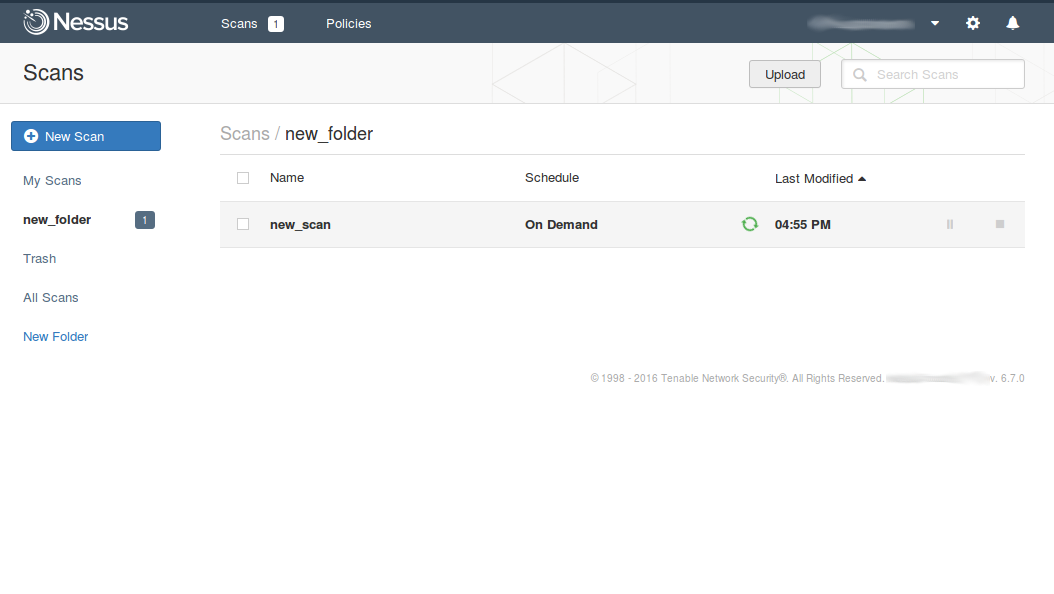
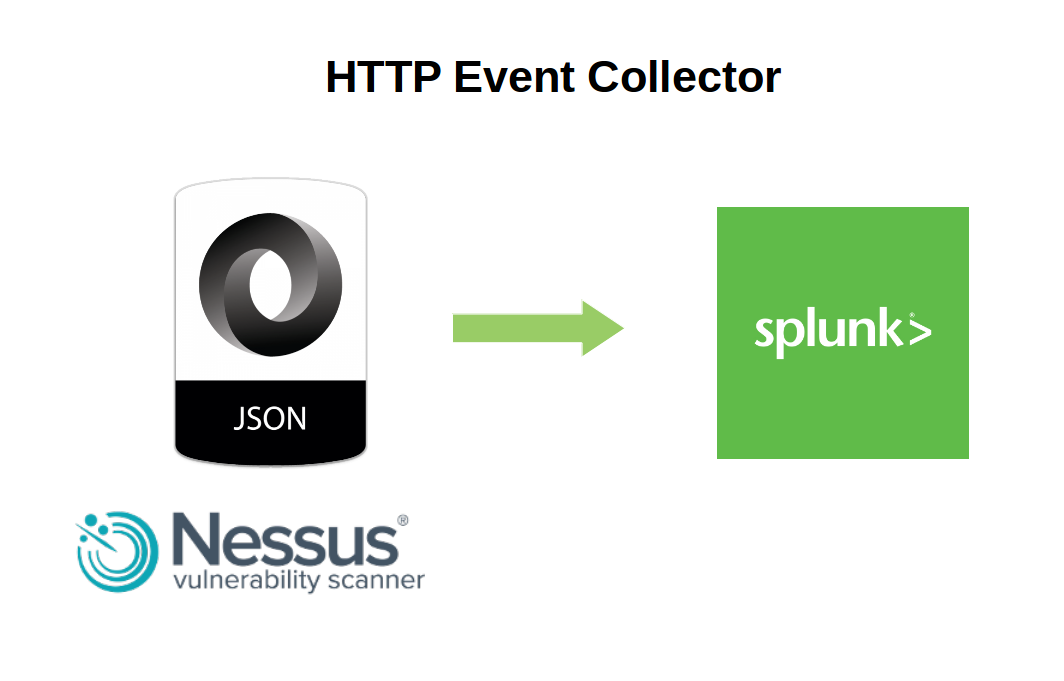
Nessus Manager and Agents. In this post I would like to share my experience with Tenable Nessus Manager. And especially how to manage agented scans with it.

First of all, I will, once again, briefly describe main editions of Nessus vulnerability management solution. Three of them, that you can deploy in your infrastructure, and one is cloud based (Nessus Cloud).
It’s of course well known Nessus Home edition, that is free for home users. Nessus Home is strictly limited by amount of IP addresses you can scan. If you try to use it in some commercial environment you might have some problems with Tenable. But for scanning some home servers and desktops, or perhaps study how vulnerability scanners work it is a really great option. You can get home license automatically after filling the registration form. I described how to register Nessus Home, configure and use it in my earlier post.
The other Nessus Professional edition is for cybersecurity professionals/individuals, who may use this product for security assessment. It is most popular version of Nessus. There is no limit in IP addresses, so you can purchase one license for Nessus Professional scanner and theoretically scan everything in your organization. The cost of the scanner is just about $2,000. Very reasonable price comparing with other competitors. It also supports multiple user accounts.
If Nessus professional does such a beautiful job, why should anybody want something else? The answer is managing multiple connected vulnerability scanners and local agents. You can configure another edition, Nessus Manager, to run scan tasks from remote connected Nessus Professional scanners. You can also configure Nessus Manager to run audit and compliance scan tasks with locally installed Nessus agents. And it is the only way to do it. Even if you’ve already purchased some expensive Enterprise Vulnerability Management product from Tenable, such as Tenable Security Center or Tenable Security Center Continuous View you still will need to pay extra ~$3,000 – $5,000 for Nessus Manager if you want to use local agents.
Nessus Cloud is like Nessus Manager but it is hosted on remote Tenable servers.
Why may you need to use local agents for scanning? The most of obvious reasons is that in this case you won’t need to manage accounts for authenticated scan. You can also check how Qualys made Agented Scanning and compare it with Tenable approach bellow.