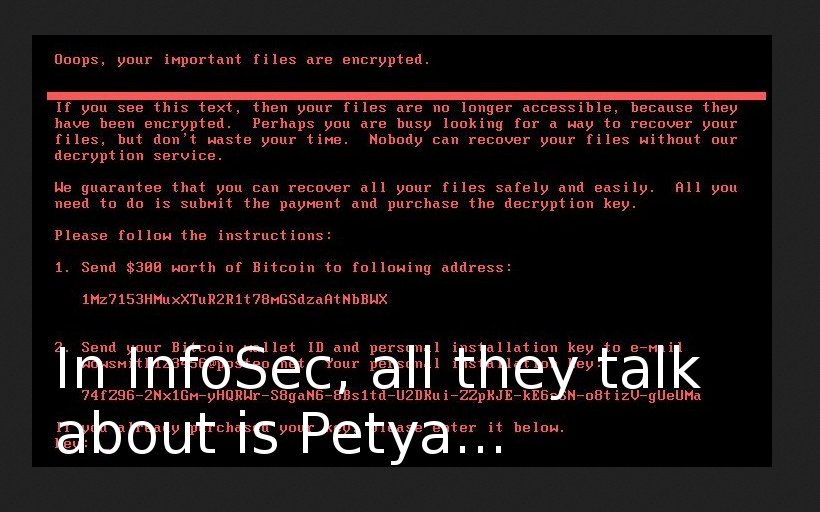
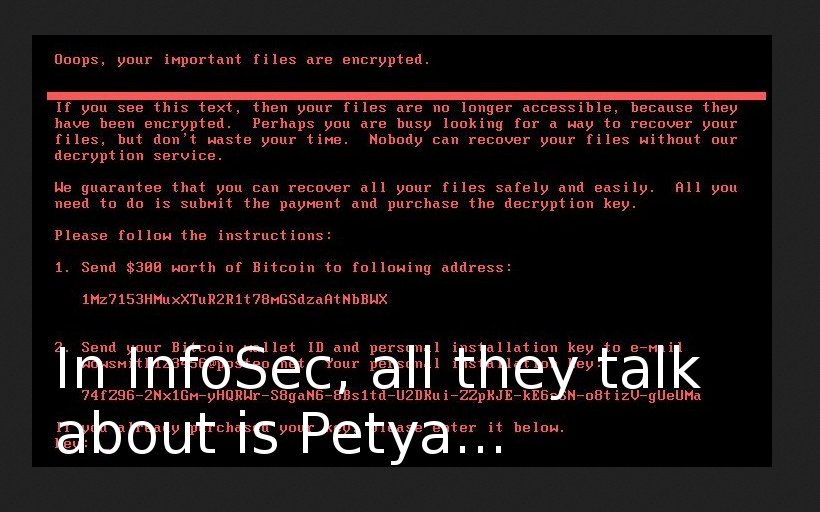
Petya the Great and why *they* don’t patch vulnerabilities. I really like this. Just imagine. Quiet, routine, everyday Vulnerability Management process in organizations: scanning-patching, scanning-patching, scanning-patching… And then. Suddenly! PEEETYYA!!!
And at very same moment everything changes. People from different companies start to communicate with each other actively, reverse this new malware, share the data, write and share tools for detection and recovery. Security professional is a friend, a brother and a source of useful information for security professional. Real movement! Real community! =)
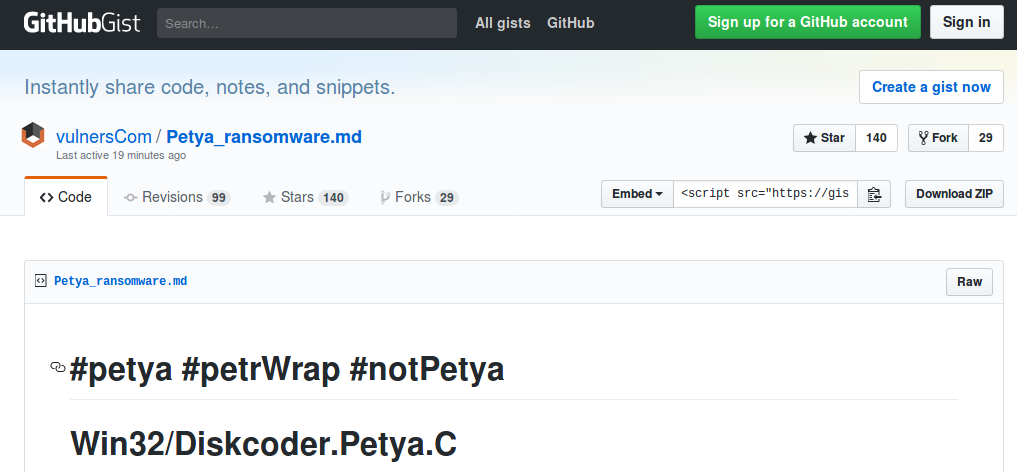
For example, my friends from Vulners.com created pretty popular gist about Petya (petrWrap, notPetya, GoldenEye) and updated in real time for several hours.
My former colleagues from Positive Technologies released detailed technical review of this ransomware (in Russian) few hours since the outbreak started, at 01:00 am . They also found a local kill switch, and probably were the first one. Simultaneously with Amit Serper from Cybereason.
Continue reading →