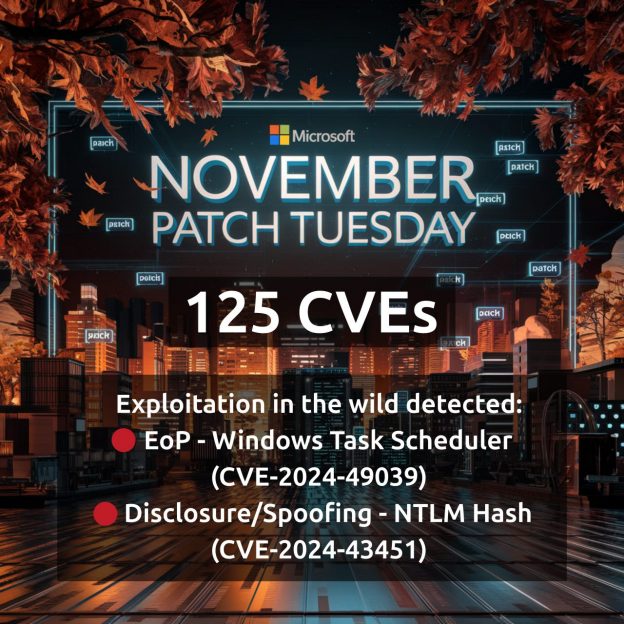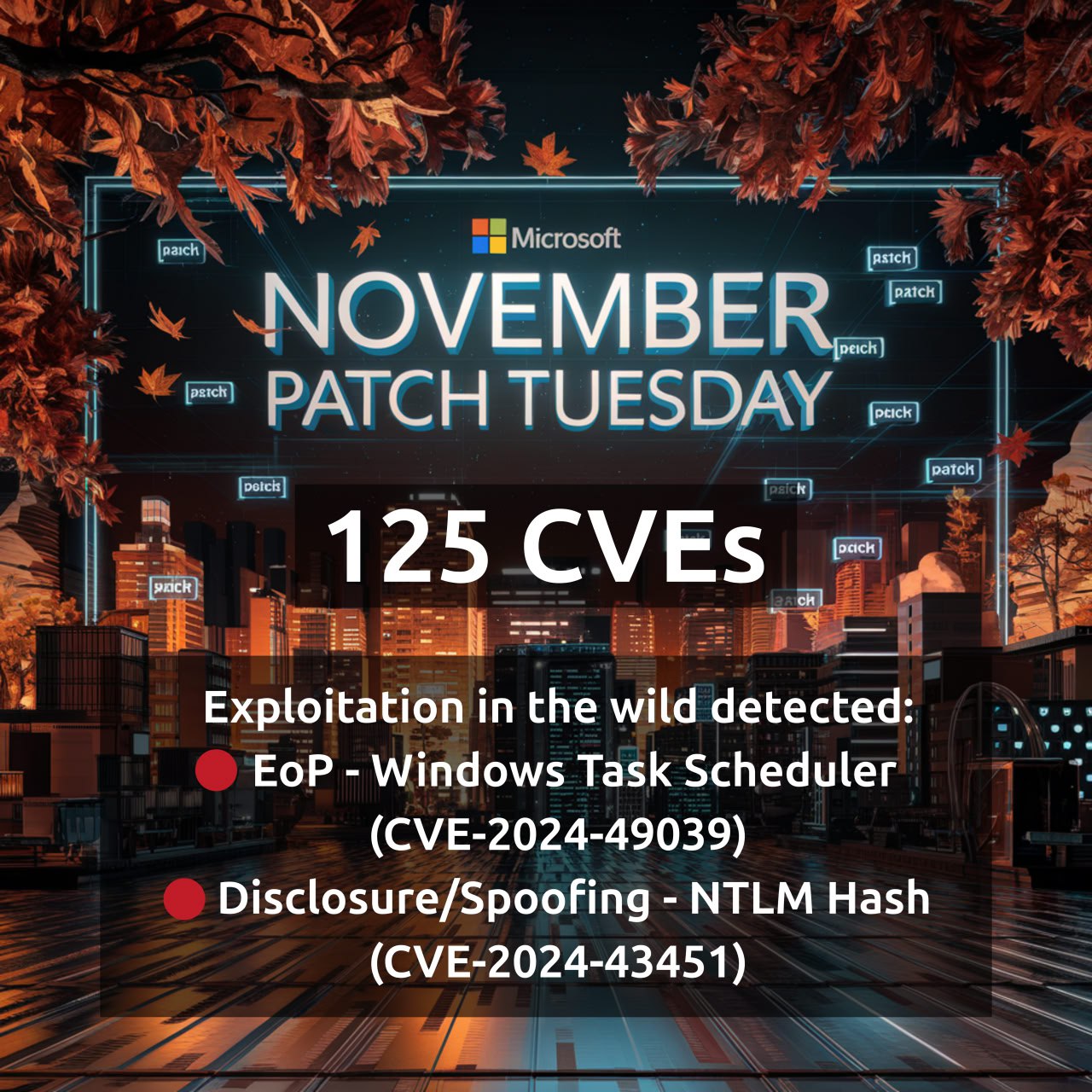
November Microsoft Patch Tuesday. 125 CVEs, 35 of which were added since October MSPT. 2 vulnerabilities with signs of exploitation in the wild:
🔻 Elevation of Privilege – Windows Task Scheduler (CVE-2024-49039)
🔻 Disclosure/Spoofing – NTLM Hash (CVE-2024-43451)
No signs of exploitation, but with a private PoC of the exploit:
🔸 Remote Code Execution – Microsoft Edge (CVE-2024-43595, CVE-2024-43596)
🔸 Authentication Bypass – Azure Functions (CVE-2024-38204)
🔸 Authentication Bypass – Microsoft Dataverse (CVE-2024-38139)
🔸 Spoofing – Microsoft Exchange (CVE-2024-49040)
Among the rest can be highlighted:
🔹Remote Code Execution – Windows Kerberos (CVE-2024-43639)
🔹Elevation of Privilege – Windows Win32k (CVE-2024-43636)
🔹Elevation of Privilege – Windows DWM Core Library (CVE-2024-43629)
🔹Elevation of Privilege – Windows NT OS Kernel (CVE-2024-43623)