CISO Forum and the problems of Vulnerability Databases. Last Tuesday, April 24, I was at “CISO FORUM 2020: glance to the future“. I presented there my report “Vulnerability Databases: sifting thousands tons of verbal ore”. In this post, I’ll briefly talk about this report and about the event itself.

My speech was the last in the program. At the same time, in a parallel stream, there was another interesting presentation by the most famous Russian information security blogger. Thus, there was a real danger of speaking in an empty room. 🙂 But everything went well. There were about 30 spectators and we had an active QA session afterwards.
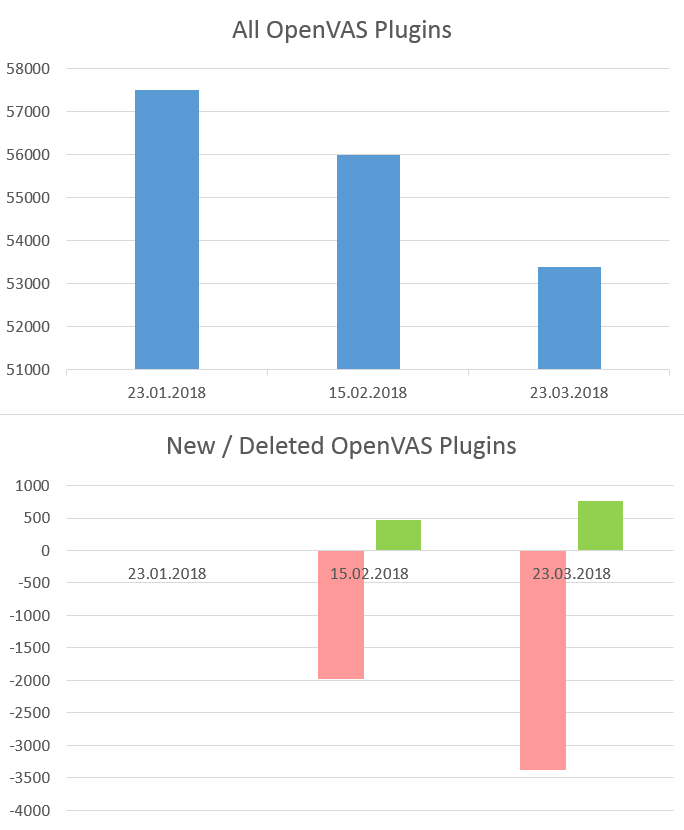
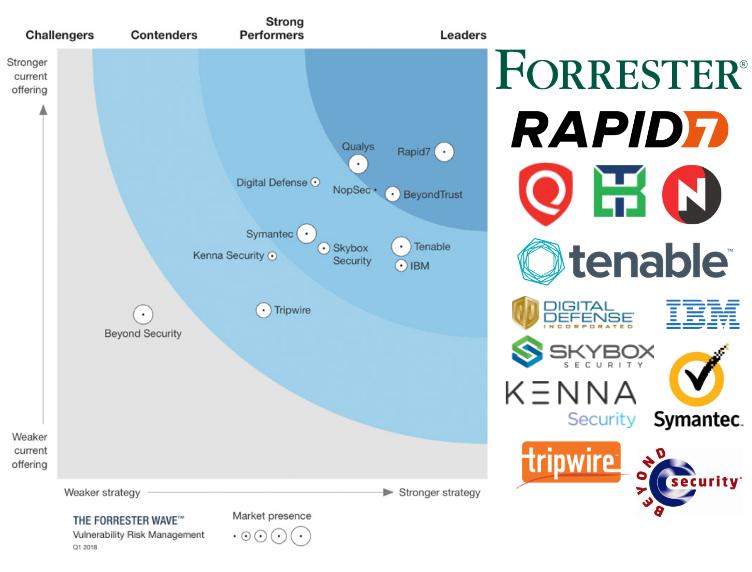
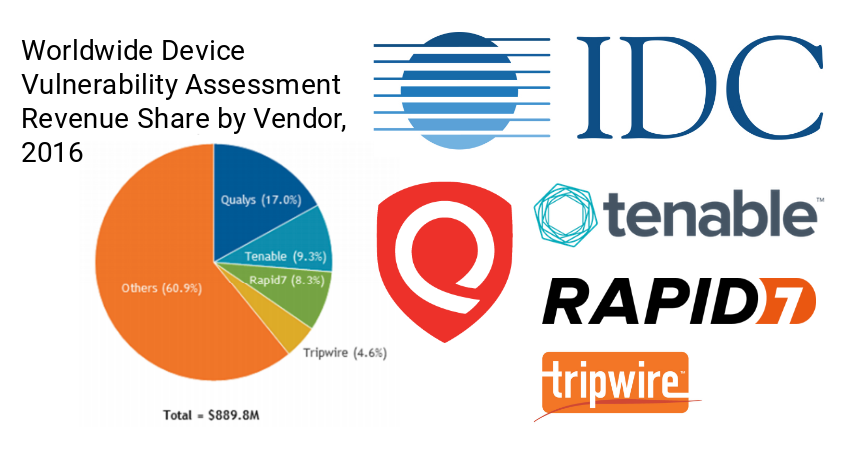
As I wrote earlier, I started preparing my CyberCentral presentation several months before the event. I did not want to tell the same story again at CISO Forum and PHDays. So I prepared 2 different presentations. At CyberCentral, I was talking about Vulnerability Scanners. And at CISO Forum I was talking mainly about Vulnerable Databases. Of course, I reused some materials, but the accents were different.