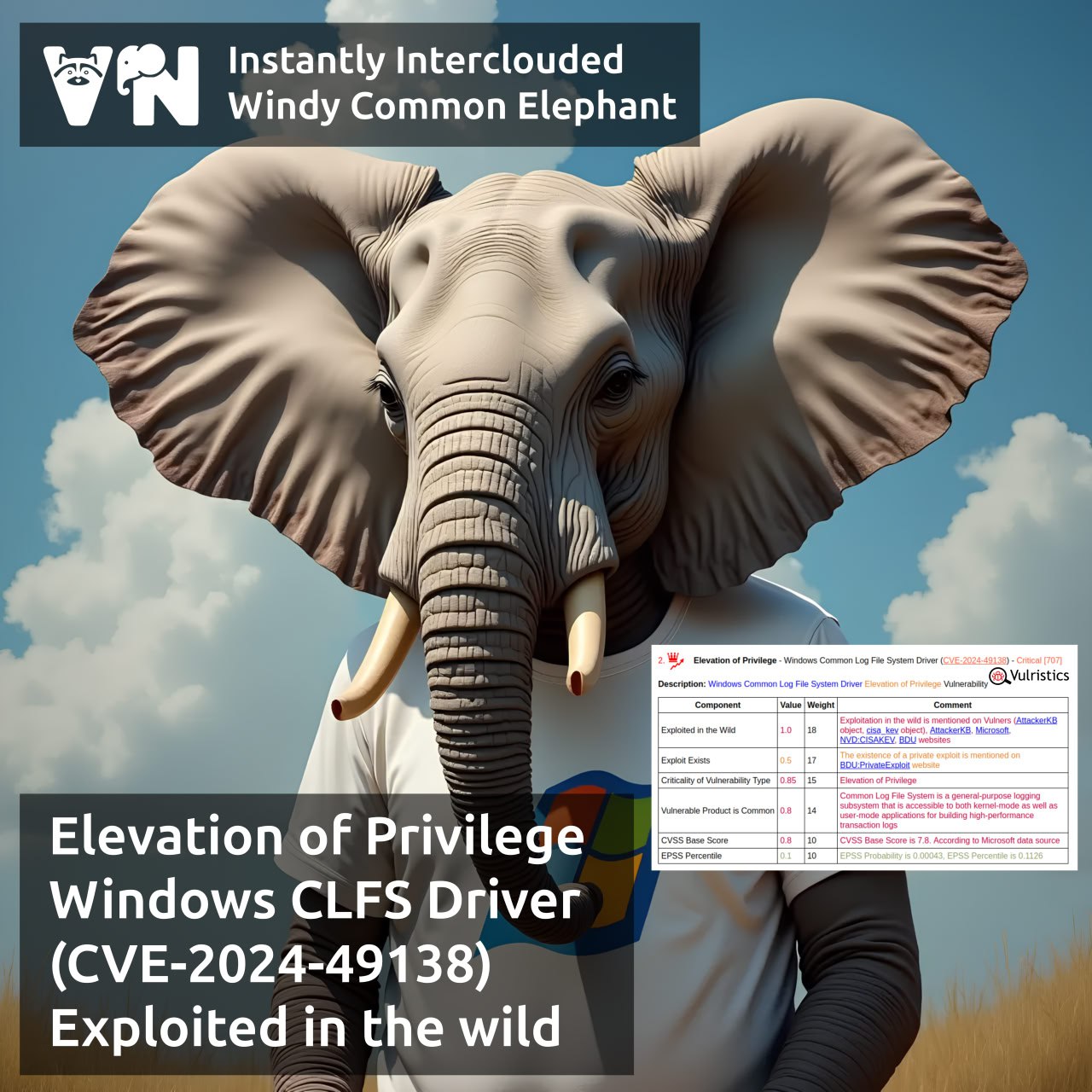
What has become known about the Elevation of Privilege – Windows Common Log File System Driver (CVE-2024-49138) vulnerability from the December Microsoft Patch Tuesday a month later? Almost nothing. 🙄 This is a vulnerability in a standard Windows component, available in all versions starting with Windows Server 2003 R2. Its description is typical for EoP in Windows: if successfully exploited, a local attacker can gain SYSTEM privileges. The cause of the vulnerability is Heap-based Buffer Overflow.
Microsoft has labeled the vulnerability as being exploited in the wild, but has not provided information on where the vulnerability was being exploited or how widespread the attacks were.
The vulnerability was reported by CrowdStrike’s Advanced Research Team. But neither they nor other researchers have provided technical details yet. 🤷♂️ And there are no exploits yet either.
So install the December Microsoft security updates and let’s wait for news! 😉